Product spotlight on healthcare solutions
Security magazine spotlights solutions that can benefit security professionals in the healthcare sector, from securing medical devices to connecting first responders with live incident video streams.

Carbyne
Connects First Responders to Live Video
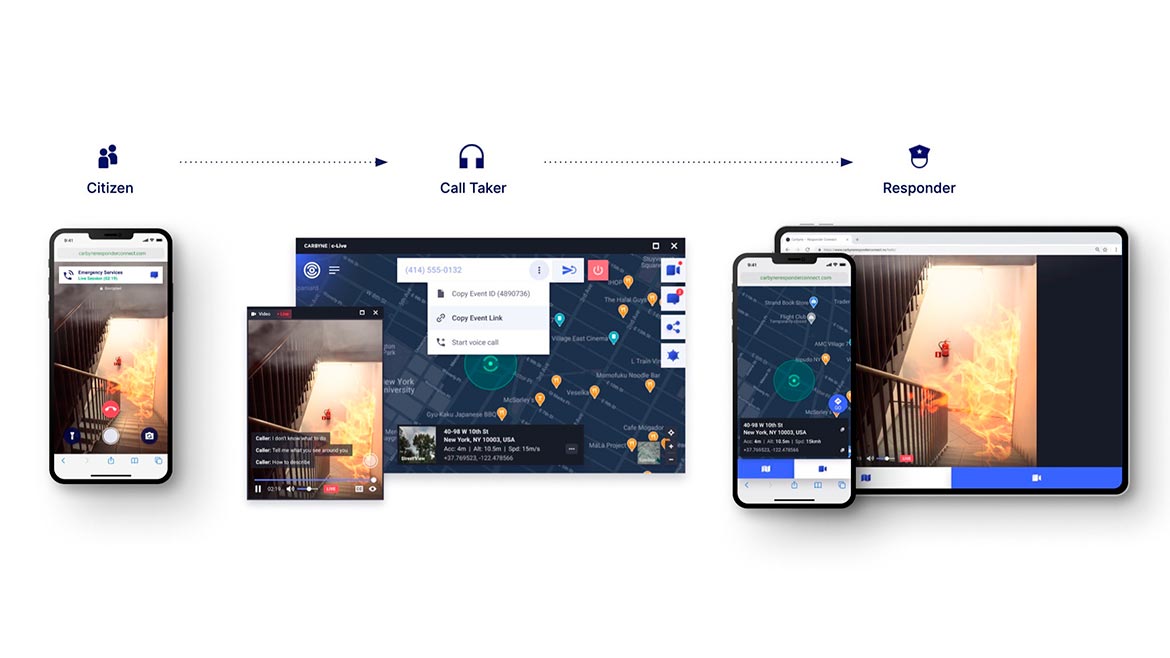 Carbyne’s Responders Connect aims to enable 911 dispatchers to share a live video stream of an incident directly to a first responder’s mobile device without requiring a downloaded app or software. It goes into effect when a caller shares video with their 911 dispatcher through Carbyne’s Universe platform. Via this platform, the dispatcher can copy a link that can then be shared via text message, email or any other mobile delivery method and is directed to the first responders’ Mobile Data Terminal, which is used in all public safety vehicles. Medical responders can provide real-time guidance for incidents where individuals need immediate action and offer instructions on how to perform first aid procedures. Image courtesy of Carbyne
Carbyne’s Responders Connect aims to enable 911 dispatchers to share a live video stream of an incident directly to a first responder’s mobile device without requiring a downloaded app or software. It goes into effect when a caller shares video with their 911 dispatcher through Carbyne’s Universe platform. Via this platform, the dispatcher can copy a link that can then be shared via text message, email or any other mobile delivery method and is directed to the first responders’ Mobile Data Terminal, which is used in all public safety vehicles. Medical responders can provide real-time guidance for incidents where individuals need immediate action and offer instructions on how to perform first aid procedures. Image courtesy of Carbyne
Find out more at www.carbyne911.com
Cynerio
Monitors Cyberattacks on Medical Devices
