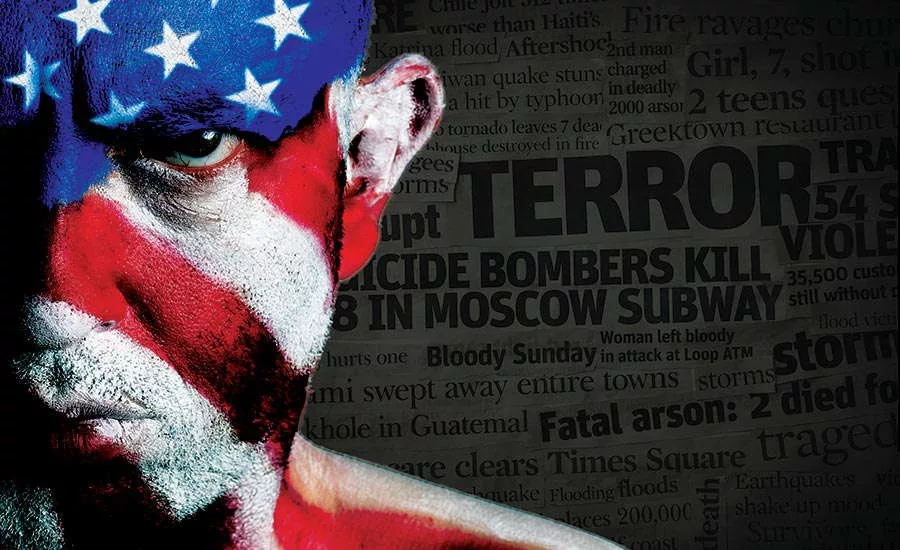
What Does an American Jihadist Look Like Online?
In addition to its research into cybercrime, terrorism and security threats worldwide, the George Washington University’s Center for Cyber & Homeland Security’s Program on Extremism homes in on extremist and terrorist threats and trends, seeking to provide empirical information that policymakers and security leaders can wrap their heads around on this complex and evolving challenge.
Seamus Hughes, Deputy Director for the Program on Extremism, is currently researching the state of Islamist-inspired terrorism in the U.S. He and his colleagues collate thousands of pages of legal documents on U.S. ISIS-related court cases (125 cases so far), conduct interviews with foreign fighters, defendants and attorneys, pull millions of ISIS English-language Twitter posts, and every month they release an updated demographic snapshot.
This information could help policymakers evaluate whether the use of a travel ban, for example, is the right approach when most of the court cases in the U.S. revolve around homegrown terrorism – people who were born and raised in the United States. “Vetting of visitors coming in may make sense from one aspect, but if you’re trying to address the issue of homegrown terrorism, you’re going to need a whole other set of policies,” says Hughes.
He is also researching how American ISIS members are recruited. “When we first started looking at this, Twitter was the platform of choice. Now, ISIS has been pushed away from the mainstream sites like YouTube, Facebook and Twitter, and they’ve largely concentrated on Telegram, which provides end-to-end encryption. It’s still an open platform, but you have to know what channels to go to in order to join. It’s not like a kid from the Midwest can stumble across it and meet an ISIS guy; it’s not as easy as it used to be.”
Hughes is also seeing the rise of “ISIS Virtual Entrepreneurs” – a team of six or seven ISIS members in Iraq who would actively reach out to Americans, befriend them and then encourage them to attack their homeland. This marks a hybrid recruitment method from older al-Qaida training camps and inspiring lone-actor attacks, he says.
“There’s a number of American ISIS supporters who can’t travel to Syria and Iraq but still want to be part of something bigger than themselves, so they’re looking at domestic attacks and plotting to prove that they’re part of the group,” says Hughes. The change in tactics – with most communications being conducted on encrypted channels – makes law enforcement’s job all that much more difficult.
However, from the private sector perspective, “a little bit of data and knowledge goes a long way,” Hughes adds. “Having an awareness into what’s happening online, what latest calls have been made for, whether ISIS has released a magazine or video advocating for this or that type of target to be attacked… this type of situational awareness is important.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







