Big Bang Theory: Selecting Technology in Tough Economic Times

“Do your homework” before making any proposals or decisions, said Paul Boucherle, who has solid advice for security leaders working in a tough economic environment.
An almost overwhelming variety of electronic security and surveillance technologies are available today; all with various functions, features and promises that can be both confusing and complex. The ability of technology to incorporate countless streams of data to support real-time (and at times life and death) security decisions is a promising, though complicated and potentially very expensive proposition, especially in a tough economic year.
In fact, if you are not overwhelmed by the velocity of security technology development and the whirlwind of performance claims, you must just be getting back from the last moon shot, because today’s amalgamation of technical components seems to grow exponentially as if catapulted by its own “big bang” theory.
OK, Stephen Hawking I am not and my experience with relativity is mostly limited to family outings. However, the impact of selecting the right security technologies, while a complex undertaking to be sure, need not involve “chaos” theory.
I’d like to share a few tips on how to avoid the confusion and uncertainty that often plague those attempting to make effective financial and technological decisions relating to security solutions for enterprise wide applications. The right decisions can deliver real results along with real return on security investment (ROSI).
MYRIAD TECHNOLOGIES
Consider the wide category of systems that support safety and security in the workplace such as fire alarm, life safety, intrusion detection, video, access control, intercom, critical condition monitoring, asset tracking, parking controls and perimeter protection; to name a few. Making a decision to use a network-centric strategy to provide a safe and productive work environment is the first business decision you must make to leverage the benefits of current and future technology applications.Today’s technology applications can and do contribute business value to the bottom line, especially meaningful this year.
“Doing more with less” is a management mantra all security professionals face in their effort to deliver a safe and secure working environment and still deliver to the bottom line. It will help to ask and answer some key security and business questions before presenting proposals to senior management for new security technologies.
Before you get started, here is a challenge for you.
- How well do you know your own company’s business operations, different department roles and challenges?
- What is the true revenue engine that supports the business?
- Will this security application impact many different departments in a positive way?
- Will the application support specific business goals in measurable ways?
- How will the application reduce, optimize, streamline or improve security/business operations?
- Initial investment?
- External support?
- Internal resources to support?
- Initial and continued training expenses?
- Level of proficiency of operators?
- Maintenance?
- Risk exposure to adopting new technology?
- TCO (total cost of ownership)?
- Impact of a system failure?
- Increasing maintenance costs?
- Increased risk exposure based on past events?
- How a security event impacts the company’s brand?
- Do you have a good working business relationship with senior IT management?
- Is your senior management team strategic with a long view?
- How would you describe your business acumen and relationship with management?
- Can you build inter-department relationships enough to reach a consensus?
- Is it made by a reputable company?
- Is it in good operating condition?
- Can it be maintained or upgraded at a reasonable cost?
- How will your network grow over the next three to five years?
- Who are key stakeholders that will use the system and receive measurable benefit?
- Who should you consider working with to deliver long term business results?
WORK WITH GOOD LISTENERS
Next you must determine if the suppliers you are going to work with are experienced listeners or serial talkers and whether or not they have the business know-how to deliver long term system integration. Why is that important? Because you must share some of the ways your business really works, how different departments work together and what you expect technology to help you accomplish to make the right choices. If your advisors and providers are not active listeners they won’t be able to “hear” you well enough to ask the right questions and recommend the right technology application to deliver the biggest bang for your buck.Everyone can agree that the various technologies and their unique terminologies can be a bit overwhelming. But, it is also important to know that these same technologies, when selected correctly, can greatly simplify security and operational functions, and can result in significant ROSI.
With that in mind, here’s a list of questions based on experience in funding the development and implementation of software applications and advising others on technology development projects over the years. If you take the time to ask yourself and those involved in the selection process these important questions, the answers will help to determine if a specific application solution is right for you.
- Does the technology application(s) you are considering enable the organization to support the short and long term business goals of senior management and shareholders? Senior management will almost always support initiatives that will help them to reach their business goals. How these goals are supported must be clearly and concisely communicated.
- Will the implementation deliver reduced operating costs and mitigate exposure to risk by reducing response times?