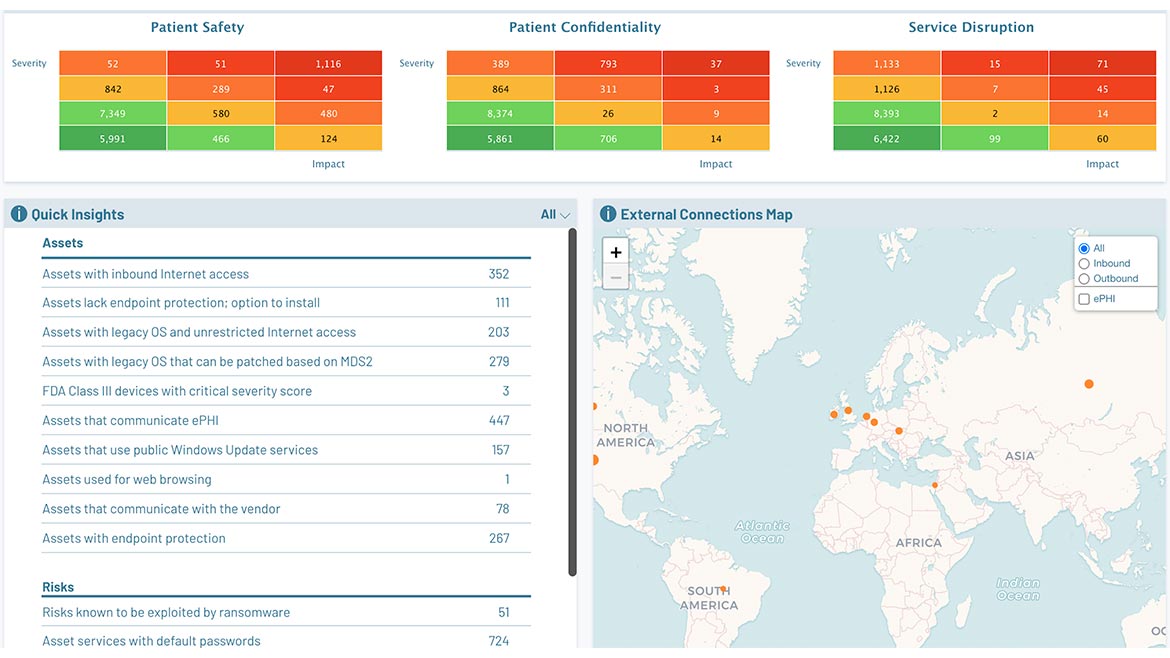 Cynerio’s IoT Attack Detection and Response module aims to allow hospitals to identify, contain and mitigate threats on medical, Internet of Things (IoT) and operational technology devices exhibiting malicious or suspicious behavior. Remediation, including the collection of forensic data, can then be performed when the device is not in use. The IoT Attack Detection and Response module uses micro-segmentation to secure phases of the IoT attack lifecycle from detection and investigation to response and containment. Image courtesy of Cynerio
Cynerio’s IoT Attack Detection and Response module aims to allow hospitals to identify, contain and mitigate threats on medical, Internet of Things (IoT) and operational technology devices exhibiting malicious or suspicious behavior. Remediation, including the collection of forensic data, can then be performed when the device is not in use. The IoT Attack Detection and Response module uses micro-segmentation to secure phases of the IoT attack lifecycle from detection and investigation to response and containment. Image courtesy of Cynerio
Find out more at www.cynerio.com
Johnson Controls
Helps Protect Access Control from Cyberattacks
 Johnson Controls’ Tyco Software House iSTAR Ultra G2 is a flexible door controller that can accommodate both wired and wireless locksets and includes expanded memory capacity. It can manage up to one million credentials for up to 32 doors. iSTAR Ultra G2 includes dual GigE network ports using TLS 1.3 network authentication and cluster-based anti-passback technology. Its hardware-based cybersecurity protection using Trusted Execution Environment can help guard against cyberattacks while the Open Supervised Device Protocol Secure Channel communication standard provides encrypted two-way communication between devices, including readers and controllers. Image courtesy of Johnson Controls
Johnson Controls’ Tyco Software House iSTAR Ultra G2 is a flexible door controller that can accommodate both wired and wireless locksets and includes expanded memory capacity. It can manage up to one million credentials for up to 32 doors. iSTAR Ultra G2 includes dual GigE network ports using TLS 1.3 network authentication and cluster-based anti-passback technology. Its hardware-based cybersecurity protection using Trusted Execution Environment can help guard against cyberattacks while the Open Supervised Device Protocol Secure Channel communication standard provides encrypted two-way communication between devices, including readers and controllers. Image courtesy of Johnson Controls
Find out more at www.johnsoncontrols.com
MetTel
Enables Zero Trust Access to Patient Data
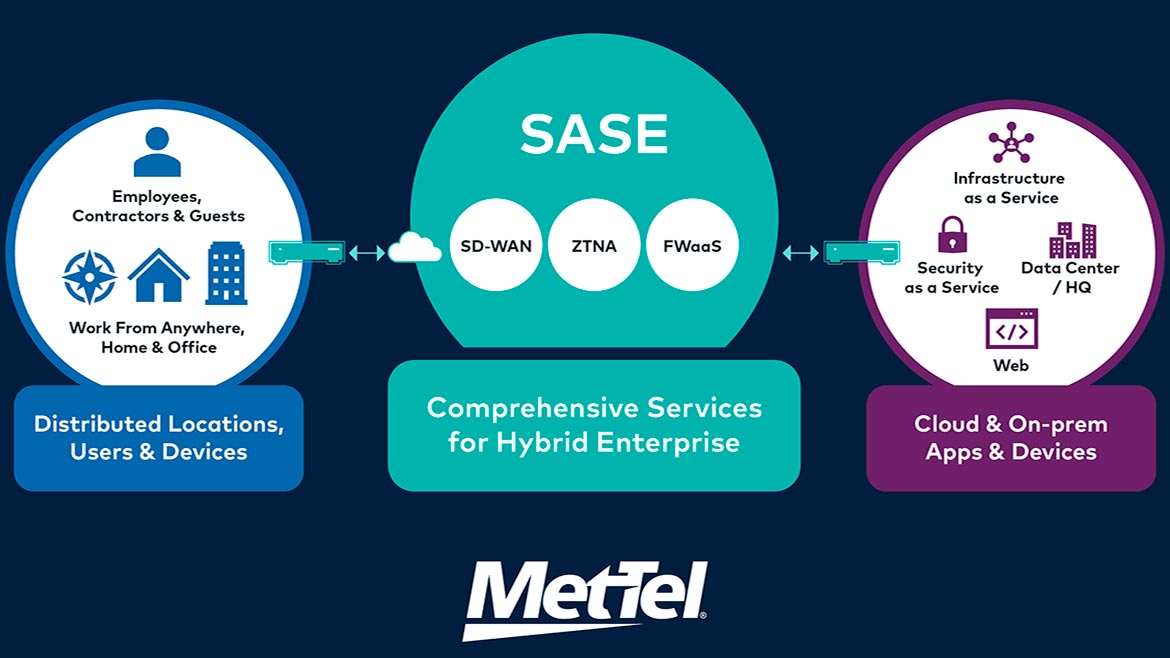 MetTel’s Global Cloud Network can help safeguard network and sensitive data. The firm’s secure access service edge (SASE) portfolio with a zero trust network access (ZTNA) offering aims to provide secure remote access to an organization’s applications, data and services based on clearly defined access control policies. ZTNA provides service and application access only to individuals who have been explicitly granted access versus the broad network access virtual private networks afford. Healthcare organizations are tasked with protecting the privacy of patients by HIPAA (Health Insurance Portability and Accountability Act) regulations, and ZTNA can secure patient data by requiring user authentication at every access point. Image courtesy of MetTel
MetTel’s Global Cloud Network can help safeguard network and sensitive data. The firm’s secure access service edge (SASE) portfolio with a zero trust network access (ZTNA) offering aims to provide secure remote access to an organization’s applications, data and services based on clearly defined access control policies. ZTNA provides service and application access only to individuals who have been explicitly granted access versus the broad network access virtual private networks afford. Healthcare organizations are tasked with protecting the privacy of patients by HIPAA (Health Insurance Portability and Accountability Act) regulations, and ZTNA can secure patient data by requiring user authentication at every access point. Image courtesy of MetTel
Find out more at www.mettel.net
Verkada
Automates Visitor Access and Identification
