Product Spotlight
Security technology at GSX 2022

The Global Security Exchange (GSX) conference, taking place September 12-14 in Atlanta, will include an exhibit hall packed with innovative security solutions, featuring new products for video surveillance, access control, incident management, perimeter security and more.
As GSX nears, Security magazine has a roundup of some of the security products, technologies and services that security management professionals may discover at the event.
Aiphone
Helps Screen Visitors and Improves Security Measures for Multi-tenant and Commercial Spaces

Aiphone added the IXG-MK IP Video Guard Station to its IXG Series Multi-Tenant Video Intercom System. The IXG-MK provides visitors a way to call a building’s concierge, receptionist or security guard directly from the entrance station, to help when visitors are unsure how to reach a tenant or if they are trying to deliver a package to the front desk. Once safe intent has been determined, calls can then be transferred to the proper apartment or suite or the door unlocked for deliveries. This solution offers enhanced perimeter security measures. Image courtesy of Aiphone
Find out more at www.aiphone.com
ASSA ABLOY
Protects Data and Security Equipment
 The HES KS Series Server Cabinet Locks from ASSA ABLOY work with existing access control systems to help protect server racks from intrusion. Four cabinet locks aim to secure data and other assets in various ways: the KS200/210 model is an integrated wired swing handle server cabinet lock; the KS200 utilizes a Wiegand interface; the KS210 uses native RS-485 OSDP communication; and the KS-M is a mechanical server cabinet lock and can be installed on most cam-activated server cabinet doors. Image courtesy of ASSA ABLOY
The HES KS Series Server Cabinet Locks from ASSA ABLOY work with existing access control systems to help protect server racks from intrusion. Four cabinet locks aim to secure data and other assets in various ways: the KS200/210 model is an integrated wired swing handle server cabinet lock; the KS200 utilizes a Wiegand interface; the KS210 uses native RS-485 OSDP communication; and the KS-M is a mechanical server cabinet lock and can be installed on most cam-activated server cabinet doors. Image courtesy of ASSA ABLOY
Find out more at www.hesinnovations.com
Axis
Improves Perimeter and Parking Security
 The Axis D4100-E Network Strobe Siren helps to deter intruders, ensure onsite safety and improve operational efficiency using light and sound. Integrated through VAPIX, MQTT or SIP, the device comes with various light and sound patterns to ensure the right level of protection for specific environments. The fully networked product can be connected to any Axis device, Axis VMS, or to third-party video management systems and issue warnings and notifications with strobe lighting and/or siren alarms. It can be used for perimeter protection, with the addition of thermal and radar cameras, or for improved parking entrance management with a license plate recognition camera. Image courtesy of Axis
The Axis D4100-E Network Strobe Siren helps to deter intruders, ensure onsite safety and improve operational efficiency using light and sound. Integrated through VAPIX, MQTT or SIP, the device comes with various light and sound patterns to ensure the right level of protection for specific environments. The fully networked product can be connected to any Axis device, Axis VMS, or to third-party video management systems and issue warnings and notifications with strobe lighting and/or siren alarms. It can be used for perimeter protection, with the addition of thermal and radar cameras, or for improved parking entrance management with a license plate recognition camera. Image courtesy of Axis
Find out more at www.axis.com
Boon Edam
Keeps Intruders Out and Users Safe
 The Tourlock 180 and Tourlock 120 revolving door models have been relaunched by Boon Edam. Both models are compliant with the European Standard EN 17352, which specifies requirements and test methods for pedestrian entrance control equipment. These doors have been updated to provide security protection through anti-tailgating and piggybacking functions. The Tourlock 180 and Tourlock 120 are equipped with an emergency stop button; buffers to protect user hands and feet while using the technology; instructional safety information; and features that help avoid entrapment. Image courtesy of Boon Edam
The Tourlock 180 and Tourlock 120 revolving door models have been relaunched by Boon Edam. Both models are compliant with the European Standard EN 17352, which specifies requirements and test methods for pedestrian entrance control equipment. These doors have been updated to provide security protection through anti-tailgating and piggybacking functions. The Tourlock 180 and Tourlock 120 are equipped with an emergency stop button; buffers to protect user hands and feet while using the technology; instructional safety information; and features that help avoid entrapment. Image courtesy of Boon Edam
Find out more at www.boonedam.com
Bosch
Monitors Traffic in Various Lighting Conditions

Bosch’s Traffic Detector software aims to detect, classify and locate vehicles in busy traffic situations under challenging lighting conditions. The program uses AI to help improve detection capabilities in congested scenes and accurately count multiple vehicle subclasses. The software also has the ability to count people. Traffic Detector software has been deployed on Bosch’s Inteox fixed and moving object classification (OC) camera models. The program’s AI algorithms are trained to ignore potential disruptions caused by vehicle headlights or shadows, extreme weather and sun reflections. Image courtesy of Bosch
