Home » cyber security
Articles Tagged with ''cyber security''
5 steps to create an effective, collaborative cybersecurity team
Read More
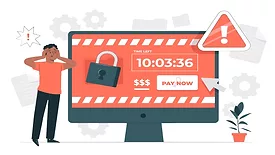
APIs and cloud applications are CISOs’ greatest threats
Zero trust, partner risk management help mitigate security challenges
June 8, 2022
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing