Integrated Solutions
Always-on defense: The critical role of monitoring in manufacturing cyber protection
Manufacturing remains a prime target for cyber threat actors due to several factors.
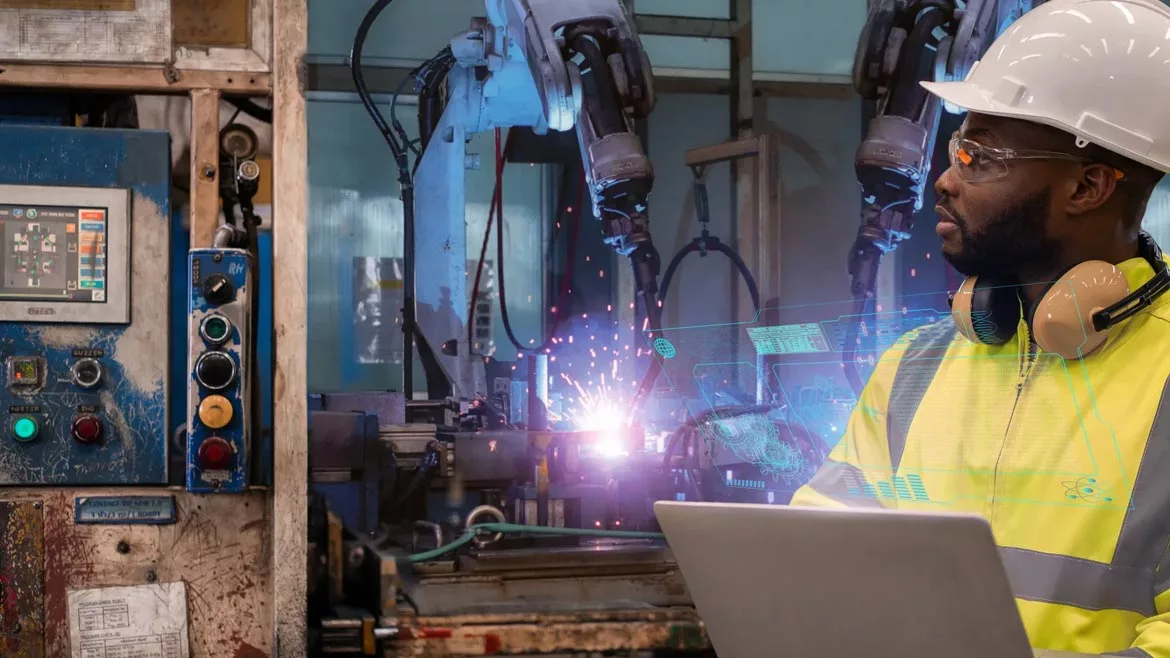
MAGNIFIER / iStock / Getty Images Plus via Getty Images
Manufacturing processes are intricately woven into the fabric of our daily lives, from the food on our tables to the devices we depend on and securing these operations is more crucial than ever. Industry 4.0 has introduced a wave of digital advancements that promise unparalleled efficiency but also expose manufacturers to a new realm of cyber threats.
In the first half of 2024, Critical Start’s biannual Threat Intelligence Report highlighted a significant uptick in cyberattacks across various sectors, with manufacturing and industrial Products bearing the brunt. Manufacturing’s reliance on interconnected systems has significantly expanded its attack surface. Historically, manufacturing networks were isolated from the internet, which provided a level of protection against cyber threats. However, the advent of Industry 4.0 has introduced a range of new technologies — such as predictive analytics and real-time process optimization — that require constant online connectivity.
Manufacturing remains a prime target for cyber threat actors due to several factors. The sector's low-tech legacy systems, lack of uniform cybersecurity regulations, and prioritization of physical over network security create significant vulnerabilities. Manufacturing’s broad impact across sectors, from food production to pharmaceuticals, means any disruption can have widespread ripple effects. The increased connectivity from Industry 4.0 further amplifies these vulnerabilities, making manufacturers attractive targets for cybercriminals seeking financial gain, industrial espionage, or sabotage. The Crown Equipment Corporation attack in June 2024 exemplifies how interconnected system vulnerabilities can lead to significant operational and financial damage.
A critical misconception in cybersecurity
One of the most pervasive misconceptions is that OT (Operational Technology) and IT (Information Technology) security are distinct, with minimal overlap. This outdated view fails to account for the convergence of IT and OT systems in modern manufacturing environments. A breach in IT systems can easily ripple through to OT systems, causing severe disruptions. For instance, the Colonial Pipeline incident highlighted the interconnected nature of IT and OT systems. Although the initial breach was IT-related, the unknown potential impact on OT systems led to a significant shutdown of certain operations, demonstrating the critical need for a unified security approach.
Adding to the complexity is the fact that many manufacturing cybersecurity leaders come from the IT side and may lack deep knowledge of OT threats. This generational shift in understanding the convergence of IT and OT is a critical challenge that needs to be addressed.
Evolving cyber criminal tactics and common attack vectors
Cybercriminal tactics in the manufacturing industry have evolved significantly. Attackers are no longer just deploying malware; they’re stealing credentials and using sophisticated social engineering tactics. For example, they may leverage generative AI to craft convincing phishing emails that can trick executives into transferring funds or revealing sensitive information.
Manufacturing’s broad impact across sectors, from food production to pharmaceuticals, means any disruption can have widespread ripple effects.
A major concern now is ransomware that specifically targets OT systems. Unlike traditional IT ransomware, which focuses on systems running Windows, these newer attacks are designed to exploit OT devices that don’t rely on standard operating systems, making them particularly dangerous.
Best practices for strengthening cybersecurity in manufacturing
To effectively defend against cyber threats, manufacturing leaders need to begin by segmenting their OT networks from IT systems and the internet. This step significantly reduces the risk of breaches spreading between different operational areas, isolating critical systems from potential cyberattacks. However, simply taking this step is not enough. Continuous, 24/7 monitoring is essential to verify that these segmentation measures are working properly and that controls remain in place. This ongoing oversight helps detect any breaches in real time, allowing companies to address them before serious damage occurs.
By ensuring proper network segmentation and consistent monitoring, manufacturers can cut down on the majority of cyberattacks. This forces threat actors to evolve their tactics, pushing them to be smarter and more deliberate in their attacks. Beyond segmentation and monitoring, organizations must also focus on securing access points through multi-factor authentication, strong password policies, and eliminating default credentials — common weak spots in manufacturing environments. Regular employee training across both OT and IT teams ensures that security is approached holistically, fostering a company-wide culture of vigilance and preparedness.
Ultimately, this multi-layered approach — combining network segmentation, always on 24/7 monitoring, strong access control, and a well-trained workforce — creates a formidable defense that significantly reduces the risk of successful cyberattacks while pushing adversaries to work harder to breach manufacturing systems.
The need for strong cybersecurity has never been more urgent. It’s no longer enough to rely on outdated methods or hope that attackers will overlook your systems. By embracing the reality of IT and OT convergence, addressing weak points, and committing to proactive security strategies, manufacturers can get ahead of cyber threats and keep their operations safe.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