Find out more at www.boschsecurity.com
Brivo
Eliminates Insecure Proximity Cards
The Brivo Unified Credential by Brivo is a cross-platform smart credential that is compatible with select wireless locks and Brivo Smart Readers to improve security while leveraging existing door locks and devices. Brivo Unified Credential allows property owners and managers to issue a single keycard or fob that operates with Brivo Smart Readers and select Schlage locks and battery-powered Aperio locks from ASSA ABLOY. Brivo Unified Credential is built on 13.56 MHz, MIFARE DESFire EV2 using the LEAF application. The solution works with partners using a common Brivo configuration across the integrated devices. Image courtesy of Brivo
Find out more at www.brivo.com
Eagle Eye Networks
Streamlines Parking Operations and More
The Eagle Eye LPR (license plate recognition) by Eagle Eye Networks uses artificial intelligence (AI) in a true cloud-based system for high accuracy in all kinds of challenging conditions. Eagle Eye LPR operates on available security cameras and works with the Eagle Eye Networks Vehicle Surveillance Package (VSP) to enable monitoring of vehicles across multiple locations. In addition, the system works with nearly any IP or analog camera and is reportedly accurate, even in challenging lighting and environmental conditions. The LPR is continually improved to support new license plates. Image courtesy of Eagle Eye Networks
Find out more at www.een.com
Everbridge
Combines Real-Time Risk Event Protection and Integrated Response
Everbridge’s Critical Event Management leverages Visual Command Center to enable security and operations professionals to partner with other business leaders and support resiliency during emergencies. Supply chain stakeholders can gain context with intelligence from other sources that may help in assessing threats related to weather, traffic, hurricane evacuation routes, global ports, railways, shipping lanes and more. In addition to Visual Command Center, applications within the platform can include safety connection, mass notification, incident communication and IT alerts. Image courtesy of Everbridge
Find out more at www.everbridge.com
Evolv
Improves Venue Operations and Visitor Experience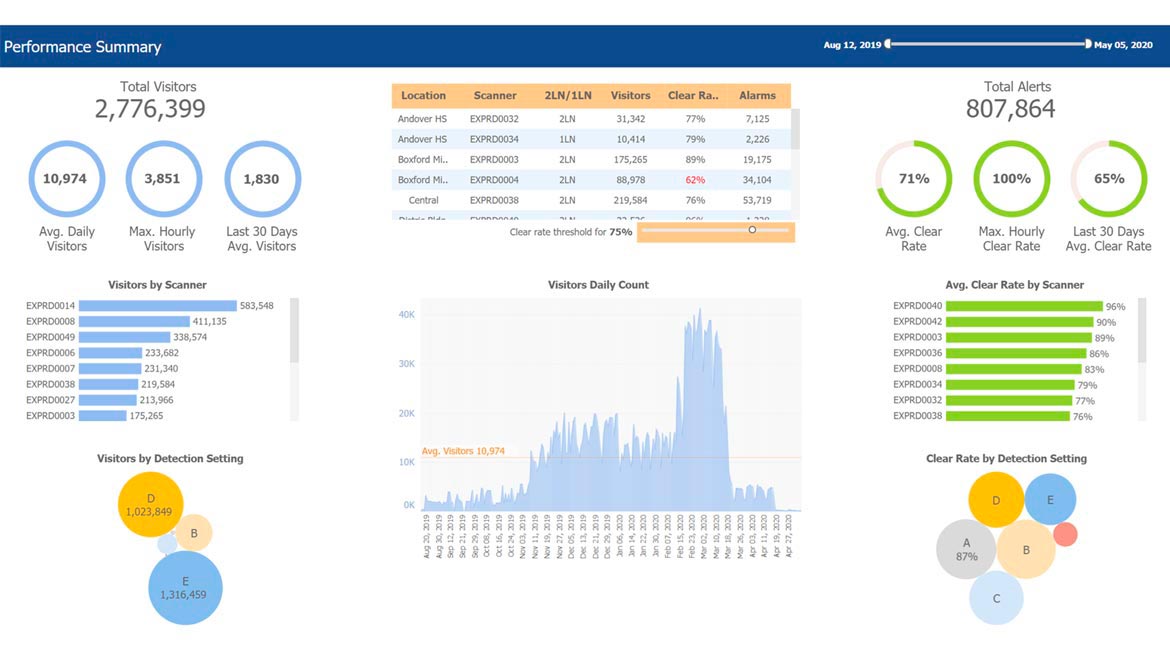
