How to Manage Physical Asset Risk
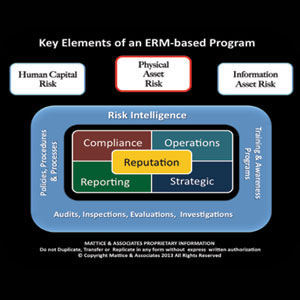
Our journey on the road to transforming to an Enterprise Risk Management based program, one of the more traditional security sweet spots, is our next area of focus.
|
Our journey on the road to transforming to an Enterprise Risk Management based program, one of the more traditional security sweet spots, is our next area of focus. In this month’s column, we will explore why most enterprises can no longer simply depend on “Gates, Guns & Guards” to adequately safeguard their physical assets.
Mitigating risks associated with physical assets covers virtually every type of object known to man. This category of assets ranges from jewels and precious metals to buildings and major infrastructure elements, and everything in between. Physical security mythologies have for years focused on concentric rings of defense. Starting at the outside and working inward with layers of protection measures based on the value of what was being safeguarded, as well as the perceived risk of theft, malicious alteration, or sabotage from human caused actions or damage, inoperability or complete loss due to natural caused events.
Municipal planners have adopted physical security risk mitigation strategies with the advent of Crime Prevention Through Environmental Design (CPTED). The original concepts focused on utilizing a multi-disciplinary approach to deterring criminal behavior through environmental design. CPTED strategies rely upon the ability to influence offender decisions which precede criminal acts.
Today, CPTED concepts are also being utilized to thwart terrorist attacks. For example, designing a building with windows that are constructed of high-strength polycarbonates or coated with blast resistant film not only prevents smash and grab type crimes, but assists in protecting buildings and their occupants from a broad range of explosive devices. Berms, bollards, planters and moats are frequently being utilized as a measure to reduce the likelihood of car or truck bombs from making it within an effective blast range of a building or critical infrastructure element.
Landscaping and lighting also come into play with CPTED. The use of low growing plants and shrubs eliminates potential hiding places. Carefully designing where trees will be located helps to avoid security video blind spots and from them being utilized to gain easy access over fences. CPTED concepts also call for the lower branches of a tree to be trimmed so there is at least an eight-foot clear zone before reaching the first branches.
Effective deployment of access control, coupled with security video and intrusion alarms has become more critical than ever.
Many corporations and building owners have deployed turnstiles of one type or another in lobbies. These turnstiles typically are low in height so they remain more aesthetically pleasing to the eye. Unless you have an armed security officer on the other side, they won’t stop some deranged person from jumping them to commit an act of workplace violence. Similarly, many schools have deployed a double door controlled entry system as an access control measure. In more than one school shooting incident, the shooter simply shot out the large pane glass panel next to the entry way to gain access.
Designing truly effective containment areas for visitors and limiting ingress and egress points are critical elements in physical security risk mitigation, but it can’t stop there. Not unexpectedly, people are the weakest link in maintaining effective physical security controls. Training all employees and/or building occupants, coupled with frequent reminders, relative to their individual responsibilities in maintaining access control is vital.
Never lose sight of the fact that a stable full of lawyers and regulatory compliance agency personnel is anxiously waiting for the opportunity to point out your negligent security liability and regulatory violations. Couple these risks with today’s social media deluge that explodes after every incident, and which is frequently filled with misperceptions and incomplete or inaccurate accounts. At the end of the day, every risk mitigation measure a company takes will be subjected to the harsh light of public opinion, just another element of reputational risk for the enterprise.
About the Authors:
Jerry J. Brennan is the founder and Chief Operating Officer of Security Management Resources (SMR Group), the world’s leading executive search firm exclusively focused in corporate security. Prior to founding SMR in 1997, Brennan enjoyed a 26-year career in domestic and international enterprise risk and security roles. Lynn Mattice is Managing Director of Mattice and Associates, a management consultancy focused at the development and alignment of Enterprise Risk Management and Business Intelligence Programs, as well as Intellectual Property Protection and Cybersecurity. He has more than 35 years of experience heading these programs at the executive level of three major multinational corporations and one mid-cap company in diverse industries.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