- Will it be used in new ways by different departments to improve operational efficiencies and perhaps support revenue growth by improving the perception of the company brand?
- Does the technology application under consideration have measurable return on security investment potential? ROSI is a relatively new concept and therefore may need to be prudently estimated. Think this one through carefully because your management team will be asking it sooner rather than later.
- How will this application save or make your company money? Be specific. Make sure your metrics are attainable and stated in ranges of anticipated results as fixed numbers are extremely difficult to hit accurately. A good technology partner can help you explore this issue more thoroughly by providing experience and objectivity.
- Who is going to use this application?
- Is the application appropriate for the skill level of its primary users? Technology spelled s-o-f-t-w-a-r-e must consider the frequency interface factor of the primary and secondary users. If you don’t use software everyday your proficiency level drops exponentially. Often, companies buy feature rich technology applications and end up using only 20-30 percent of the applications’ full potential. Try justifying that metric to an inquisitive CFO or COO down the road. A good rule of thumb is this -- if the primary users are contract officers, keep it simple. New video analysis software, if chosen and programmed with care, can deliver great results in this scenario.
- Is the application mature, cutting edge, or bleeding edge technology? Let me translate for you from my perspective: Mature means field proven for one to three years in different market segments with 80 percent of the debugging process (software patches) completed. Cutting edge implies that the application has been tested in the field with real customers for at least six months to a year, with 60-70 percent of all bugs identified and with solutions in place. Bleeding edge puts you as the first or second real customer outside the laboratory and you better have a high risk tolerance perspective. Make sure the system integrator and system manufacturer have a close working relationship and make sure a joint meeting is conducted with your team to address the “what if” questions.
- Is the application easy to maintain? If the technology application conforms to standard network protocol, standards and practices, you have half of this question answered. Your senior IT management team will ultimately be the judge of these factors. The second half may be trickier, especially if the application is new or integrates different proven technologies for the first time. The better question is who will maintain this application and how will this be accomplished. Define early in the process how your internal resources will support the application and how your supplier will support the solution. Accountability cannot be taken for granted.
- Does the application fit the organization's strategic IT architecture? There are a couple of issues to consider here, the first being who is the senior management sponsor of this solution and what level of authority do they have to make decisions stick.
- Is the network viewed as a strategic advantage or an overhead cost that must be optimized? If a network is viewed strategically, then innovative and creative ideas deliver applications that support competitive advantage to the business. If viewed as a necessary cost, then expanding the network’s growth can be challenging.
- What is required to support the new technology application? Will support come from internal IT resources or will this support be outsourced? Stretching internal IT resources too thin can result in failure to deliver service on core applications that are vital to the enterprise.
- Does your business have the necessary practices, supplies, personnel and other resources in place and working properly to take advantage of the new technology? If not, your business realistically may not be able to take advantage of new technology applications.
- What type of IT support is available to adapt to and support the new technology? There are many ways to work around these issues including outsourcing IT help on a project by project basis.
- Is it a profitable decision?
- What is the financial impact of not implementing this application, what problems will this solution solve and what are the different options available to solve this problem?
- Does the increase in revenue from all sources, or the decrease in expenses from all sources, offset the change in expenses from all sources needed to use the new technology?
ANTICIPATE ALL COSTS
Will this technology application drive additional expenses? Every new application or solution will have new and sometimes unanticipated costs associated with the implementation. It’s human nature to resist change. Make sure that you chose the right product, system integrator, consultant and the right departments in your company to help with new technology applications to understand how the new solution will impact your bottom line. It’s a career enhancing strategy.Selecting the right technology for the job is no easy task and can certainly lead to a big headache if not a big bang.
The main thing to remember is that new network technology applications can and do have a very strong impact on delivering competitive advantage to the enterprise. Just make sure your game plan is well thought out in advance. Try to keep your chaos at a minimum by seeking internal and external expert advice whenever possible and do your homework.
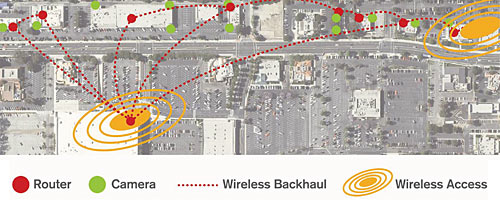
A wireless mesh solution proved cost effective for the owner of the Lakewood Mall.