Evolv Express is a weapons detection system that combines sensor technology with AI, security ecosystem integrations and venue analytics to ensure safe threat detection at high speed. The solution can capture visitor rates, alarm rates and threat types detected at every venue entrance, making this data available across multiple business dimensions — date, time, location, entrance and event type — in the Evolv Insights analytics platform. With this feature, security staff at venues can deploy guards when and where they are needed. Image courtesy of Evolv
Find out more at www.evolvtechnology.com
Genetec
Helps Migrate Surveillance Data to the Cloud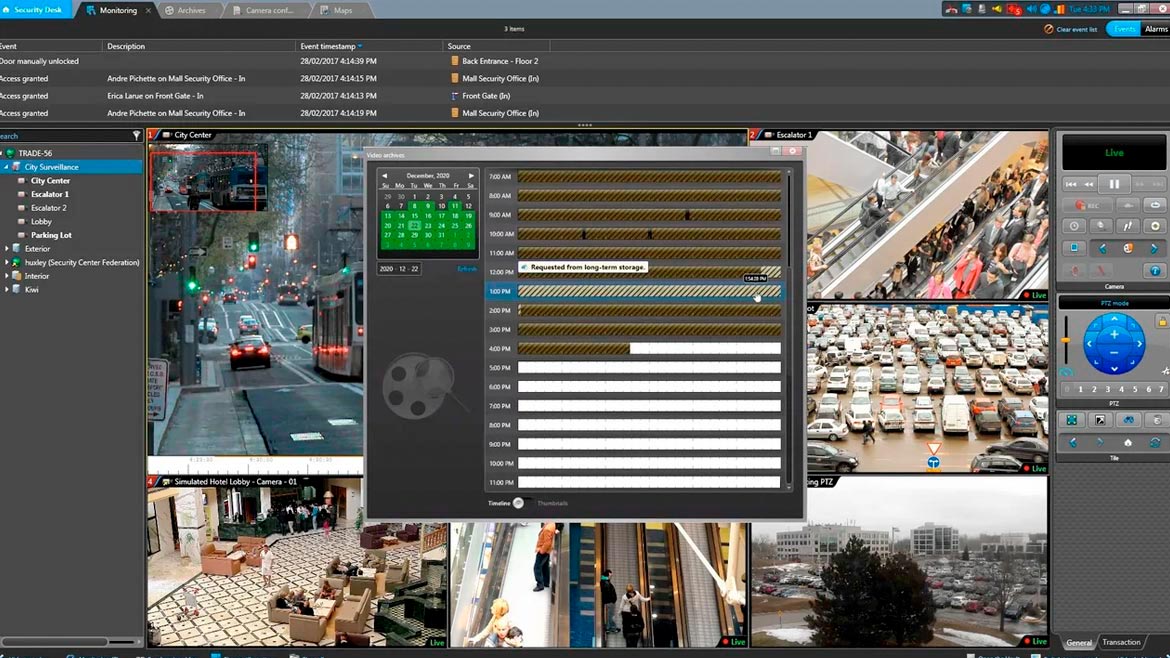
The 5.10 version of Genetec’s Security Center brings enterprise video surveillance users options to facilitate their migration to the cloud and support flexible hybrid-cloud architectures. Security Center Omnicast — the video management system of Security Center — can store video archives in the cloud and on-premises. Ingested video blocks are encrypted on-premises and then moved to the cloud using encrypted communications channels. Security Center 5.10 uses a no-code solution to connect external data sources. Users can define record types and consume data from a variety of sources, including KML, JSON and CSV documents or set up a REST application listening point to which these external services can push records. Image courtesy of Genetec
Find out more at www.genetec.com
Hanwha Techwin
Video Surveillance With Security Capabilities

Hanwha Techwin expanded its Wisenet Q Series of bullet and dome cameras with a National Defense Authorization Act (NDAA)-compliant model offering system installation and configuration, especially in video surveillance applications. The QNO-7012R 4MP IR Bullet Camera is equipped with an Open Platform chipset for integration with third-party systems and solutions, and analog video output (CVBS) support for camera positioning during installation. A suite of onboard video analytics covers tampering, directional/virtual line detection, defocus detection, enter/exit, and motion detection. Wide Dynamic Range (WDR) allows the cameras to perform at up to 120dB to produce clear images from scenes containing a challenging mix of bright and dark areas. Image courtesy of Hanwha Techwin
Find out more at www.hanwhasecurity.com
HID Global
Protects User Privacy With Encryption and Authentication
HID Global’s MIFARE DESFire EV3 features AES128 encryption, a secure channel for protecting card data from man-in-the-middle attacks, and a random unique identifier (UID) for protecting user privacy. The credential works with readers based on MIFARE DESFire EV1 and EV2 products and is interoperable with other product offerings. Users can choose standard or custom security profiles to meet their specific needs, while protecting a credential’s identity data through key diversification, authentication signatures and encryption. Users can create multi-technology cards with HID’s credential based on NXP MIFARE DESFire EV3 to provide a migration path from legacy systems to modern and secure credential technology. Image courtesy of HID Global
Find out more at www.hidglobal.com
Honeywell
Combines Video Capabilities With Access Control and Alarm Monitoring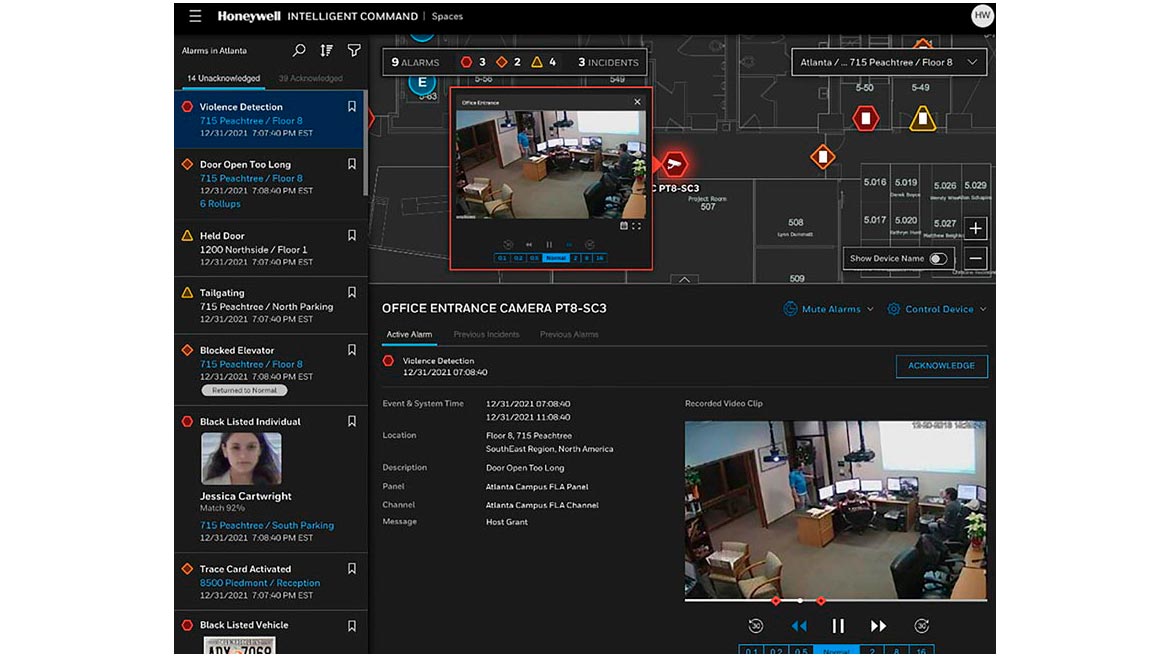
Pro-Watch 5.5 is the latest iteration of Honeywell’s Pro-Watch Integrated Security Suite, a software platform designed for enterprise and critical infrastructure markets to protect people and property, optimize productivity and ensure compliance with industry regulations. The security software can help reduce security risks and provide a unified view of alarms and maps, incident workflows and a space/area builder to create logical zones and group-based multisite views. Image courtesy of Honeywell
Find out more at www.honeywell.com
March Networks
Detects People and Vehicles
March Networks news ME8 Series IP Cameras uses Deep Neural Network processing power to accurately detect both people and vehicles. This built-in intelligence is combined with security analytics and 4K high-definition (HD) resolution for detailed video and real-time detection of events. The ME8 Series’ AI-powered video analytics enable organizations to enhance security in both public and private spaces by detecting atypical activity more rapidly and consistently. Using this built-in video intelligence, users can quickly respond to incidents such as building or zone intrusions, the abandonment of suspicious objects, and loitering and perimeter breaches by people and vehicles. Image courtesy of March Networks
Find out more at www.marchnetworks.com
Milestone Systems
Secures Complex or Simple Facility Setups With Video Management Series
With the Husky appliances series, Milestone Systems offers users a range of six video management appliances that cover a variety of use cases from simple setups in small sites, including retail, all the way to larger and more complex installations, like critical facilities. The Husky series offers service and support with a single point of contact for both hardware and software, along with the possibility to access onsite support through a global support network. Image courtesy of Milestone Systems
Find out more at www.milestonesys.com
OnSolve
Identifies Active Incidents and Sends Emergency Alerts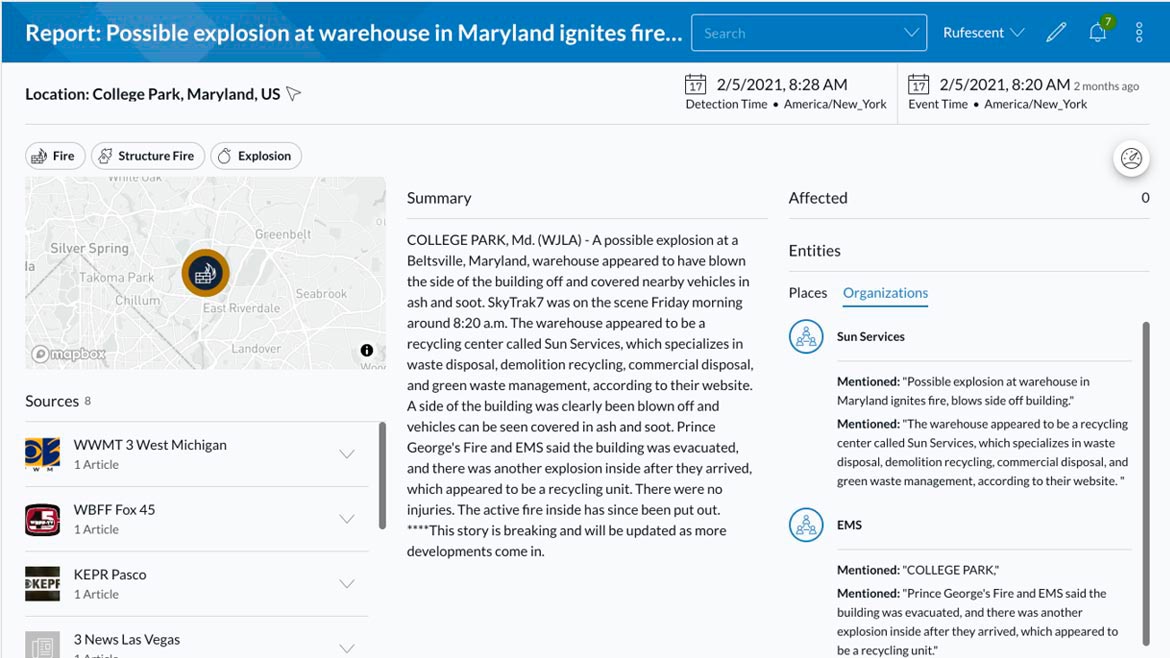
