
In an Uncertain Economy, Security Is a Necessity - Not an Afterthought
As theft surges and budgets tighten, proactive security is emerging as a vital pillar of operational resilience
Today’s economic climate is defined by persistent headwinds. Inflation remains a stubborn force, interest rates are at multi-decade highs, and cost containment is a top priority for many organizations. Companies of all sizes are feeling the squeeze with capital expenditures under review, operational budgets tightening, and forecasts being more cautious than optimistic.
Yet amid these financial challenges lies a parallel trend that security professionals cannot afford to ignore: a rise in property-related crime. Historically, there has been a strong correlation between economic downturns and increased theft, especially when it comes to high-value materials, heavy equipment, vehicles, and fuel. In tough times, desperation grows, and with it, opportunistic criminal activity.
As risk rises, the question becomes: What are security leaders doing to proactively protect their operations from disruption, reputational damage, and loss of revenue and physical assets?
Security Operations Are Vulnerable by Nature
To understand why so many operational sites are attractive targets, consider their physical layout. By necessity, assets, equipment, and materials are stored, staged, and transported across a network of locations — many of which operate around the clock, span both rural and urban areas, and vary greatly in how they’re secured.
Common vulnerability points include:
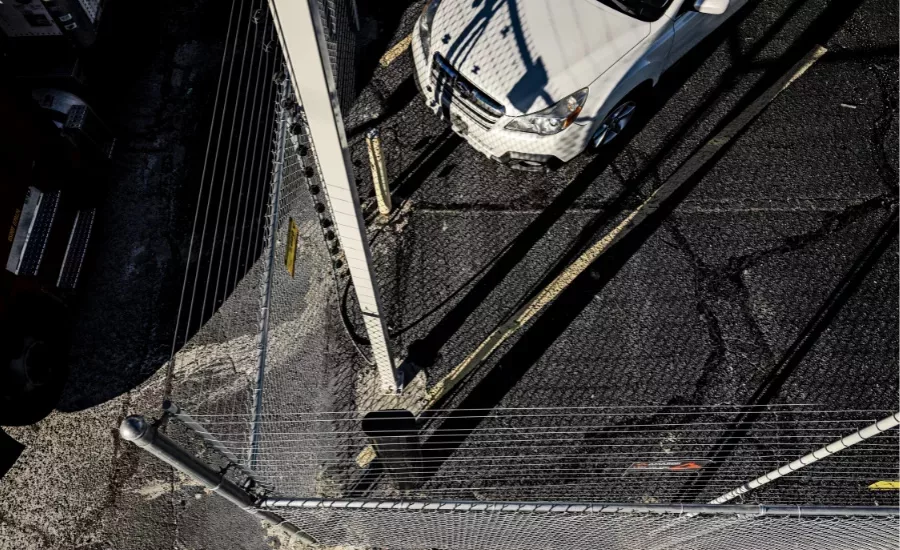
- Parking areas and storage yards where vehicles, trailers, or equipment sit idle for extended periods.
- Construction and project sites with minimal fencing or overnight supervision.
- Facilities and warehouses with gaps in perimeter coverage or access control.
- Remote lots holding surplus materials, overflow inventory, or fleet vehicles.
Each of these locations plays a critical role in daily operations — and each presents unique risks:
- Theft of high-value goods Theft of high-value assets is increasing. Criminals target items such as electronics, tools, metals, and valuable equipment—often striking when these assets are left unattended in unsecured or poorly monitored areas.
- Metal theft remains a costly challenge for industries from construction to utilities. With scrap prices high, even small amounts of stolen copper or other metals can yield significant payouts — especially when thieves hit the same site repeatedly.
- Component theft, such as catalytic converters, is rampant, particularly from fleet vehicles parked overnight. These parts contain precious metals and can be removed in minutes.
- Fuel siphoning has surged in recent years. Trucks, generators, and heavy equipment are easy targets when left in low-visibility areas.
- Heavy equipment theft, including machinery, generators, and specialty tools, can derail projects and cause significant replacement and downtime costs.
The common thread across these incidents is the presence of visibility gaps — weekends, after-hours periods, and remote locations with long response times or minimal surveillance. Criminals thrive in darkness, silence, and distance — exploiting weaknesses that traditional security measures often fail to address.