SIDEBAR: Hitting It Right: Quality video; Low Cost of Ownership
Michael Mercado is a very good listener. As the systems integrator to Lakewood Center Mall in southern California, he learned that the mall needed to install a video surveillance system covering the parking lots and surrounding area of a series of stores and restaurants located across a busy street from the surveillance center. The high cost of running fiber across the street and parking lots as well as the inconvenience and lost tenant revenue associated with digging made a wireless video solution the preferred option.So he worked with Azalea Networks with its wireless mesh network and Active Video Transport technology. “With the location of the coverage area across a busy street from the surveillance center, it could have cost over $100,000 to dig and bury fiber to connect all the cameras,” reported Mercado, president of Electronic Times. Covering an area approximately five square blocks, the wireless mesh network offered Lakewood Center Mall superior video quality for a fraction of the cost of burying fiber. But it also provided a superior video quality solution. The solution leverages a routing technology that preserves video packets, minimizes jitter and maximizes throughput over multiple hops. This ability to maintain maximum throughput over multiple hops allows a network to require fewer gateway nodes, which not only decreases the deployment costs but also permits scaling of the network over time.
SIDEBAR: Making a Successful, Low-cost, High Profile Transition
In tough economic times, it’s what you know that is most important. For some making the transition from a military career, for example, to an enterprise job, certification from ASIS International made a big difference.For Ken Freeman, general manager of SOC Los Alamos, he earned his CPP certification “as part of a test we did in the U.S. Air Force to determine the degree of compatibility between the ASIS body of knowledge – their certification programs -- and Air Force security force developmental experience.” SOC Los Alamos is the laboratory’s protective force subcontract company.
“I believe security certification, and in particular ASIS certification is very relevant in today’s business environment. Over the past decade we’ve seen security increase in importance to business based on a number of factors. This trend continues today. A person who is board certified in security management brings very good credibility, a body of experience capped with the certification itself, and assurance to the business leader that he or she is well-qualified for the challenges at hand.”
Rich Yamamoto, senior director, corporate security and safety at Fannie Mae, was named one of the 25 Most Influential People in the security industry. He is a former U.S. Army Military Police Colonel, former director for security at the U.S. Department of Commerce and recently was elected a director for the 2009 ASIS Board of Directors.
“Certification sets you apart from a wide variety of security practitioners -- it objectively establishes your bona fides. It certainly helped me for promotion to the Federal Senior Executive Service and, more recently, for selection to my current position.” He also pointed out that “it is clear why the Department of Homeland Security awarded the SAFETY Act certification to limit liability for all people holding an ASIS certificate.”
Yamamoto also contended that “ASIS accreditation gives you a competitive advantage like no other. It provides for world class recognition. World class security organizations that I know of tend to have a higher percentage of certified staff than mediocre ones. I have found that the CPP opens doors not otherwise available. It does not guarantee a job but it helps in competing to be on the short list.
Everything else being somewhat equal, the tie breaker is someone who has proven self-discipline to go the extra distance to be competitive. The preparation process itself helps practitioners to break out of their narrow, localized silos and gain a broader, more global view.”
Joe Rector, CPP, PSP, PCI, is deputy chief of security forces for the 316th Security Forces Squadron at Andrews Air Force Base. “I retired from active duty with the Air Force as a Lieutenant Colonel in September 2007. As I began my transition to post-military life, I was offered a number of opportunities in the private sector, but ultimately accepted a senior civil servant position back with the Air Force. As I interviewed for positions in the private sector, I found ASIS certification a big plus. Certification reflects a level of expertise that transcends the military. For those who understand the various certifications, there is common level of expectation of knowledge and experience that one associates with, for example, a CPP. Secondly, holding a certification indicates a commitment to continued education and development
as a person and to the security profession as a whole.”
Rector added, “While professional certifications are a definite plus, most hiring authorities including me still evaluate potential employees on the whole person concept. This involves looking at their breadth and depth of experience, technical expertise, demonstrated leadership ability and education and seeing how this matches up with the requirements for the position for which they are being considered.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