The OnSolve Platform for Critical Event Management (CEM) uses an AI engine to identify active emergencies and notify personnel. The OnSolve CEM platform adds more than 450 integrations to users’ existing physical security, business continuity and IT management ecosystems with its suite of products: OnSolve Risk Intelligence, Critical Communications and Incident Management. Through the OnSolve integration engine, users can orchestrate tasks such as wellness checks and alerts to impacted areas; disable building access; and trigger appropriate tests based on sensor data such as temperature drops, water levels, electrical current detection or gunshot/monitor detection. Image courtesy of OnSolve
Find out more at www.onsolve.com
Ontic
Helps With Security Investigations
Ontic’s Incidents, Investigations and Case Management solution is a purpose-built destination for corporate security and investigation teams who are tasked with researching and managing cases. The solution helps organizations see the full picture to properly record details and find connections. Key features include integrated research capabilities, customized access roles to maintain privacy and support compliance requirements, flexible report dashboards, easily accessible historical data, connected threat assessment workflows, and more. These capabilities help organizations recognize potential threats and take necessary action. Image courtesy of Ontic
for corporate security and investigation teams who are tasked with researching and managing cases. The solution helps organizations see the full picture to properly record details and find connections. Key features include integrated research capabilities, customized access roles to maintain privacy and support compliance requirements, flexible report dashboards, easily accessible historical data, connected threat assessment workflows, and more. These capabilities help organizations recognize potential threats and take necessary action. Image courtesy of Ontic
Find out more at www.ontic.com
i-PRO
Surveils Areas With AI-Enhanced Video and Sound
The i-PRO S-series line of network cameras comes with a built-in artificial intelligence (AI) processor that transforms the camera into an edge-computing device to help improve surveillance operations and offer the ability to select and install third-party applications without a cloud- or server-based connection. Surveillance videos captured by the cameras are encoded as H.265 files, aiming to conserve network bandwidth and server storage capacities. Sound classification technology can allow users to set alarms for targeted sounds, such as gunshots, yelling, vehicle horns and glass breaking using an external microphone. The i-PRO S-series is compatible with i-PRO’s multi-AI system, a search function that finds people or vehicles through video management software. Image courtesy of i-PRO
Find out more at www.i-pro.com
Par-Kut
Secures Access Control Points in Style
