Understanding and Mitigating Financial Asset Risk
How is Cybercrime the new Wild West of Theft?
The type and range of risks affecting financial assets are enormous. From the days of Jesse James and Bonnie & Clyde to the North Hollywood shootout (the violent confrontation between two heavily armed and armored bank robbers and officers of the Los Angeles Police Department in February, 1997), banks have always been a target of those after fast cash. When the notorious bank robber Willie Sutton was asked why he robbed banks, his short and direct response was…“Because that’s where the money is!”
|
In reality, according to the FBI, the number of bank robberies has declined dramatically, with the average bank robbery today typically only netting around $2,500 in cash.
We mustn’t forget to also mention the long list of charlatans that have splashed across our history. Characters like Charles Ponzi, whose name has become synonymous with a whole range of pyramid schemes, always seem to be on the hunt for unsuspecting or greed-inspired victims. The now infamous multi-billion dollar Ponzi scheme by Bernie Madoff focused on the full range of scammer targets.
Obviously, the financial industry is particularly wrought with risk to financial assets. Earlier we mentioned the average take in a bank robbery only being around $2,500, which is a drop in the bucket compared to the virtually risk-free cyber-based expropriation of cash from bank and credit card accounts of businesses of all sizes, as well as from those of unsuspecting individuals. While bank accounts of individuals are covered for fraudulent activity, business bank accounts are not afforded such protection. Many a small business has evaporated overnight due to devastating bank fraud which was committed against them.
A report issued by Symantec in 2011 opined that cybercrime nets more than the combined sales of marijuana, heroin and cocaine. The report stated that more than one million people per day were affected by cybercrime at an estimated loss of more than $338 billion annually. One company recently discovered that its IT systems and networks had been penetrated and the associated exfiltration had gone undetected for four and one half years, despite the exemplary cyber safeguards they had deployed.
Insiders, however, are responsible for the vast majority of financial schemes that companies face today. Fraud, embezzlement, collusion, falsification of records, bribery and kick-back schemes have historically always been a part of life far back into history. However, greed is not always at the heart of all financial asset risk. Desperate senior executives sometimes also take extreme chances with a company’s financial assets. Occasionally they succeed, but the majority of the time they do not. Take Fred Smith, Founder & CEO of FedEx: in 1973 he did not have enough money to make the company’s payroll and keep their planes flying. Smith flew to Las Vegas, played Blackjack, and won enough money to cover keeping the company afloat. He wired the winnings back to the home office…and the rest, as they say, is history. In today’s regulatory intense business world, going to Las Vegas and gambling like Smith did with his company’s money would get him thrown in jail.
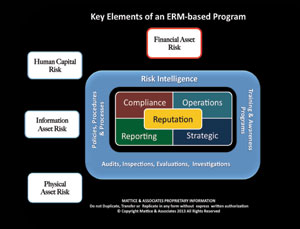
There is much an enterprise can do to effectively manage risks to their financial assets. Establishing detailed procedural checks and balances are extremely important and necessary process controls. Routine audits, coupled with surprise or unannounced audits, ensure to the greatest extent possible that procedural controls are maintained and aberrant behavior is detected. In addition, managers taking the time to monitor their employee’s attendance, validating time cards, payroll and supplier/vendor audits, expense report audits, rebate and warranty claim reviews, budgetary spending limits, additional authorizations for large budgetary expenditures and conducting detailed due diligence reviews anytime a new supply chain or channel partner is engaged are just a few of the basics necessary to safeguard financial assets. And we can’t forget about intellectual property safeguards and anti-counterfeiting measures to guard future earnings and profitability.
Rest assured, virtually every effort that you take to safeguard your enterprises financial assets will be met with equal or even greater efforts by bad actors to relieve your enterprise of those financial assets. So, as the Latin phrase “Semper Vigilare” translates…you must remain Ever Vigilant.
About the Authors:
Jerry J. Brennan is the founder and Chief Operating Officer of Security Management Resources (SMR Group), the world’s leading executive search firm exclusively focused in corporate security. Lynn Mattice is Managing Director of Mattice and Associates, a management consultancy focused at the development and alignment of Enterprise Risk Management and Business Intelligence Programs, as well as Intellectual Property Protection and Cybersecurity.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







