Security Talk
Step-by-step strategy for the CISO
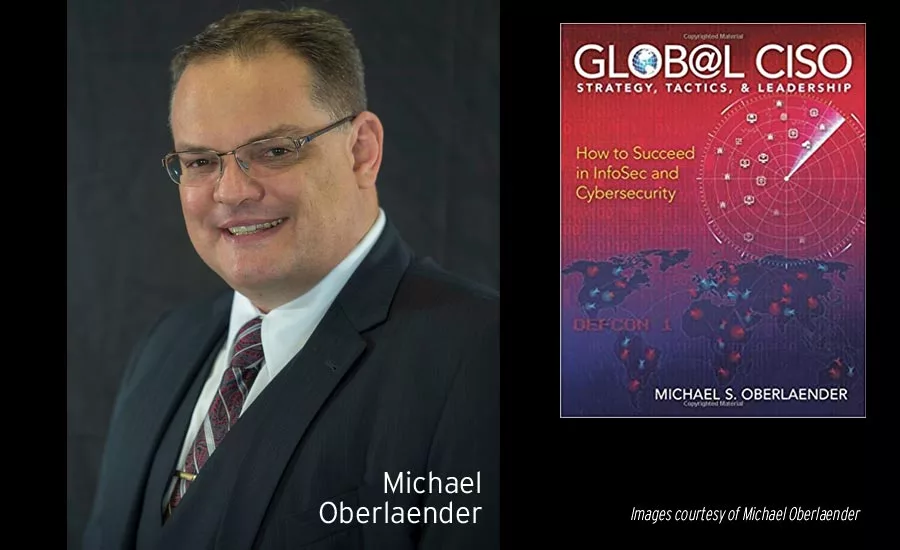
Michael Oberlaender has had cybersecurity leadership positions and CSO/CISO titles at enterprises around the world. He’s recovered companies from data breaches, built cyber-hardening strategies and policies, implemented cybersecurity budgets, forged relationships and communications with the C-suite, analyzed risks, and dealt with privacy laws around the world. And now, he’s written his second book, “Global CISO: Strategy, Tactics & Leadership — How to Succeed in InfoSec and Cybersecurity,” which takes his first-hand experience and gives CISOs and similar leaders a step-by-step approach to budgets and team building, privacy laws, security program planning and policy creation, backup plans, enumerating security metrics, conceptualizing SecDevOps (security, software development and IT operations), establishing a reporting structure, security architecture and design principles and more.
As one of Oberlaender’s toughest moments as Chief Information Security Officer of a global technology company in Houston, he describes when the company was hit with a major virus and zero-day attack. “In hindsight, we learned that a facility in Southeast Asia was not following security policies put in place and someone put a USB key that contained malicious code into a server. It steadily started an attack that was really devastating,” he recalls. Oberlaender developed a strategy to isolate all infected systems and, together with his team and the global organization, got the zero-day attack under control within 96 hours.
It is this experience and many others over the past 25 years that Oberlaender wants to share with his industry peers. He feels there is a need to share experiences as a cybersecurity leader, including tried-and-true ways of building security programs, hardening security and implementing policies and procedures that protect but don’t hinder an organization.
“I think many companies bring in CISOs that don’t have the technical expertise for the job. It’s so important for those of us that have lived through this and been through this to share knowledge and experience so [future CISOs] can prepare for that battle,” Oberlaender says.
He says that his most important advice for a cybersecurity leader would be three-fold. First, he says, is you’ve got to have integrity and build your team around others that have integrity. “Second, from an educational perspective, you’ve got to have qualifying certifications that you keep current and that you are consistently building and maintaining. Solid theoretical knowledge is critical. Then, you’ve got to be a very good communicator at all levels, with the board, C-suite and staff. Communication is imperative,” he says. Together, these traits will go a long way in setting you up for success.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