After a marina experienced repeated break-ins and theft, Par-Kut designed the 86PREZ-19192 security booth, a 6 by 8-foot structure with ballistic glass and a sliding communication window for the security officer to verify permissions to enter a facility. The booth has a standing-seam metal roof, decorative window mullions and wall treatment and exterior LED lighting. Heating and cooling were provided to ensure the insulated welded steel guardhouse would be a comfortable work environment during peak and shoulder seasons. Image courtesy of Par-Kut
Find out more at www.parkut.com
Resolver
Gain Corporate Security Insights for Incidents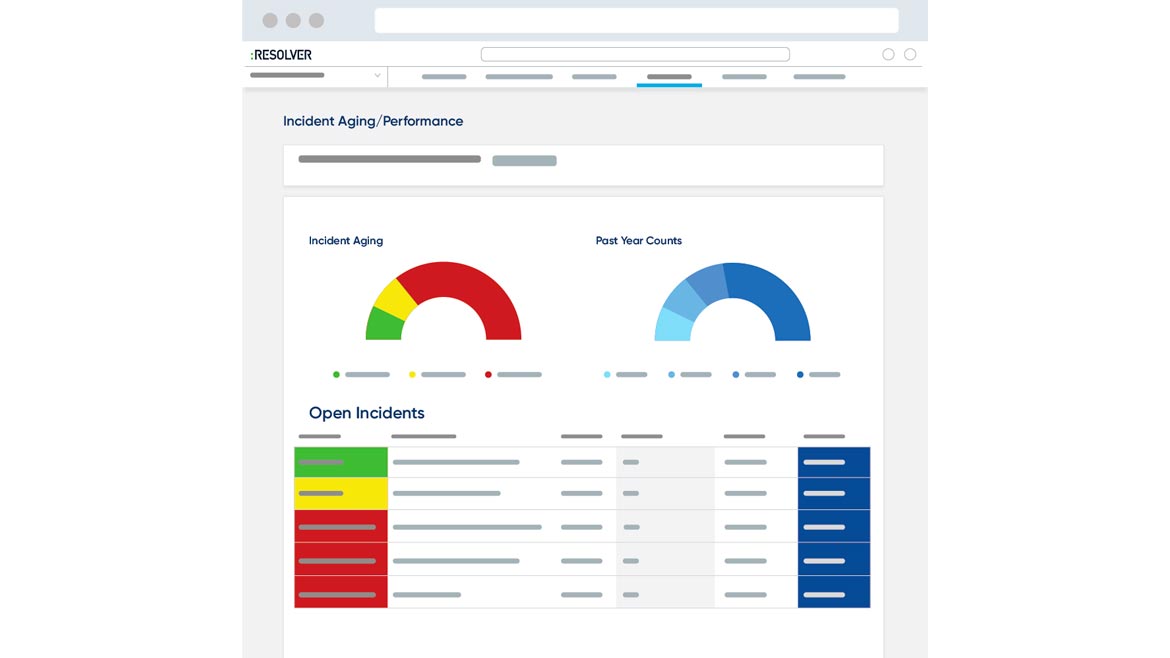
Resolver Inc. announced the 3.6 release features for its cloud-based incident management software. With the additional features, corporate security teams can gain better visibility and insights to protect their organizations. Capabilities include confidential reporting to enable employees to report incidents from anywhere and minimize fear of retaliation, as well as Email Data Collection and Hotline Reporting to improve corporate security and case investigation teams’ ability to bring data into Resolver’s incident and case management applications. Security teams can also leverage data from existing processes via integrations. Image courtesy of Resolver
Find out more at www.resolver.com
Salient Systems
Leverages Intelligent Video Technology to Mitigate Risks
The CompleteView video management system from Salient Systems is an enterprise-ready, open video data platform that offers bandwidth management and enables users to access more cameras from any client. The newest version, CompleteView 7.0, provides the foundation for cloud connectivity, enabling remote management and monitoring of the deployment. End users can leverage on-prem and cloud access while retaining the flexibility and ownership of their data. CompleteView 7.0 also enables flexibility in storage with enhancements such as the creation of storage pools with improved backup and overflow capabilities and new camera-based retention policies. New camera support for multi-sensor panoramic cameras provides added capabilities for large spaces. Image courtesy of Salient Systems
Find out more at www.salientsys.com
Speco Technologies
Equipped With Audio and Visual Deterrence
Speco Technologies’ O4TDD1M AND O4BDD1M cameras capture video up to 4 megapixels at 30 frames per second. Additionally, these cameras are both NDAA compliant and are equipped with audio and visual deterrence as well as analytics, which drastically reduce false alarms and allow units to be accurate. When paired with either vehicle or human detection, O4TDD1M AND O4BDD1M will trigger both audio and visual deterrence. The audio deterrence comes in the form of a pre-recorded audio message, which is a customizable feature to relay messages to anyone in the area. Image courtesy of Speco
