Product Spotlight
Product spotlight on video surveillance solutions

Video surveillance often plays a key role in securing physical locations. Cameras can monitor perimeters and internal spaces, alerting security leaders to suspicious activity.
Security magazine highlights a number of video surveillance solutions, including cameras and video management software (VMS).

AXIS COMMUNICATIONS
Classify moving objects while recording
The AXIS Q1805-LE cameras features a deep learning processing unit for improved processing capabilities. This allows users to collect and analyze data on the edge. It also delivers metadata facilitating forensic search capabilities. The camera is able to detect and classify moving objects. Image courtesy of Axis Communications
FIND OUT MORE AT AXIS.COM
EAGLE EYE NETWORKS
Connect cameras directly to cloud
The Eagle Eye Camera Direct Complete connects cameras directly to the cloud for video management. Because the cameras are connected to the cloud, the cameras can be added to existing video management software accounts or new accounts. Camera Direct Complete includes artificial intelligence (AI)-based smart video search and smart layouts. The cameras require less onsite equipment to set up, making it easier for smaller locations with limited space. The system is designed for four or fewer cameras and will store video locally in the event of a connectivity loss. Image courtesy of Eagle Eye Networks
FIND OUT MORE AT EEN.COM

GENETEC
Monitor threats from a mobile device
Genetec Mobile provides mobile video surveillance and analytics. The updated version includes a tab to monitor all cameras in one location. The system includes intrusion detection to inform users of suspicious activity and incidents with the help of intrusion alerts. Users can arm and disarm intrusion zones, bring contextual video when alarms are triggered, see which input triggered the intrusion alarm, and acknowledge intrusion events. Image courtesy of Genetec
FIND OUT MORE AT GENETEC.COM

HAILO-15
Detect threats in low light
The Hailo-15 vision processors integrate directly into cameras. They’ve been used in city security, manufacturing, retail and transportation. They can recognize real-time emergencies such as broken machinery, trespassers and lost/unaccompanied children. The added AI capacity can be utilized for video enhancement and better video quality in low-light environments, video stabilization and high dynamic range performance. The Hailo-15 offloads cloud analytics to save video bandwidth and processing while improving overall privacy due to data anonymization at the edge. The Hailo-15 vision processers are engineered to consume little power, making them suitable for IP cameras and enabling the design of fanless edge devices. Image courtesy of Hailo
FIND OUT MORE AT HAILO.AI
HANWHA VISION
Classify objects and withstand severe weather
The TNM-P9022EPT3-Z camera from Hanwha Vision allows for AI-based image classification. The camera is designed with corrosion-resistant, marine-grade aluminum with an IP66/67 Type 4X rating for protection against water and dust particles and is certified to withstand temperatures ranging from -20°C to 55°C. The enclosure also features a breather drain membrane system incorporated into the housing design: air within the enclosure is allowed to equalize with the surrounding atmosphere, preventing interior condensation and negating any potential damage to the onboard electronics. Image courtesy of Hanwha Vision
FIND OUT MORE AT HANWHAVISIONAMERICA.COM

