Home » network security
Articles Tagged with ''network security''
24-Port Gbps Managed Power Over Ethernet Switch
Designed to Protect the Network
March 1, 2018
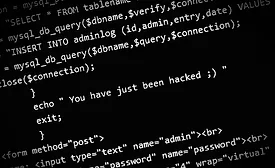
Simulates Attacks on Networks to Test Responses, Security Levels
Red Team from NTT Security
December 1, 2016
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing