Rebalancing security and business innovation post-pandemic

Image from Pixabay
The past two years were all about accelerated digital transformation. Now, the pendulum is swinging in the opposite direction, with governance phases requiring companies to circle back and address security protections overlooked during the fast-moving pivots of the pandemic.
For many mid-market information technology (IT) leaders, security needs to play catch-up. But it’s more than just that. It’s time to rebalance the relationship between security and digital transformation and put security back in a proactive role.
How innovation and security got knocked out of balance
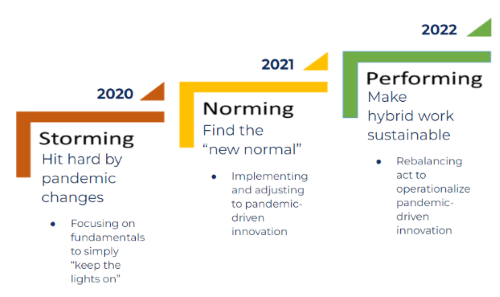 Image courtesy of Barbour
Image courtesy of Barbour
Since 2020, necessity has been driving digital transformation. COVID-19 demanded new business models, creating a “storming” phase of change. In lieu of going out of business, executives had no alternative but to put cybersecurity considerations on the back burner and mobilize guerrilla IT to keep the business running. Rush-ordered solutions created new risks:
- Remote work: Cost and supply chain constraints meant personal devices were sometimes used for work, creating unmanaged environments and increasing the corporate attack surface.
- Employees: With trends in employee turnover, security awareness training often fails. While the root cause of attacks are difficult to pinpoint, it’s hard not to connect the dots between the 150% rise in ransomware attacks and unpatched endpoints alongside their untrained users.
- Cloud: Security is more complex now with shadow IT concerns, cloud application misconfigurations, and changes in security roles and responsibilities as services transition to the cloud.
Moving through the “norming and performing” phases of 2021 and 2022, mid-market companies are now trying to patch the gaps left in the wake of rapid change.
The dangerous yet necessary game of playing catch-up
Recoil is common when innovation outpaces security. The effect can be described as security “pumping the brakes” on transformation. In the worst case scenario, companies slam on the brakes after a security breach or ransomware incident, but more often they pump the brakes after concerned stakeholders call for a security risk assessment. Either way, action is taken to assess risk, manage exposure and put controls in place. Several studies highlight today’s security rebound.
- 76% of CIOs say it’s challenging to find the right balance between business innovation and operational excellence.
- “After scrambling to adapt to the disruptions caused by the pandemic, security teams are deploying and managing technology and processes to build security into web and mobile applications, making remote work secure and improving the security and economics of networking and cloud-based resources,” according to an (ISC)2 report.
- Analysts at Gartner also describe the challenges of cloud security. “The most commonly cited challenge to cloud adoption was gaining security team approval and support for cloud migration strategies, suggesting that security teams are struggling to adapt to increasingly complex cloud technologies.”
Playing catch-up can cost businesses dearly. When a remote worker was a factor in causing a data breach, the cost went up by $1.07 million, making the total $5.31 million on average. Companies can potentially find themselves taking on everything at once — updating security while simultaneously paying ransomware attackers and emergency response teams. For these reasons, catch-up is considered a dangerous game, but IT executives shouldn’t point fingers or stress about it. COVID-19 left no option. Course correcting now — before the data breach — is still an honorable win.
How to put checks and balances in place
If an organization doesn’t yet have a formal security program, start with these steps.
- Reassess security with remote work as a given. Yesterday’s band-aids will remain the long-term strategy with employees working beyond defined perimeters using their own devices.
- Initiate a cyber risk assessment. Identify priorities based on risk and business objectives, understanding where to focus now and in the future.
- If the organization has more than a few hundred employees, the business needs at least one dedicated security resource who is given the authority to challenge recklessness. Without an empowered owner, the security program rarely materializes because business decisions overrule risk mitigation.
- In combination with a risk assessment, use the available cybersecurity frameworks to identify needed controls and practices. Act with urgency and prioritize — don’t expect to do it all at once.
Rebalancing security and innovation
Ideally, security should never be catching up with innovation; it should be in sync or out in front of the business strategy. It is time to recalibrate.
Processes are needed to ensure security and innovation are always working in tandem. Here’s how to restore balance.
- Grow security capabilities and align security strategy to meet future needs starting now. What is the business vision and how can security empower it? Think about changes in users, services and the IT footprint. Put controls in place before they are needed, so they accelerate revenue rather than delay it.
- Start with the proverbial trilogy of technology, expertise and process. While security is mostly an expertise and process problem, technologies like cloud access security brokers (CASB) and secure access service edge (SASE) can help restore balance and increase agility, addressing connectivity and cybersecurity in support of the hybrid workforce. Ask for help from security consultants and service providers who can scale countermeasures.
- Don’t forget about executive sponsorship. Explain the threat landscape pertinent to the organization. Proactive approaches cost less by accelerating new revenue streams, preemptively managing cyber risk as companies engage with new services, markets and users. Sure, it costs money, but the alternative is to slam the brakes on innovation or pay for the data breach.
Using security to be future-ready
Change is certain, and digital transformation must be constant for businesses to adapt and capitalize on new market conditions. But innovation can easily become a disaster when security is out of balance. The confidence of being future-ready stems from security preparedness, control and enabling rapid change. These are necessary to counterbalance every type of transformational risk. The key is to have smoke detectors, fire doors and sprinkler systems alongside fire inspectors and professional alarm monitors — not to be calling in the fire trucks after the house is already on fire.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