The Hidden Cost of Being Reactive
Many companies approach physical security as a passive function - an afterthought until something goes wrong. But the consequences of this mindset can be severe and far-reaching.
Let’s break down what a single theft or intrusion might cost your business:
- Missed deliveries and delayed jobs: Stolen goods, damaged infrastructure, or unavailable equipment can stall operations. In industries like construction, manufacturing, and retail, this can trigger late penalties, lost revenue, and customer dissatisfaction.
- Lost time managing the aftermath: Investigating a security breach is rarely quick. Your team may spend days coordinating with law enforcement, filing insurance claims, and conducting internal audits. During this time, production slows or stops. Here is a case study highlighting the challenges of downtime after a breach.
- Insurance premium hikes and coverage gaps: Even if losses are covered, frequent claims can lead to higher premiums or stricter policy terms. And some losses (like project delays) may not be covered at all. Here is an article that details the insurance costs for businesses with security failures.
- Employee morale and safety concerns: Workers who feel unsafe or see repeated theft may become disengaged, less productive, or more likely to seek employment elsewhere.
- Reputation damage: News of a security incident can affect customer confidence and brand equity, especially if delays ripple across multiple clients or markets.
The indirect cost of theft often dwarfs the value of what was actually stolen. It’s not just about what gets taken — it’s about the disruption it causes, the trust it erodes, and the time it wastes.
Security as a Strategic Investment - Not an Expense
Forward-thinking organizations have started to challenge the traditional view of security as a costly measure. Instead, they’re reframing it as a form of risk mitigation and operational resilience. In a modern business plan, it is just as important as cyber defenses, regulatory compliance, or operational resilience.
Security is no longer just about fences and guards. It’s about intelligent design, layered deterrence, and real-time visibility.
Here’s how industry leaders are upgrading their multi-layered approach:
- Electric or monitored fencing to actively deter intruders.
- Expertly planned LED lighting to eliminate dark corners and improve visibility, starting at the perimeter. Read more about lighting strategy for commercial properties here.
- Surveillance cameras with AI capabilities to detect and analyze unusual behavior.
- Motion sensors and alarm systems that alert response personnel instantly.
- Remote monitoring and automation, especially if you need to oversee multiple facilities simultaneously. When combined with AI-powered analytics, these systems can flag threats in real time, escalating only when human attention is truly needed.
- Access control systems that log who enter and exit facilities, and when they are allowed to do so. You can learn more about access control systems and their business benefits here.
In addition to layered security strategies, even minor layout adjustments can significantly impact a business’s overall security posture. For companies aiming to maximize every opportunity, seemingly obvious improvements are often missed without a strategic approach to security planning:
- Limiting entry points reduces vulnerability and unauthorized access.
- Elevating camera placement enhances visibility and coverage.
- Repositioning high-value assets away from perimeter fencing deters smash-and-grab opportunists.
Ultimately, the return on investment in security goes beyond preventing theft - —it’s reflected in reduced operational downtime, safer job sites, more efficient deliveries, and greater peace of mind.
Advice for Security Leaders
Now that vulnerabilities and security strategies have been outlined, and the hidden costs of inadequate security planning have been revealed, what practical steps can you take to strengthen your defenses?
If you haven’t reevaluated your physical security posture recently, now is the time. Here are four critical steps to consider:
- Audit your vulnerabilities. Walk your sites with fresh eyes — or bring in an independent expert. Identify access points, blind spots, and risks during low-visibility periods.
- Integrate security into operational continuity plans. Just as you plan for natural disasters or IT outages, plan for physical security incidents. What is your response protocol? Who is notified? How quickly can you recover and resume operations?
- Budget for security strategically. Treat security enhancements as capital investments, not reactive expenses. Prioritize high-risk locations and initiatives that deliver quick, measurable improvements.
- Partner with specialists. Don’t tackle this alone. Collaborate with security professionals who understand the unique challenges of your industry — especially where assets are mobile, high-value, and difficult to monitor.
In times of economic uncertainty, growth is important, but stability, uptime, and resilience are equally critical — and they all start with a secure perimeter.
Every vehicle, piece of equipment, and inventory item represents more than just a dollar value — it stands for commitments made to customers, wages paid to employees, and the ongoing momentum of your organization.
Don’t wait for theft to show you where your blind spots are. Reevaluate your security posture today before a single incident costs you far more than the investment required to prevent it.
Resources:
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





