Security Talk
The evolution of enterprise security since 9/11

BrianEKushner / iStock / Getty Images Plus via Getty Image

On September 11, 2001, 19 militants associated with the Islamic extremist group al Qaeda hijacked four airplanes and carried out suicide attacks against targets in the United States. All told, nearly 3,000 people were killed as two of the planes crashed into the twin towers of the World Trade Center in New York City, a third plane hit the Pentagon, and a fourth plane crashed in a Pennsylvania field.
Only six people who were in the World Trade Center’s twin towers at the time of their collapse survived. The west side of the Pentagon military headquarters was set ablaze from jet fuel from the crash, causing a structural collapse of part of the building, killing everyone aboard the plane and another 125 military personnel and civilians on the ground. Back in NYC, close to 10,000 more people were treated for injuries due to the building collapses.
But you know all this. If you’re in your mid 20s or older, you may remember where you were or what you were doing when you found out about the terrorist attacks that not only defined George W. Bush’s presidency, but changed the course of life for so many in the United States and around the world.
Not long after 9/11, U.S. Congress established the Transportation Security Administration (TSA) on November 19, 2001, which prompted countries globally to follow suit in establishing further security procedures, operations and protocols, thus transforming how we travel.
Of course, it’s hardly just the establishment of the TSA that was born out of the deadliest foreign terrorist attack to hit United States soil. John McClurg, Senior Vice President and CISO at BlackBerry, and author of Security’s Cyber Tactics column, reminds us to take the events of 9/11 and other events since as lessons that can and should help guide us to the future. He points to a quote from Spanish-American philosopher George Santayana, who is credited with saying, “Those who cannot remember the past are condemned to repeat it.”
McClurg says, “A year doesn’t pass by that my reflections turn to the lessons of that day, which in many instances now tie themselves to aspects of our current environment in a manner that makes grappling with them even more critical.”
As we commemorate the 20th anniversary of September 11, 2001, Security spoke with several professionals in the industry to reflect on a few of the varied, significant ways in which enterprise security and security leadership at organizations, corporations and agencies around the world have changed, evolved and progressed over the past two decades.
“I have seen it change in a revolutionary way,” says Bonnie Michelman, CPP, CHPA, Executive Director: Police, Security and Outside Services at Mass General Brigham, the parent company of Massachusetts General Hospital, and former president of IAHSS, ASIS and ISMA. “Our industry has become an entire industry filled with thought leaders and a lot of credentials and university degrees that hadn’t existed before. I’ve also seen organizations take a really macro view of risk and incorporate enterprise security risk management into their major infrastructure in broader and deeper ways than ever before.”
Michelman says that enterprise security risk leaders have become true business leaders and influencers since 9/11, helping to drive sustainability and profitability within the enterprise, and taking on different functional areas within an organization that they hadn’t had a hand in previously.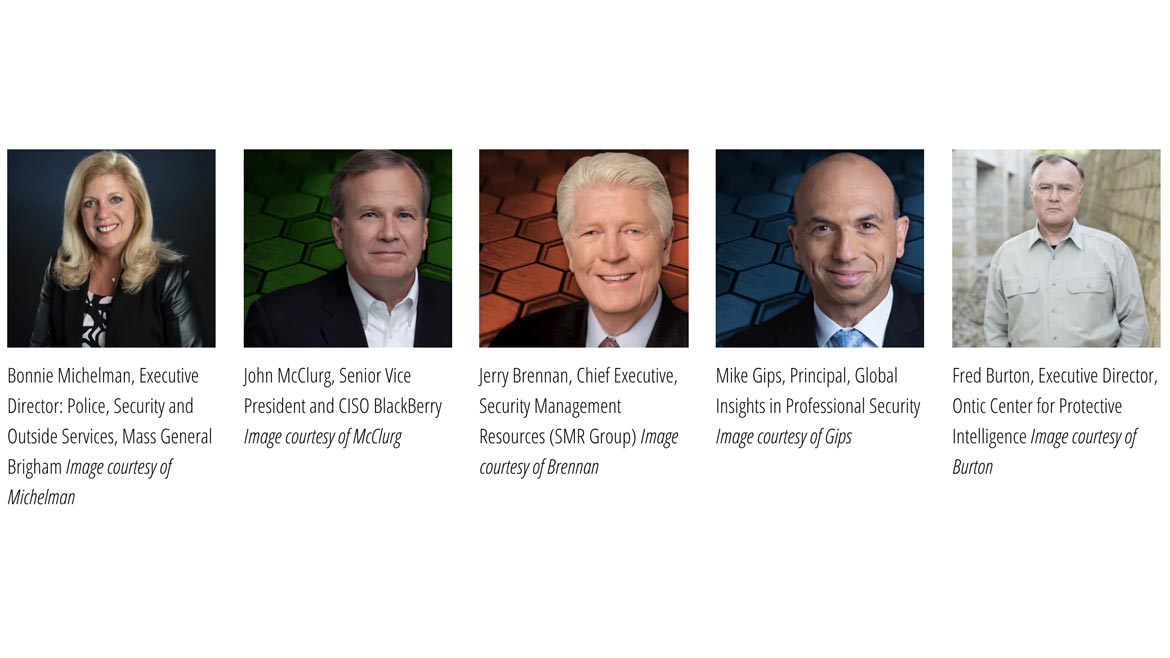
Corporate security strategies have also changed over the past 20 years, notes Jerry Brennan, co-founder and Chief Executive of Security Management Resources (SMR Group) and co-columnist for Security’s Career Intelligence column.
“During that time and the years that followed, there was a shift in how corporate security was viewed and the expectations by senior leadership and their Boards relative to the integration of a proactive approach to a wide range of security risk-related issues,” Brennan says. He adds that in addition to a shift toward incorporating a proactive approach to threats within the enterprise, there was a simultaneous shift in thinking that security programs should be supporting and aligning with an organization’s core business objectives.
One evolution sparked by 9/11, which has transformed how security leaders and security programs can do their jobs within the enterprise is security technology advancements, according to Fred Burton, Executive Director at Ontic Center for Protective Intelligence.
“Having been a part of the intelligence community when I was an agent and then transitioning into the private sector, these are the kinds of events that have this almost tsunami effect across the entire landscape of our country. And from a leadership perspective, as you look back at all the changes that had to be made, one of the more fascinating aspects to me is just the technology evolution that has taken place in this space [since 9/11],” he says. “For many, many years, even when I was an agent in the 80s and the 90s, the whole focus was on your traditional guns, gates and guards, even in the private sector. The technology innovations that have surfaced in many ways as a result of 9/11 have transitioned into the private sector and vice versa, to not only protect corporate America, but also into the public sector as well. The innovation in this space has really been phenomenal as you reflect back.”
As corporate enterprise security strategies have evolved to take a macro-level view to risk and physical security technologies have advanced, another evolution over the past two decades that have affected enterprise security is the overlap of physical and cybersecurity, in strategies, in leadership and in the threat landscape. As Mike Gips, Principal at Global Insights in Professional Security, LLC and Security’s Leadership and Management columnist, reminds us, though Google emerged in 1998, iPhones weren’t invented until 2007, triggering a mobile and technology revolution that continues to infiltrate enterprise security with the proliferation of the Internet of Things (IoT) connected devices throughout an organization — bringing along with them a whole host of risks and vulnerabilities that threaten the enterprise. Physical security technologies such as access control and video surveillance continue to enter and connect to the IoT-sphere within an organization, pulling security leaders across multi-functional groups together for support and risk mitigation.
“Networking undergirds many aspects of physical security, such as access control, video surveillance and visitor management, all of which are available as a cloud-based service. Combined cyber-physical threats now disrupt the sleep of today’s corporate security managers,” Gips says.
But the entrance of cyber-connected risks into enterprise security is not even close to the only additional threat that enterprise security has experienced since 2001. The threat landscape has continued to evolve and widen in myriad ways.
“Besides orienting themselves to cyber processes at the heart of their enterprise, in the last 20 years, security executives have had to address: a surge in nation-state espionage; ever-increasing attacks on soft targets such as schools, theaters and houses of worships; regular pandemics such as SARS, Avian flu and COVID-19; various types of natural disasters; social media threats and disinformation; data privacy issues; social movements leading to civil unrest; sustainability concerns; globalization of teams and functions; various new laws and regulations; and so on,” Gips adds. “It is a constantly changing dance.”
McClurg says that IoT has not only widened the threat landscape over time, but has increased the potential consequences as well. “The implications of asymmetrical warfare have grown more complex and potentially consequential since 9/11 by the exponential growth of and porosity created by IoT. The potential attack vectors are expanding at an incredible pace as our inter-connectivity increases,” he says. “What the adversaries could advance with simple box cutters back on 9/11 can now be advanced with a laptop — with just as much potential physical-world impact, e.g., Colonial Pipeline.”
To combat a threat landscape that has widened, changed and continues to evolve, both Michelman and Brennan say that one of the powerful shifts that has occurred within enterprise security over time is the expansion and role of intelligence within security programs, operational continuity and resilience enterprise-wide, and risk-related decision making.
“Since then, the increase in Board-level concerns on resiliency and continuity of operations, coupled with geopolitical challenges have since resulted in adding or [expanding] intelligence capabilities within organizations. There has been significant growth in the private sector of intelligence staffing and sophisticated operations centers that have been woven into the fabric of corporate security risk programs,” Brennan says. “This has touched every element of their organizations and is continuing to grow at a rapid pace. Predictive analysis is used to support the business case for a wide range of security initiatives.”
Adds Michelman, “Security leaders are leading the helm of managing change, being agile, and having their hand in a lot of different functional areas. This is going to continue. To meet this ever-changing world, security leaders must continue to be active members of the team, not passive, but actual influencers of the process of staying current, being proactive and being an essential part of the business executive team and strategy.”
Editor’s Note: Listen to a special edition of The Security Podcasts as we sit down with 2021 Most Influential recipient, New York Times bestselling author and Executive Director at Ontic Center for Protective Intelligence Fred Burton, for more on his thoughts as he reflects on the 20th anniversary of 9/11.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





