Home » Publications » Security Magazine
Security Magazine
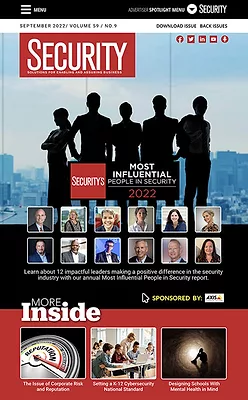
2022 September
Cover Story
Back to TopSpecial Report
This year’s Most Influential People in Security recipients represent a small cross section of people protecting their organizations, furthering their missions and elevating the security industry in significant ways.
Read More
Featured Articles
Back to TopProduct Spotlight
Mass notification and emergency communications: Security technology spotlight
September 14, 2022
Enterprise Services
Protecting utilities: Top criminal and terrorist targets
A comprehensive, layered and thorough security program is a vital component of any utility or critical infrastructure organization’s operations.
July 25, 2022
Strategic Security
The issue of corporate risk and reputation
How can a security leader build resilience and internal risk management programs to protect an organization’s reputation and, ultimately, operational continuity?
September 9, 2022
Columns
Back to TopCybersecurity Education & Training
The fundamentals of implementing a zero trust security policy
What exactly does it entail to enforce a zero trust security policy? A lot.
September 1, 2022
Leadership & Management
A chief security officer (CSO) by any other name
September 7, 2022
Career Intelligence
Are awards valuable to your security career?
Everyone enjoys a trophy but it’s important for security professionals to do their due diligence before accepting.
September 7, 2022
Cyber Tactics
Flaming torches and cybersecurity
Being a security leader while juggling business priorities and daily operations is a challenge that requires pragmatic solutions.
September 6, 2022
Security Talk
Designing schools with mental health in mind
Safety and security stakeholders can empower students and staff to help mitigate mental health issues, violence or unwanted behaviors by starting with facility design.
September 6, 2022
Departments
Back to TopSign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing


















