Product Spotlight on Healthcare
Security magazine highlights a few healthcare security products for 2026.

Healthcare is undoubtedly a critical aspect of everyday life. Unfortunately, this also makes it a prime target for attack from bad actors. This makes it essential for security leaders to constantly keep security and safety at the forefront of their minds when it comes to healthcare systems. Not only for the patients, but for everyone inside a facility.
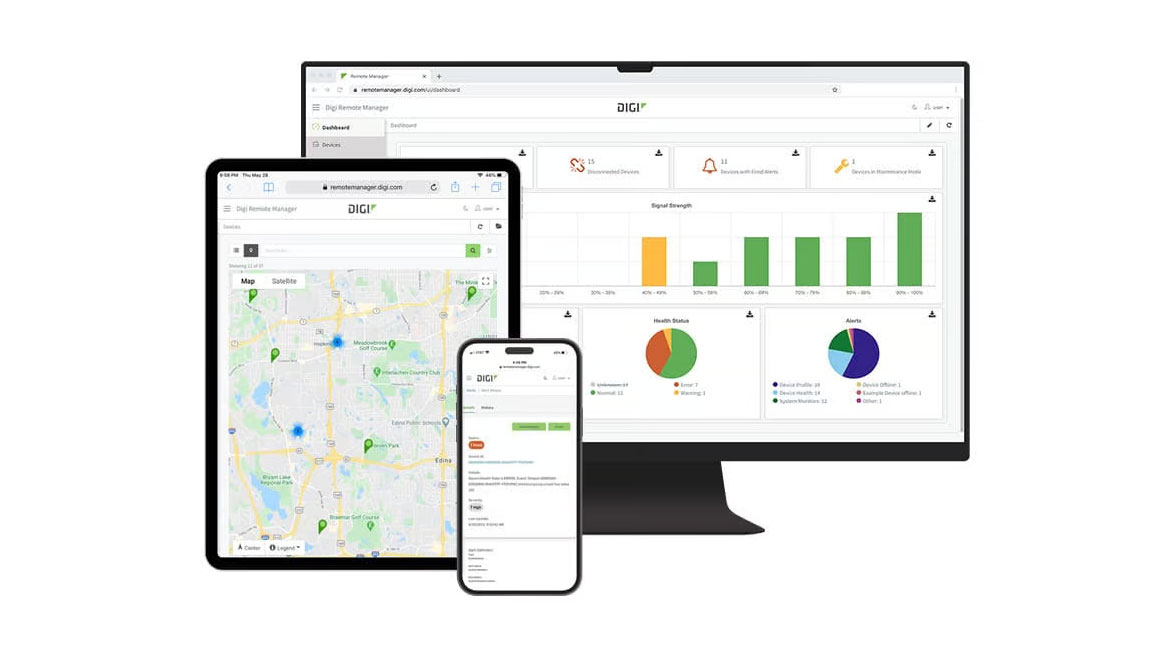
Digi
Deploys Devices Rapidly
Digi’s report manager allows for rapid device deployment and easier asset management. Users can monitor IoT devices, asset performance and security with bi-directional communications. The platform automates mass firmware and software updates to enhance functionality, stay in compliance and scale deployment. Users can access data from edge devices that were previously out of reach. Image courtesy of Digi
Find out more at www.digi.com

ORDR
Follows Commands to Analyze Data
Powered by an integrated network of specialized AI agents, ORDR IQ doesn't just retrieve information; it analyzes it, acts on it, and does so in seconds instead of hours. Security teams can ask questions in natural language, and ORDR IQ will answer and triage incidents, generate dashboards, write and deploy policies, and even send them directly to network switches through ORDR's AI Protect for Security code all with human approval. Image courtesy of ORDR
Find out more at https://ordr.net/

Pedestal Pro
Allows For Emergency Calls in Remote Locations
Blue light emergency towers increase visibility and response speed in a variety of settings. They can be installed on campuses or within parking lots to allow users to immediately connect with emergency services, even when cell service is disrupted. Image courtesy of Pedestal Pro
Find out more at www.pedestalpro.com

Traka
Manages Medication Access
Traka’s Medication Distribution Lockers (MDLs) provide a secure, automated solution for managing patient-specific medication access in healthcare environments. The system allows staff to load individually prescribed doses into secure locker compartments, each assigned to a specific patient. When it’s time for medication pickup, patients authenticate using a biometric fingerprint reader, enabling fast, discreet access without waiting in line or relying on staff availability. Image courtesy of Traka
Find out more at www.traka.com

Xtract One
Uses AI to Scan Visitors and Detect Threats
SmartGateway delivers individual screening, utilizing AI-powered sensors to unobtrusively scan for weapons and other prohibited items upon entry. This technology replaces intimidating, traditional metal detectors and mitigates the need for individuals to remove personal items. SmartGateway is designed to enable seamless passage through checkpoints and promote the uninterrupted flow of movement. Image courtesy of Xtract One
Find out more at xtractone.com
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