Find out more at www.specotech.com
Teledyne FLIR
Designed for Harsh Environments
Teledyne FLIR’s FLIR RS6780 long-range radiometric infrared camera system is designed for range tracking, target signature, outdoor testing and science applications in all conditions. Featuring continuous zoom, the camera includes an integrated motorized three-position filter wheel and optional factory calibrations to support thermography applications up to 3000°C. The optional 3x zoom attachment provides engineers and scientists the flexibility to change the focal range from the standard 50 mm – 250 mm to up to 150 mm – 750 mm, designed to get the most pixels on target and address unique application and testing requirements in the field. The camera also features tri-level sync, providing operators the ability to sync the frame capture of the RS6780 to other types of video output, such as visible or ultraviolet, where the other cameras do not have a sync out/in option. Image courtesy of Teledyne FLIR
Find out more at www.flir.com
Topo.ai
Supports Crisis Management from Alerts to Investigations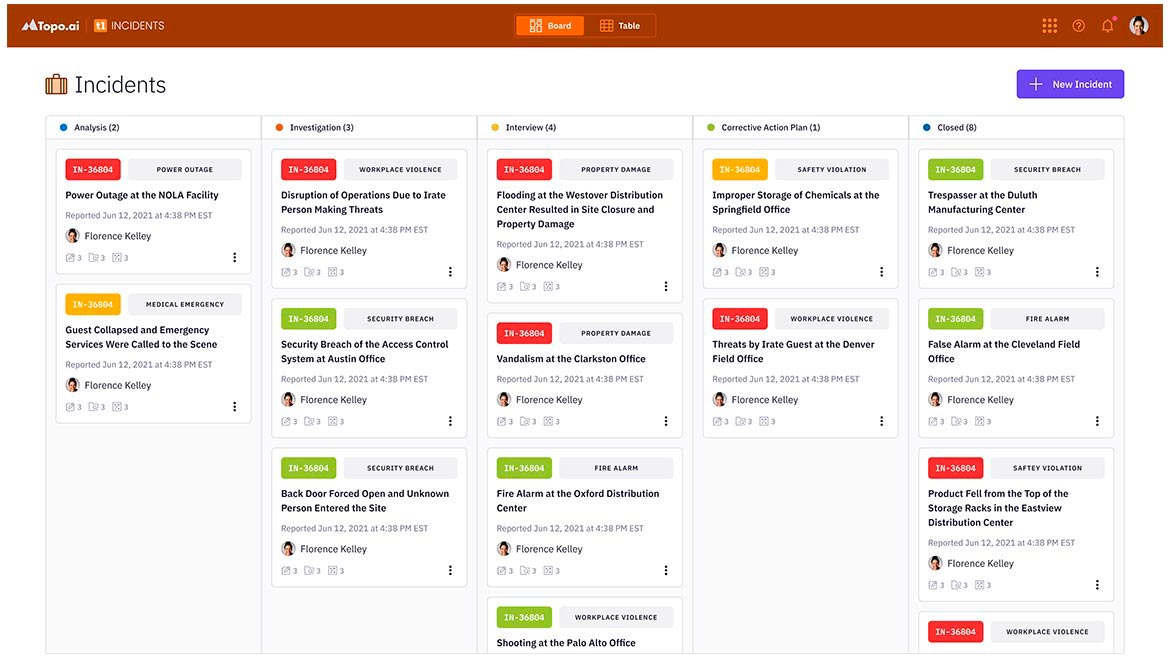
Topo.ai’s TopoONE Incidents is an integrated incident management system within the TopoONE platform that helps to ensure consistency in all phases of incident management, including automated intake of details from threat alerts and other sources; user-configurable workflows, tasks and checklists; and tracking all actions and information updates. The system provides comprehensive support for several use cases such as catastrophic weather events and criminal investigations as well as simple incidents such as vandalism and minor injuries. The incident management system is integrated with the map-based common operating picture in TopoONE. Image courtesy of Topo.ai
Find out more at www.topoai.com
Winsted
Protects Control Room Employees From COVID-19
Protective Operator Partitions from Winsted aim to reduce the risk of exposure to COVID-19 in tight spaces like a control room environment, where social distancing can be difficult to maintain. Winsted provides a partition that may help reduce both exposure and the risk of exposing others within a control room or operations center. The partitions are designed to fit multiple workspaces and are repositionable and extendable. Image courtesy of Winsted
Find out more at www.winsted.com
For more articles on security products, visit:
Spotlight on security technology at GSX 2021
Product spotlight on threat monitoring and risk assessment solutions
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




