Security Leadership and Management
Special Recognition
CEO, Cardinal Point Strategies
Read More
Government
Security's Most Influential People in Security 2020 - Paul Abbate
Associate Deputy Director, Federal Bureau of Investigation (FBI)
September 3, 2020
Security's Most Influential People in Security 2020 - Chief Carmen Best
Chief of Police, Seattle Police Department
September 3, 2020
Government
Security's Most Influential People in Security 2020 - Rebecca Morgan
Chief Insider Threat Division Center for Development of Security Excellence (CDSE), Defense Counterintelligence and Security Agency (DCSA)
September 3, 2020
Government
Security's Most Influential People in Security 2020 - Tyne Truong
Assistant Special Agent in Charge, U.S. Department of Homeland Security, Homeland Security Investigations
September 3, 2020
Cybersecurity
Security's Most Influential People in Security 2020 - Sounil Yu
CISO-in-Residence, YL Ventures
September 3, 2020
Cybersecurity
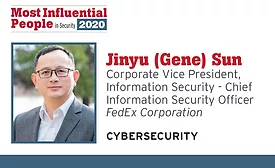
Security's Most Influential People in Security 2020 - Jinyu (Gene) Sun
Corporate Vice President of Information Security/Chief Information Security Officer, FedEx Corporation
September 3, 2020
Cybersecurity
Security's Most Influential People in Security 2020 - Joyce Hunter
Executive Director, The Institute for Critical Infrastructure Technology
September 3, 2020
Cybersecurity
Security's Most Influential People in Security 2020 - Kurt John
Chief Cybersecurity Officer, Siemens USA
September 3, 2020
Cybersecurity
Security's Most Influential People in Security 2020 - Paul Lanois
Director of Technology, Outsourcing and Privacy Fieldfisher
September 3, 2020
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing