The state of the cybercriminal marketplace landscape following the Empire Market exit scam

Digital Shadows has analyzed the cybercriminal marketplace landscape following the Empire Market exit scam. The company’s research has identified a number of currently available dark web marketplaces popular within the cybercriminal community. Noting the impact of the closure of Empire Market, some marketplaces, such as Icarus Market, have seen a major spike in listings, from 25,000 to 35,000 in the last month.
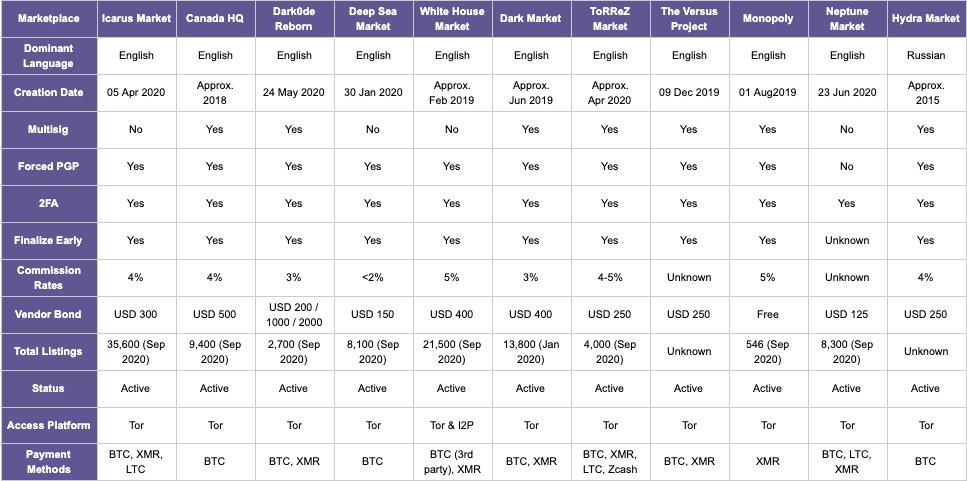
The table below includes a subset of the currently available dark web marketplaces assessed to be popular within the cybercriminal community. The highlighted features indicate factors that cybercriminals may consider when choosing a new market. Some of these were included in a guide published on the dark web community forum Dread covering desired features for a dark web marketplace. According to the guide, a good marketplace should have compulsory multisig and PGP verification and competitive vendor bond rates - terminologies covered in the definitions list below. Digital Shadows also added a few more considerations that they think might play their part.
Definitions:
- Multisig - Does the marketplace enforce multisig, a payment system in which multiple authorizations from different individuals must continue with cryptocurrency transactions? Multisig is considered to provide additional security during transactions.
- Forced PGP - Does the marketplace force its members to sign their communications using Pretty Good Privacy (PGP), an encryption method to prove the legitimacy of messages? PGP is used to reassure cybercriminals they communicate with the real owner of an account rather than an interloper.
- 2FA - Does the market allow two-factor authentication for user accounts? 2FA provides added security.
- Finalize Early - Does the market allow funds to be released before the vendor is satisfied with the transaction? This measure reduces the potential damage from fluctuations in the price of Bitcoin and increases the chance of falling victim to a scam.
- Commission rates - How much commission does the marketplace earn from each transaction?
- Vendor bond - How much does it cost for a vendor to register and list offerings on the marketplace? Higher vendor bonds might put some sellers off but do reduce the chances of scammers registering.
- Access Platform - Which browser platform must be used to access the marketplace?
- Payment Methods - What types of cryptocurrencies are allowed for payment purposes? Bitcoin (BTC), Monero (XMR), Litecoin (LTC)
With all these competing factors to consider, plus the risk of yet another exit scam, you might be asking yourself why cybercriminals persevere with the marketplace format, especially with the availability of other platforms such as forums and encrypted communication applications (Telegram and Wickr), says the Digital Shadows team. Several factors are explaining the continued existence of marketplaces in the current cybercriminal ecosystem.
- Are there any suitable forums?
- Why not choose Russian platforms over English ones?
- How about switching to messaging applications?
According to Digital Shadows, many English-speaking cybercriminals see little choice than to register on new marketplaces that take the place of a recently closed one (and hope that history doesn’t repeat itself) due to the challenges of using foreign-language platforms, the scarcity of English-language forums and the drawbacks of communication applications.
"As we saw with the demise of AlphaBay, Hansa, and Dream Market, when a marketplace’s users are abandoned, they seek sanctuary in another platform. Could the recent explosion in the number of listings that Icarus market hosts indicate that the site is positioning itself to capitalize on the wealth likely to come it’s way? Especially if it attracts a substantial number of new joiners and then executes a text-book exit scam? Only time will tell," writes the Digital Shadows research team. "Like all of us, cybercriminals tend to be creatures of habit. Suppose a marketplace demonstrates it has some security awareness but is also widely accessible through its use of popular cryptocurrencies, attracts top-level vendors, and provides active support to its userbase. In that case, cybercriminals will likely forgo iron-clad security platforms with smaller numbers of vendors and listings in favor of moderately secure platforms with a large number of vendors and products, inevitably restarting the exit scam cycle once again."
For detailed findings and more information, please visit https://www.digitalshadows.com/blog-and-research/with-the-empire-falling-who-will-take-over-the-throne/
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