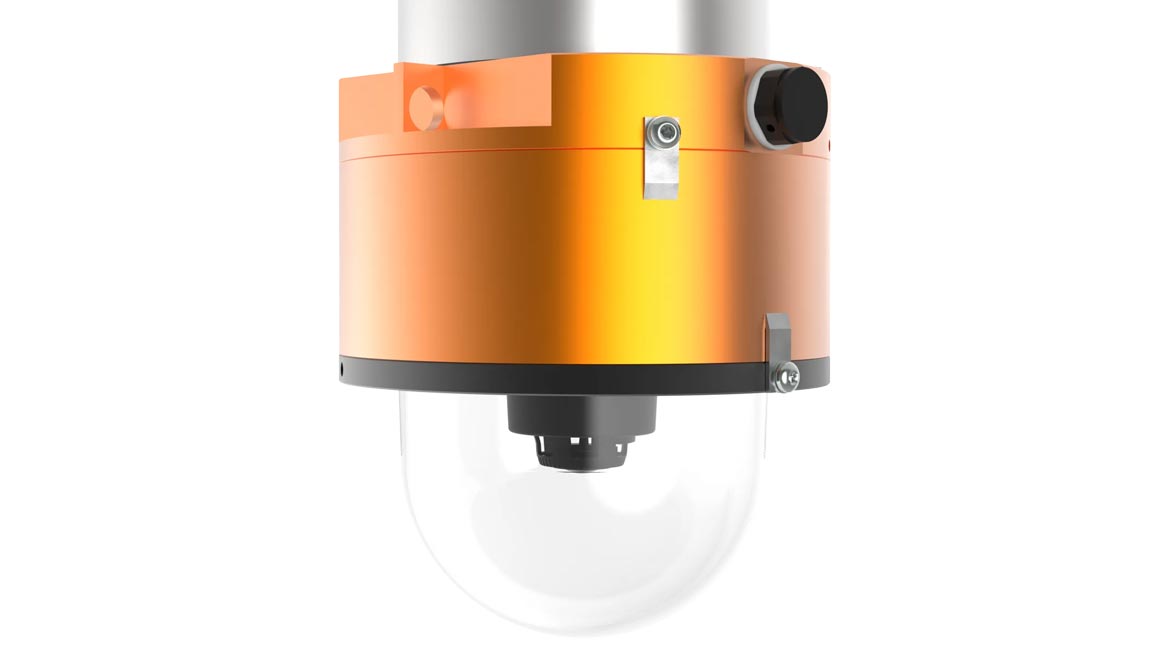
I-PRO
Track objects crossing the perimeter
The i-PRO X-Series Camera turns non-AI network cameras into comprehensive AI smart devices. The onsite AI learning feature lets users teach the camera about custom objects they wish to identify and search for or track. For example, operators could teach the camera to count forklifts passing through the camera’s field of view to provide new metrics about operational efficiency. A hospital could count ambulances arriving at the emergency room. Image courtesy of i-PRO
FIND OUT MORE AT I-PRO.COM
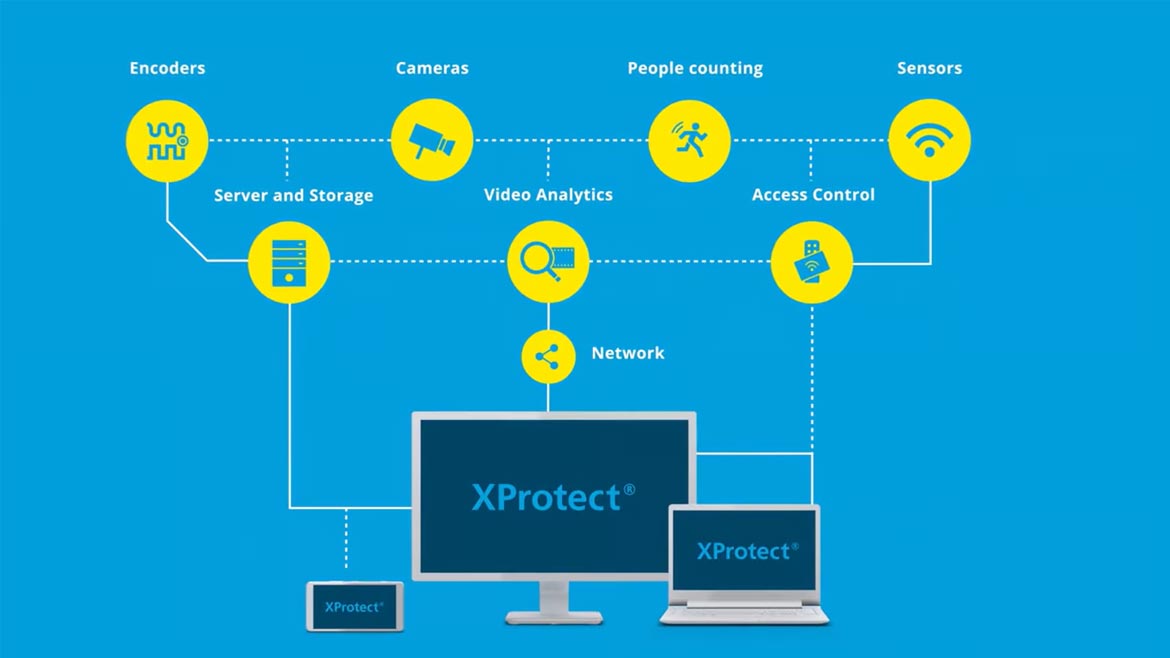
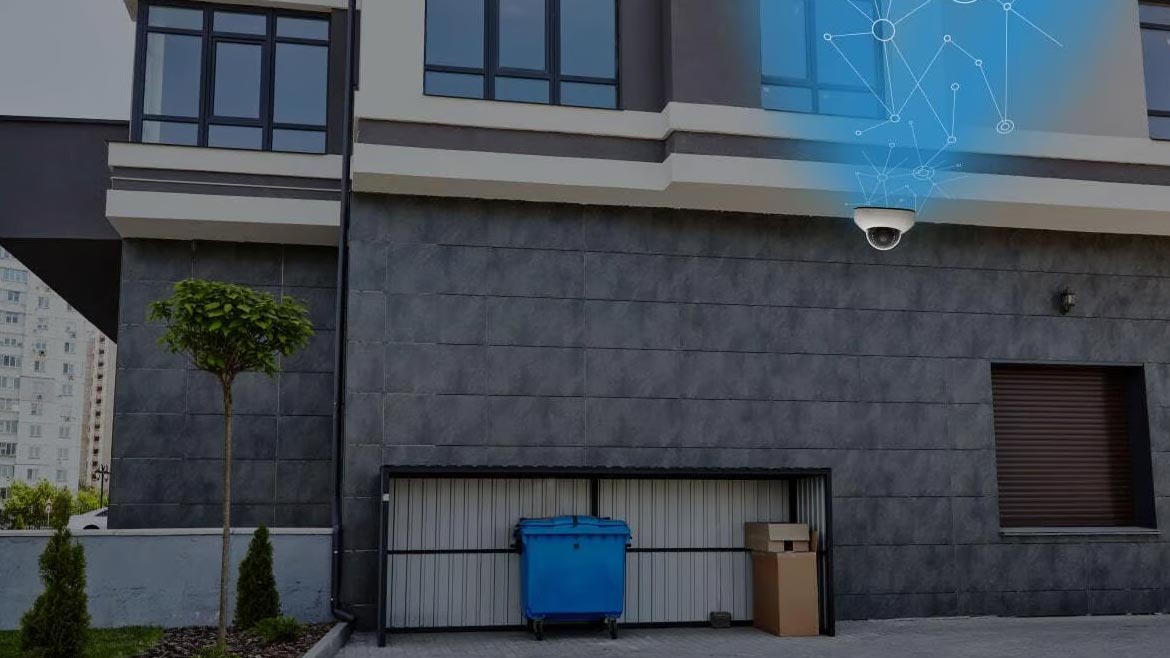
MILESTONE
Monitor video while completing tasks
Milestone XProtect was updated to include bookmarks sharing, background picture in picture and native screenshots. The program includes situational awareness capabilities with smart maps in the mobile setting. This feature provides operators with a map-based overview of cameras and devices. The background picture-in-picture allows operators to monitor specific cameras while completing other tasks. Image courtesy of Milestone
FIND OUT MORE AT MILESTONESYS.COM

RHOMBUS
Capture a 360° view of large rooms
Rhombus security cameras provide real-time de-warping of 360° footage, allowing users to monitor large areas from multiple angles and ensure nothing is out of frame or missed. The fisheye cameras work in stadiums, showrooms and other large open spaces. The camera’s platform allows users to dive into the video and move around within the scene. Image courtesy of Rhombus
FIND OUT MORE AT RHOMBUS.COM

QOGNIFY
View live surveillance footage
Qognify VMS 7.4 is the latest version of Qognify’s video management software (VMS). The updates include live video viewing, playback and investigation capabilities in the hands of the people who need it — whether on patrol, offsite or in the control room. Incident response and investigations are also accelerated, which now supports metadata streams from additional cameras, as well as through a suite of AI-based video analytics. Image courtesy of Qognify
FIND OUT MORE AT QOGNIFY.COM
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