 Verkada Guest is built on Verkada’s integrated physical security platform and aims to simplify and customize the visitor check-in experience for hospitals and other organizations. The platform allows administrators to configure visitor arrivals through touchless check-in, photo capture, badge printing, arrival notifications and remote door unlocking. Administrators can use Guest to view a timeline of events relating to each visitor; set person-of-interest alerts; and manage site-specific access with role-based permissions. Image courtesy of Verkada
Verkada Guest is built on Verkada’s integrated physical security platform and aims to simplify and customize the visitor check-in experience for hospitals and other organizations. The platform allows administrators to configure visitor arrivals through touchless check-in, photo capture, badge printing, arrival notifications and remote door unlocking. Administrators can use Guest to view a timeline of events relating to each visitor; set person-of-interest alerts; and manage site-specific access with role-based permissions. Image courtesy of Verkada
Find out more at www.verkada.com
viisights
Detects Abnormalities in Surveillance Video Streams
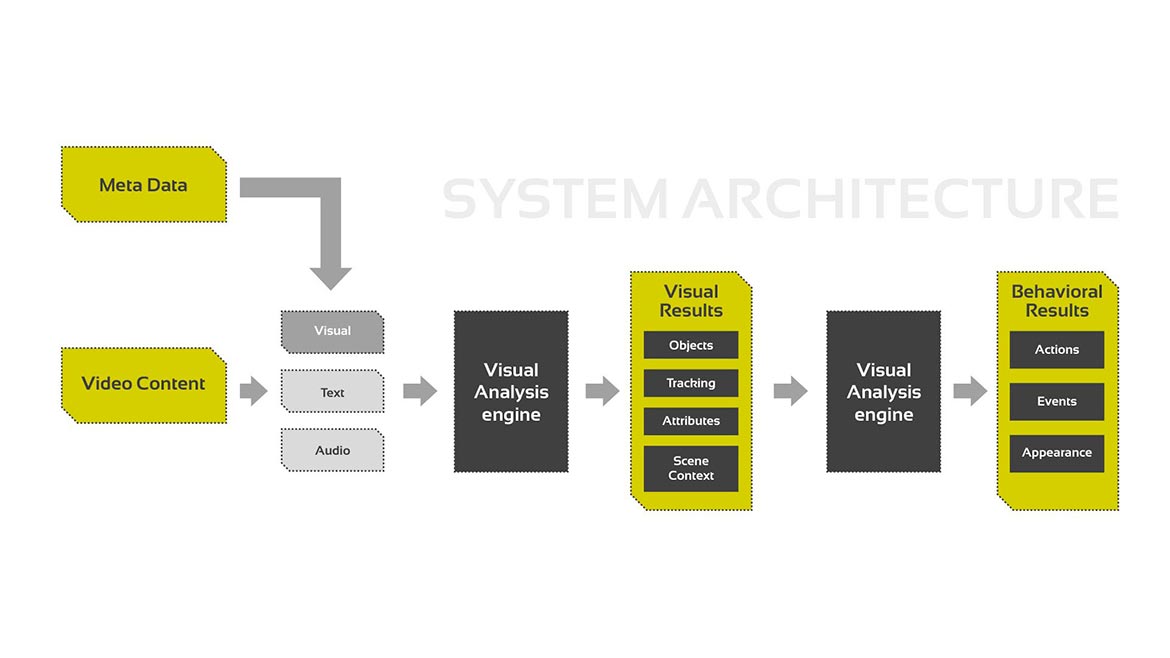 The viisights Behavioral Analytics with advanced video understanding technology solution aims to help healthcare security professionals recognize abnormal behaviors in surveillance footage in real time and notify personnel of any incidents. Behaviors noted by the analytics solution can include workplace violence, weapon detection, fighting or bullying, trespassing, vandalism and theft, environmental hazards such as smoke or fire, occupancy analytics, and whether or not an individual is wearing a face mask. Image courtesy of viisights
The viisights Behavioral Analytics with advanced video understanding technology solution aims to help healthcare security professionals recognize abnormal behaviors in surveillance footage in real time and notify personnel of any incidents. Behaviors noted by the analytics solution can include workplace violence, weapon detection, fighting or bullying, trespassing, vandalism and theft, environmental hazards such as smoke or fire, occupancy analytics, and whether or not an individual is wearing a face mask. Image courtesy of viisights
Find out more at www.viisights.com
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





