Security Enterprise Services
Fraud schemes amid COVID-19
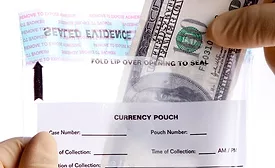
Fraudsters are taking advantage of the pandemic and increasing the threat landscape for governments and enterprises around the world in a wide-reaching fashion.
February 10, 2021
Best practices on integrating access control, biometrics with swing doors and security entrances
There needs to be a solid strategy to ensure security when using an electronic access control system (ACS) and secured entrance devices.
February 9, 2021
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing