Product spotlight on identity management solutions

Securing physical or digital assets are at the heart of reducing enterprise and business risks. Identity management solutions help enterprises verify a user’s identity and ensure that only authorized users access facilities, applications, systems or networks. Let’s explore a sampling of the latest identity management solutions.
AlertEnterprise
Delivers Identity Lifecycle Process and Workflow Enterprise-Wide
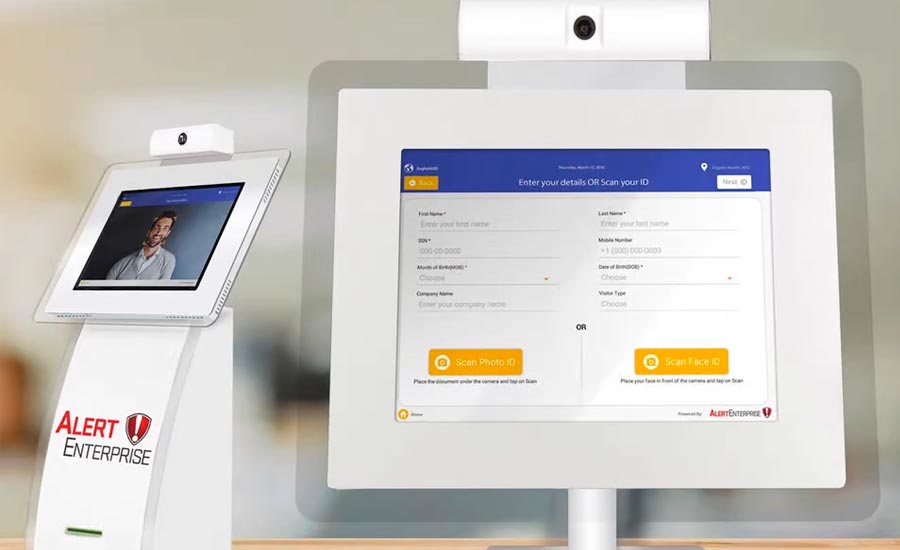
AlertEnterprise Visitor Identity Management (VIM) software controls the visitor lifecycle end-to-end, from pre-registration and self-service check-in to notifying hosts of visitor arrivals and checking out. It assists with access governance, fosters integration with other systems and platforms, including physical access control (PACS), and offers credentialing. VIM helps enforce company policies and compliance standards, helping employees, visitors and contractors stay compliant and ensuring they only have access to what they need. Credentials and access automatically expire and are taken offline when access is no longer needed, reducing risk. It allows for real-time integration with leading PACs, HR, training, ticket management, IT, industrial control and SCADA systems to compile insights and data needed for enterprise situational awareness. Image courtesy of AlertEnterprise
Find out more at www.alertenterprise.com
Tyco
Combines Access Control and Identity Management
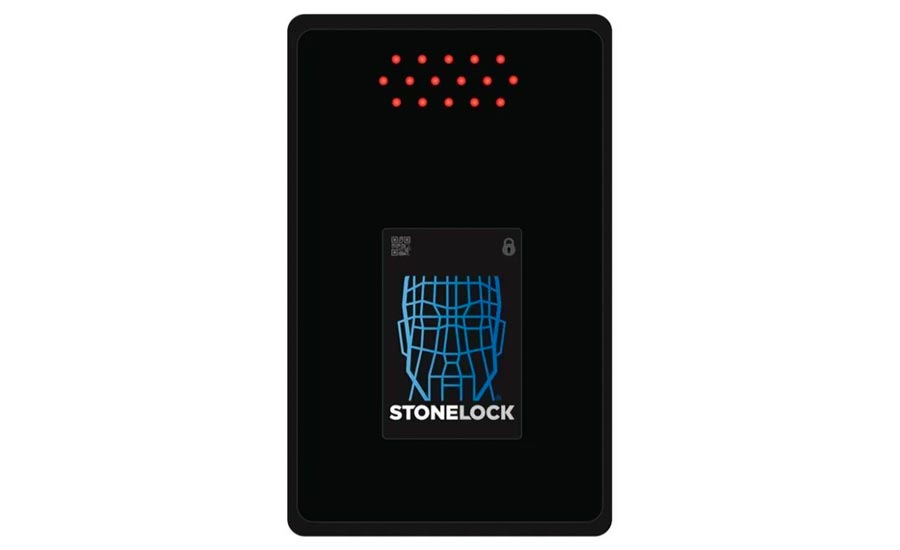 Tyco Kantech EntraPass and StoneLock GO’s opt-in “faceless” recognition is designed to protect users by safeguarding their privacy without photographs, while eliminating the need to physically touch the reader. The integration of StoneLock GO with Kantech EntraPass security management assists in mitigating threats from vulnerabilities such as weak PINs, code sharing and risks from surface contamination via contactless technology. While an access card or password can be susceptible to theft or cloning, the integration offers anti-spoofing and false acceptance rate authentication to better ensure that the people accessing facilities have been granted permission. Image courtesy of Tyco
Tyco Kantech EntraPass and StoneLock GO’s opt-in “faceless” recognition is designed to protect users by safeguarding their privacy without photographs, while eliminating the need to physically touch the reader. The integration of StoneLock GO with Kantech EntraPass security management assists in mitigating threats from vulnerabilities such as weak PINs, code sharing and risks from surface contamination via contactless technology. While an access card or password can be susceptible to theft or cloning, the integration offers anti-spoofing and false acceptance rate authentication to better ensure that the people accessing facilities have been granted permission. Image courtesy of Tyco
Find out more at www.kantech.com
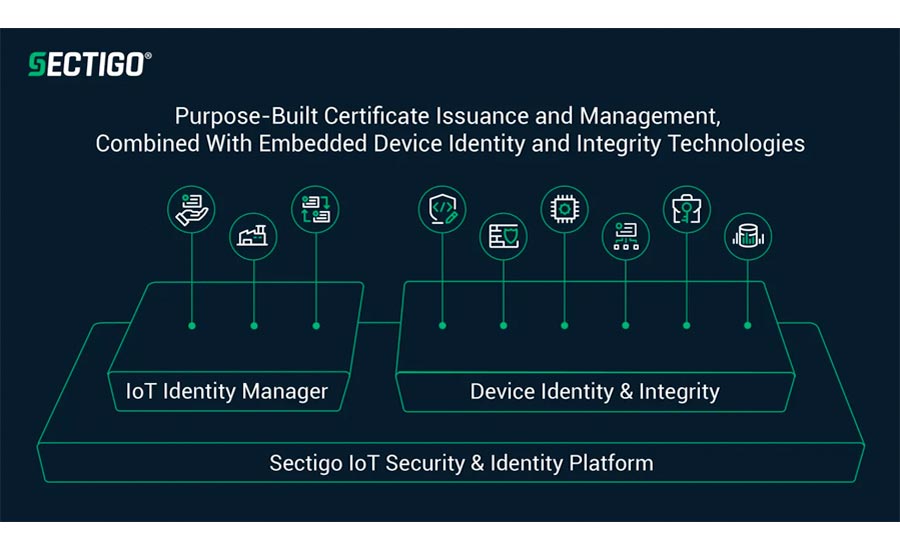
Sectigo
Combines Device Identity, Integrity Technologies With Certificate Issuance and Management
Sectigo Internet of Things (IoT) Security & Identity Management Platform helps integrate and manage connected devices for original equipment manufacturers (OEMs) and enterprises. Features include a public key infrastructure (PKI) client software development kit to help secure and authenticate connected devices so enterprises can protect their infrastructure. The platform enables users to build secure devices that are compliant with security standards and IoT security regulations. Image courtesy of Sectigo
Find out more at www.sectigo.com
Panasonic
Facial Recognition, Detection and Identification of Individuals
 Panasonic i-PRO FacePRO facial recognition analytics employ artificial intelligence (AI) and deep learning to recognize and authenticate an individual’s identity. The software can identify a person even if their face is partially covered, if they are at an obscure camera angle or if they have aged, according to the company. The AI analytics can detect if an individual is not wearing a mask and detect when they have an elevated body temperature. The software enables automatic redaction of faces on video, which can help save time for security personnel and law enforcement agencies, schools, municipalities, correction facilities and others to respond to FOIA or FERPA requests. Image courtesy of Panasonic
Panasonic i-PRO FacePRO facial recognition analytics employ artificial intelligence (AI) and deep learning to recognize and authenticate an individual’s identity. The software can identify a person even if their face is partially covered, if they are at an obscure camera angle or if they have aged, according to the company. The AI analytics can detect if an individual is not wearing a mask and detect when they have an elevated body temperature. The software enables automatic redaction of faces on video, which can help save time for security personnel and law enforcement agencies, schools, municipalities, correction facilities and others to respond to FOIA or FERPA requests. Image courtesy of Panasonic
Find out more at www.i-pro.com
Simeo
Automates Application Integration
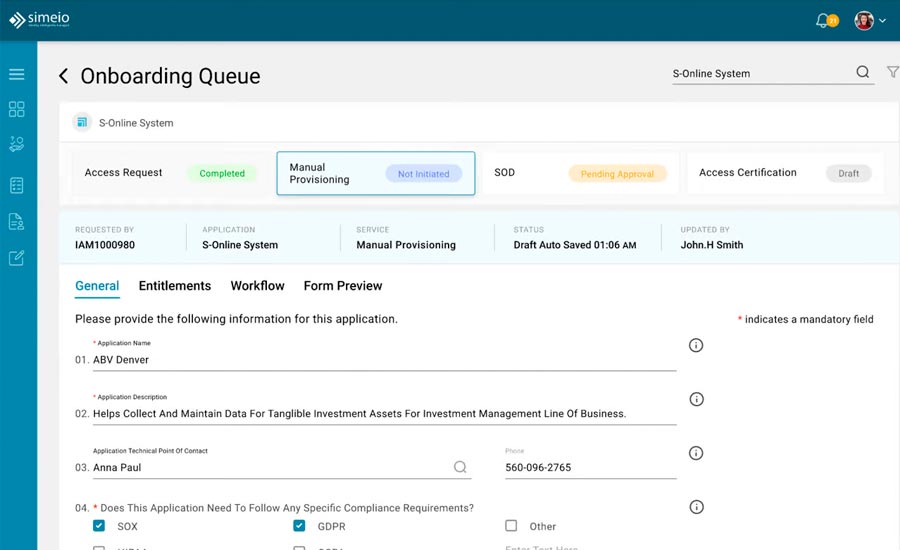 Simeo’s Modernized Application On-Boarding-as-a-Service helps organizations to onboard applications into their identity ecosystem. The solution offers security controls, compliance posture and centralized visibility into identity and access management (IAM) program maturity. Modernized Application On-Boarding provides internal stakeholders with intelligence through a dashboard that displays the number of apps within the organization and the number of apps onboarded, thus providing visibility into the key success metrics of the IAM solutions. Image courtesy of Simeo
Simeo’s Modernized Application On-Boarding-as-a-Service helps organizations to onboard applications into their identity ecosystem. The solution offers security controls, compliance posture and centralized visibility into identity and access management (IAM) program maturity. Modernized Application On-Boarding provides internal stakeholders with intelligence through a dashboard that displays the number of apps within the organization and the number of apps onboarded, thus providing visibility into the key success metrics of the IAM solutions. Image courtesy of Simeo
Find out more at www.simeio.com
SecureAuth
Built-in Privacy Controls With User Identity Management
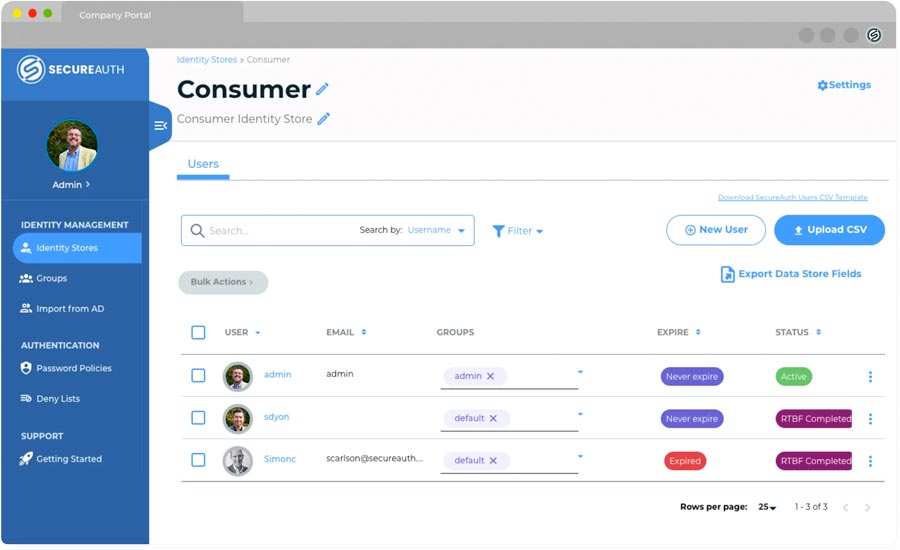 SecureAuth Identity Store is a privacy-focused cloud directory that helps users secure personally identifiable information of all non-workforce and customer identities, helping maintain compliance with government regulations and privacy protection acts and laws such as the European General Data Protection Regulation and the California Consumer Privacy Act. With Identity Store, users can manage identities for all partners or suppliers by creating time-limited access rights. Identity Store also provides built-in “Right to Be Forgotten” controls, letting users terminate their accounts and delete associated data. Image courtesy of SecureAuth
SecureAuth Identity Store is a privacy-focused cloud directory that helps users secure personally identifiable information of all non-workforce and customer identities, helping maintain compliance with government regulations and privacy protection acts and laws such as the European General Data Protection Regulation and the California Consumer Privacy Act. With Identity Store, users can manage identities for all partners or suppliers by creating time-limited access rights. Identity Store also provides built-in “Right to Be Forgotten” controls, letting users terminate their accounts and delete associated data. Image courtesy of SecureAuth
Find out more at www.secureauth.com
SAFR from RealNetworks
Monitors Identity and Controls Access
SAFR from RealNetworks facial recognition platform includes Passive Liveness detection and anti-spoofing features that can help improve the security of unattended access control use cases and alert security teams to attempted in-progress perimeter breaches. The feature helps verify that a real person is in front of any standard RTSP or USB camera, instead of a photo or video clip. In version 3.4, the SAFR algorithm analyzes texture and context based on the RGB visual spectrum field from a standard 2D camera, such as an IP camera embedded in an access control terminal, an ATM camera, or a USB or laptop camera. Image courtesy of SAFR
Find out more at www.safr.com
Idesco Corp.
Card Printer Personalizes Oversized ID Cards

Idesco Corp.’s XCR100 2.0 card printer allows users to personalize oversized ID cards. The printer is a dye-sublimation printer that can personalize CR100 cards, which are larger than the standard credit card size. The printer can produce up to 180 full cards per hour in color and up to 1,400 cards per hour in monochrome. The cards can help facilities, such as healthcare systems, maintain a safe environment for patients and staff alike, helping identify personnel and visitors. Image courtesy of Idesco Corp.
Find out more at www.idesco.com
HID Global
Enables Identity and Access Management Across Systems
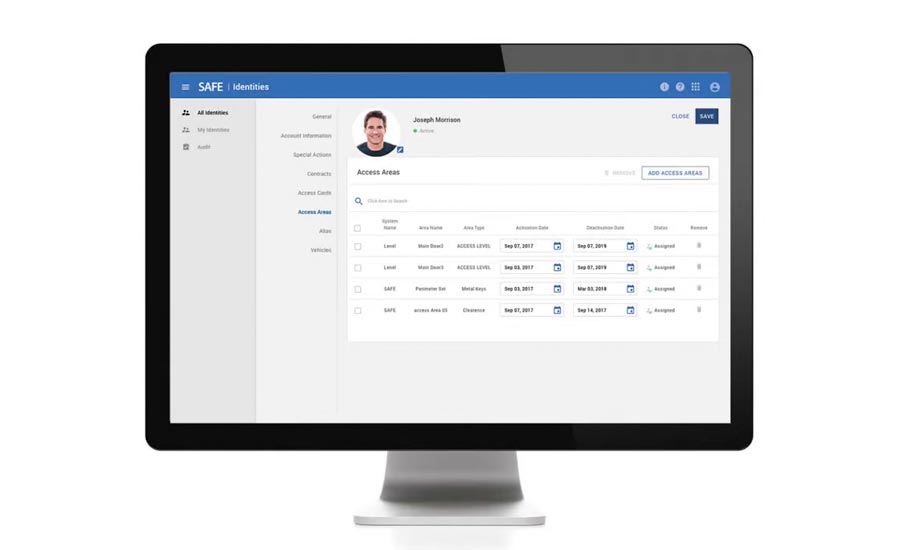 HID SAFE Enterprise helps enable physical access to staff, employees or visitors. The solution helps break down traditional organizational silos by creating a framework to integrate disparate systems. The software provides a policy-based supervisory management system to automate manual workflows and processes, and it offers an integrated enrollment, access-provisioning and badging engine. The solution helps teams create a transparent, auditable compliance process. Image courtesy of HID Global
HID SAFE Enterprise helps enable physical access to staff, employees or visitors. The solution helps break down traditional organizational silos by creating a framework to integrate disparate systems. The software provides a policy-based supervisory management system to automate manual workflows and processes, and it offers an integrated enrollment, access-provisioning and badging engine. The solution helps teams create a transparent, auditable compliance process. Image courtesy of HID Global
Find out more at www.hidglobal.com
Genetec
Assigns and Updates Access Rights Based on Security Policies
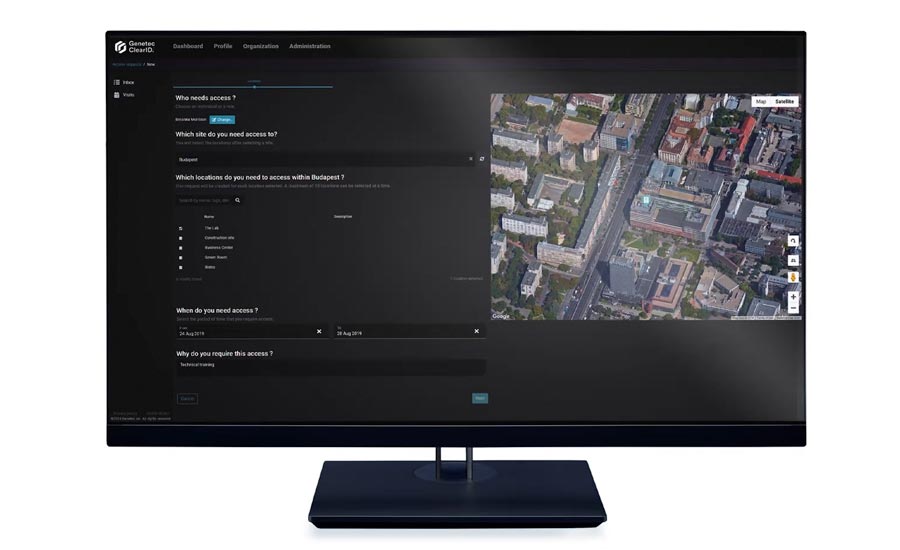
Genetec ClearID is a self-service physical identity and access management (PIAM) system that helps strengthen security policies while improving the flow of people within organizations. Unified with an access control system, this cloud-based solution uses a workflow-based approach that allows employees to make access requests and schedule visitors. It helps enforce security policies and update individual access rights based on current attributes. The solution helps ensure that only users with the necessary approvals have access to secure areas. Image courtesy of Genetec
Find out more at www.genetec.com
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!