Security Enterprise Services
Top Security Guarding Companies Report 2016
The security officer industry faces a ‘Watershed Moment’ as consolidation alters the landscape.
December 1, 2016
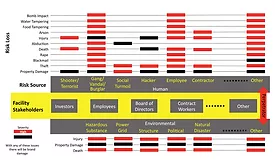
Using Environmental Risk Mapping and Analysis to Enable Effective Decision Making
Uninformed is unprepared. Build your own metrics and maps in order to make thoughtful, business-minded security decisions.
December 1, 2016
Duplicate Alerts Draining Security Analysts' Time
New research shows that 30 percent of analysts' manpower is lost to duplicate alerts.
November 22, 2016
4 Ways to Thwart Social Engineering Attacks
Social engineering attacks are on the rise. Here's what your organization can do to stop them.
October 25, 2016
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing