Leadership & Management
A chief security officer (CSO) by any other name

Prostock-Studio / iStock / Getty Images Plus via Getty Images

No less a word wizard than Shakespeare said that a rose by any other name would smell as sweet. But would “The Bard” himself agree that a Chief Security Officer (CSO) by any other name would retain the same authority, respect and gravitas?
About two decades ago, the security profession staked its claim to the C-suite by adopting and popularizing the CSO title, but the term has faced challenges. If you tell anyone outside of security that you are a CSO, they may well guess that you are a strategy officer, a sales officer or you lead an organization’s scientific or sustainability efforts. Even if they surmise correctly that you are in security, they might conclude that you own cybersecurity only.
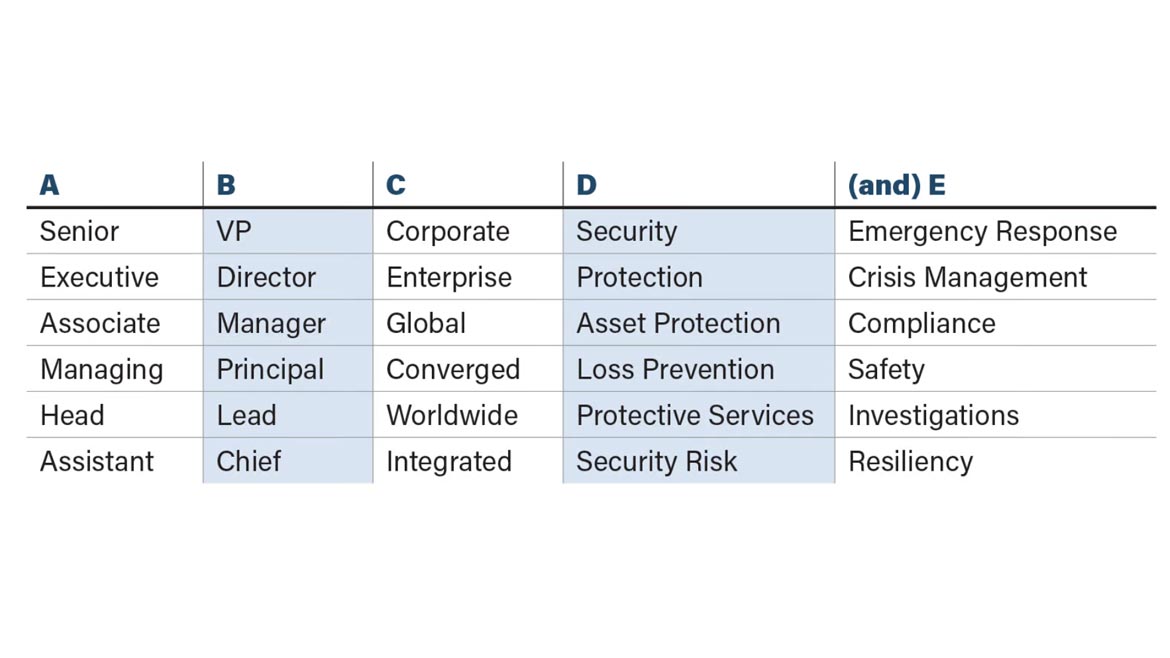
What’s more, CSO may not even be the most popular term for an organization’s senior security executive. Hundreds of different titles populate the corporate landscape. In fact, you can create your own with this handy senior security title generator. Simply pick one term from each column.
We haven’t come very far in naming conventions in the last 20 years. Likewise, progress has been marginal in standardizing a CSO’s duties, responsibilities and authority.
In an article written by Steve Hunt almost 20 years ago, he wrote, “The role of the chief security officer (CSO) has burst onto the corporate scene in North America and Europe in the last two years. Today, there are more than 200, but their respective job descriptions, reporting structures, qualifications and compensation are wildly diverse.” A mere review of today’s titles still bears out this reality.
Acknowledging that the CSO term hasn’t pushed other job titles out of the market, ASIS International (ASIS) has renamed its Chief Security Officer standard the Senior Security Executive (SSE) standard. As a member of the group that reimagined and redrafted that standard from its 2013 iteration, I can attest to differences of opinion on whether to keep the original name or go generic. Not everyone was ready to abandon CSO for SSE.
In my view, this was a strategic choice to emphasize the substance and purpose of the standard over its titular significance. For example, the new document accentuates the central role of Enterprise Security Risk Management (ESRM) in a CSO’s role and responsibilities. In addition, it incorporates, by reference, the security competency model created by ASIS, the Apollo Group, and the University of Phoenix and endorsed by the U.S. Department of Labor.
Moreover, the updated standard better positions the CSO as a critical business partner and advisor to other senior executives. Here is the key language from the executive summary:
"The SSE takes a holistic view of security and the organization’s operations to establish and implement effective protective strategies across various functions to support asset protection and organizational effectiveness. Accordingly, the [Senior Security Executive] coordinates with other organizational functions to develop, implement, and manage policies, plans and procedures that establish organizational responses across the broad spectrum of business and organizational risks."
Maybe the question isn’t whether the SSE title smells as sweet as CSO does, but whether heads of security pass the sniff test when interacting with their organizational peers. Following the updated standard can help them pass that test.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





