Global News
Video surveillance cameras optimize security operations

Jay_Zynism / iStock / Getty Images Plus via Getty Images
From businesses to schools and communities, how are organizations around the globe deploying security cameras in a cloud-based video management system (VMS)?
In its annual report on security cameras, Eagle Eye Networks (EEN) aggregated data from a sample of 200,000 security cameras worldwide over the past six years from more than 1,000 organizations in several different markets, including retail, restaurants, warehouses, commercial enterprises, multi-family residence, healthcare, hospitality, logistics, K-12 schools and cities.
The report reveals security trends and insights as to how organizations decide on the number and locations of their cameras to improve safety and security operations.
Video Recording Location
Sixty percent of cameras are used for cloud-only video recording, while 40% combine a mix of cloud and on-premises recording. There was an increase in the number of larger enterprises moving to cloud video surveillance in 2021; the higher number of security cameras in each building for larger enterprises requires more onsite storage due to bandwidth limitations.
The shift resulted in a slight increase in the percentage of organizations deploying mixed-cloud plus on-premises video recording compared with last year’s data. The percentage of cameras with combined-cloud and on-premises recording (versus cloud-only recording) increased between 2016 and 2019 and has been fairly stable over the past three years.
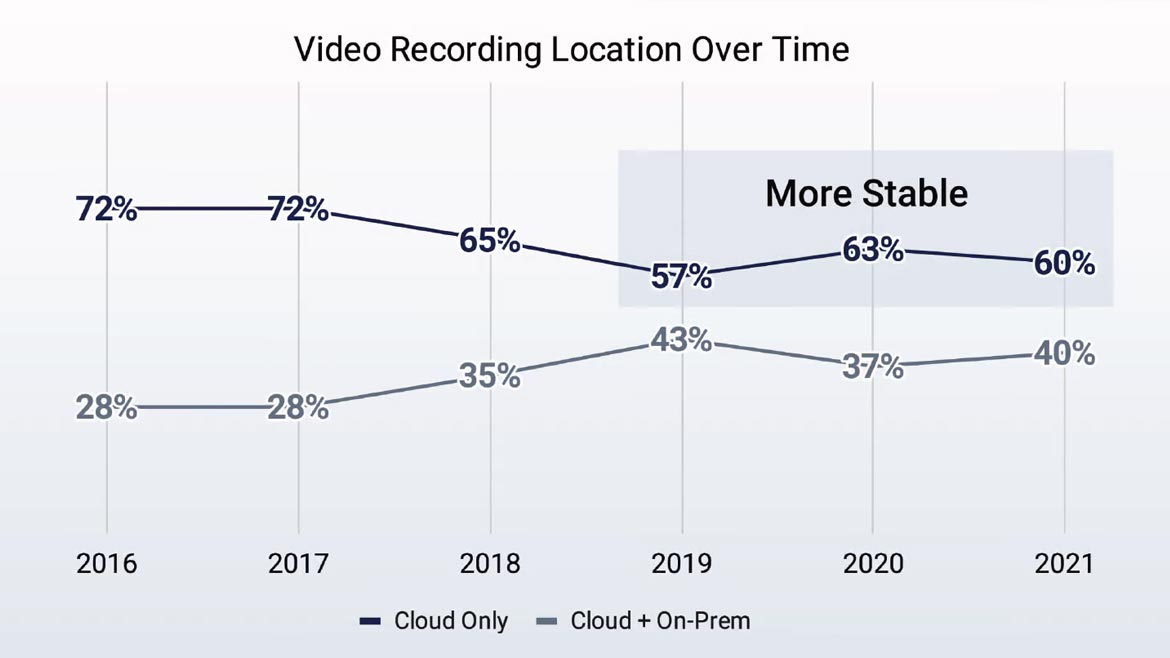
Image courtesy of EEN
1. Cloud Recording Retention
The average cloud recording retention in 2021 was 29 days, only slightly higher than the 28.2 day cloud retention from last year’s report. The most common cloud retention was 30 days. Moreover, 43% of respondents said their cloud recording was 30 days, 31% said 1 to 7 days, 15% said 14 days, 10% said 60 to 180 days, and 1% said 1 to 7 years.
Although there is variation, for 180 days retention and above, highly represented sectors include medical, educational institutions, financial, government, hospitality and multi-unit residences. More regulated industries, such as banking, law enforcement and the cannabis industry, generally require longer retention, with some contract recordings requiring a full seven years.
2. On-Premises Recording Retention
The average on-premises recording retention was stable at 33 days. The dominant retention choice was 30 to 60 days for 78% of respondents. In addition, 20% said their choice for on-premises recording retention was 90 to 180 days; 1% said 7 to 14 days and an additional 1% said 365 to 480 days.
Audio Recording
The percentage of audio recording-enabled security cameras has doubled over the past five years, with 7% of cameras installed in 2021 using audio recording — the same percentage of cameras installed in 2020.
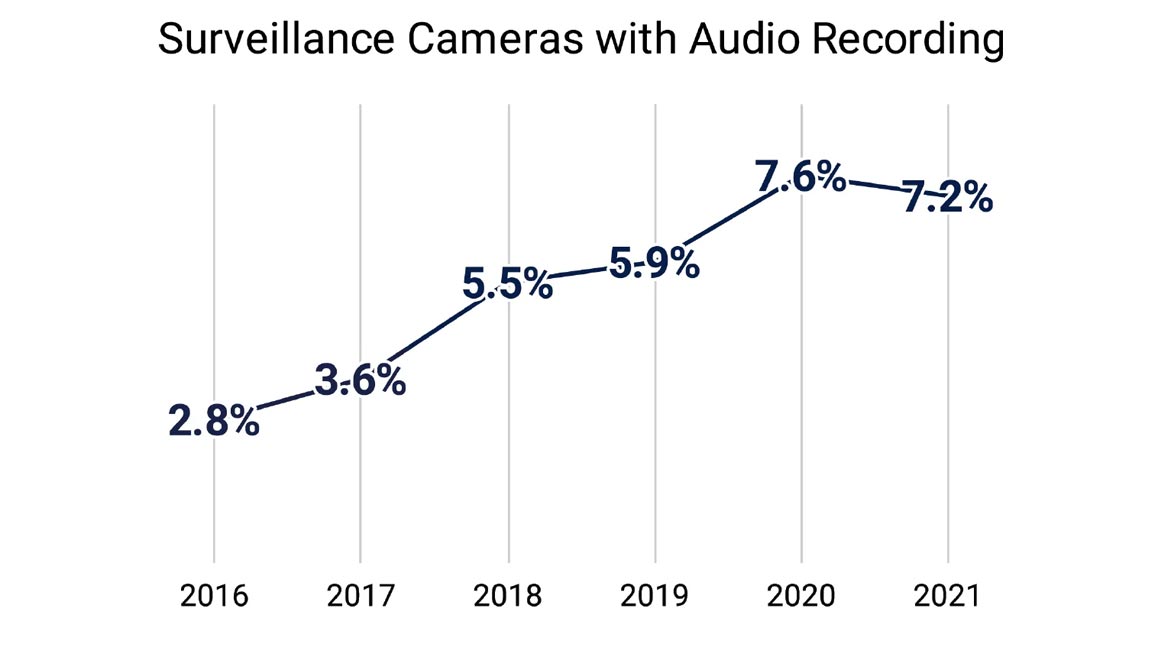
Image courtesy of EEN
Top Security Analytics
Security camera video analytics track and provide real-time alerts to particular events. They can also be used to search forensically for events that have already occurred. The report examined the four most common physical security analytics to determine their relative level of use.
The four most commonly used security analytics, according to respondents are:
- Intrusion: Flags when someone enters a designated area; typically associated with areas that are considered off limits.
- Crossing: Identifies whether a person or vehicle crosses a marked line; commonly tied to people entering a store and can also be used for an unsafe area.
- Counting: Counts the number of people in an area; typically used to monitor service quality or for safety reasons.
- Loitering: Determines if an individual or group stays beyond a specified time in a particular area and can indicate suspicious behavior.
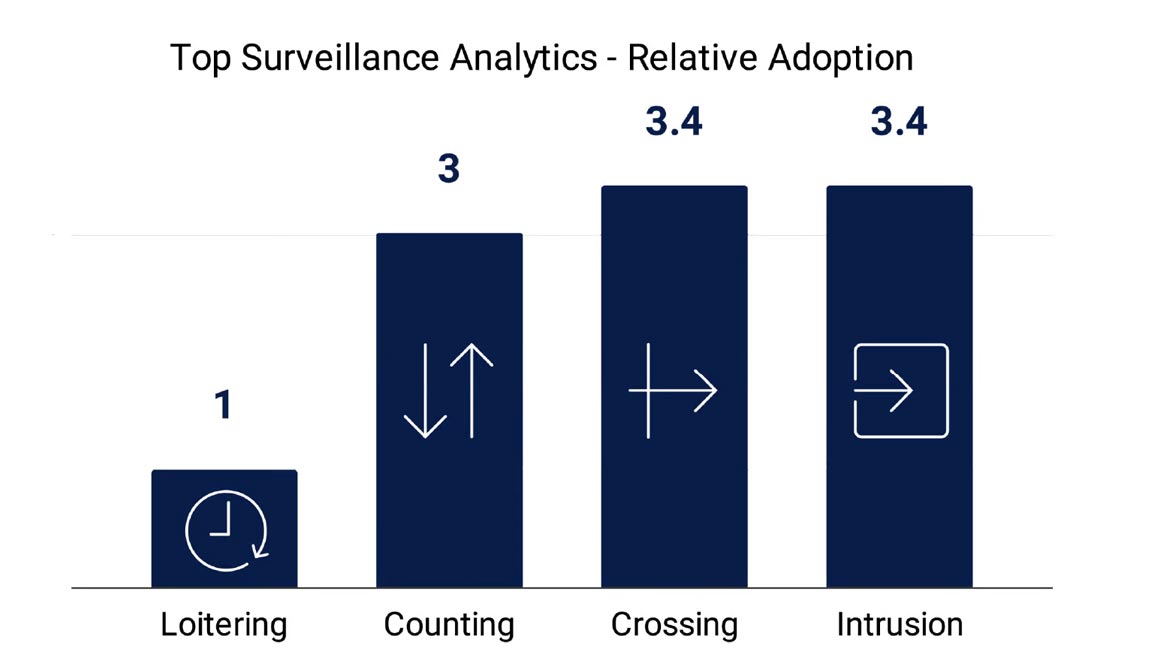
Image courtesy of EEN
This year, crossing analytics caught up with intrusion for a two-way tie for the most deployed analytics, closely followed by counting analytics. Loitering remained the least-used application, with deployment levels one-third or less compared to the others.
The more recent artificial intelligence-based analytics available in the market, including license plate recognition and traffic monitoring, are still in earlier stages of adoption and did not show up in this study with a significant level of response.
The report can be helpful for security leaders and their organizations looking for insights on moving to cloud-based video surveillance camera systems.
For the full report, visit www.een.com.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








