Data shows regulatory password compliance falls short

Image via Freepik
Organizations of all kinds look to regulatory recommendations and standards for guidance on constructing a secure password policy for their networks. However, new research shows that regulatory password complexity and construction recommendations are insufficient.
According to the Specops research, which analyzed over 800 million known compromised passwords, up to 83% of passwords that appear in compromised password databases would otherwise satisfy regulatory password standards. The team compared the construction rules of five different standards against a dataset of 800 million compromised passwords.
The following regulatory standard rules were investigated:
- NIST
- HITRUST for HIPAA
- PCI
- ICO for GDPR
- Cyber Essentials for NCSC
Quite a few of these standards include a recommendation or requirement to also use a known compromised password list to prevent the use of breached passwords, and for a good reason. The following chart shows what percent of the known compromised password dataset would otherwise fulfill regulatory recommendations.
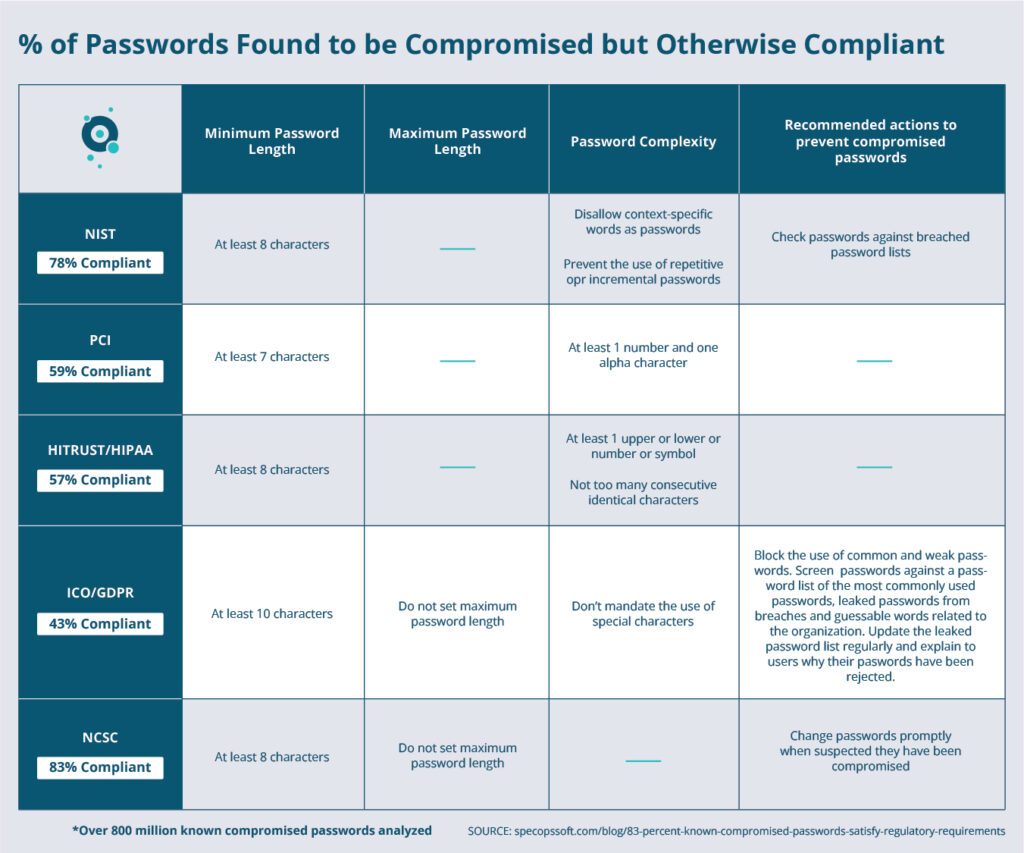
Image courtesy of Specops
1. Almost NCSC (Cyber Essentials) Compliant Compromised Passwords
NCSC, the National Cyber Security Centre, is a part of the United Kingdom government that provides advice and support for the public and private sectors on avoiding computer security threats. The NCSC’s approved accreditation scheme, Cyber Essentials, outlines a standardized baseline for cyber security policies, controls, and technologies. Cyber Essentials is mandatory for government contracts that involve handling personal information, or provisioning certain products and services.
The Cyber Essentials password requirements include:
- set a minimum password length of at least 8 characters
- do not set a maximum password length
- change passwords promptly when suspected they have been compromised
When the Specops team analyzed the compromised password dataset for passwords that are 8 characters or more, they found that 82.98% of the passwords fulfilled that requirement.
Some examples of the nearly 83% otherwise compliant passwords:
- malcom01
- maidmarian
- magvai87magvai87
- maggie1987
- madrilena
2. Almost ICO/GDPR Compliant Compromised Passwords
The General Data Protection Regulation (GDPR) requires organizations to take care of protecting EU citizen data and privacy. The regulation provides no specific password guidance, but the Information Commissioner’s Office (ICO), which is responsible for enforcing the regulation, does provide some non-binding guidance, including:
- Password length: Minimum length should be 10 characters and there should be no maximum.
- Password complexity: Don’t mandate the use of special characters.
- Password deny list: Block the use of common and weak passwords.
Screen passwords against a password list of the most commonly used passwords leaked passwords from breaches, and guessable words related to the organization. Update the leaked password list regularly and explain to users why they their passwords have been rejected.
When the Specops team analyzed the compromised password dataset for passwords that would fulfill these recommendations, they found that 43.48% of the compromised passwords would meet the password length standard.
Some samples of the 43% otherwise-compliant compromised passwords:
- ihatekittens
- ihatebrent
- ihateapples
- igor5062489
- igor454645
3. Almost HITRUST/HIPAA Compliant Compromised Passwords
Formed in 2007 to fill the gap in the often found to be vague requirements of HIPAA, the Health Information Trust (HITRUST) offers a framework to comply with standards such as ISO/IEC 27000-series and HIPAA.
Some of the password guidance provided by HITRUST includes:
- Minimum of 8 characters
- At least 1 upper or lower or number or symbol
- Not too many consecutive identical characters
The Specops team defined “not too many consecutive identical characters” 4 or more, and found 56.87% of the compromised password dataset fulfilled the above guidance.
Some examples of the otherwise-compliant nearly 57% compromised passwords:
- freedom1321
- freddie43
- fortview0122015
- forrest55
- foolish16
4. Almost PCI Compliant Compromised Passwords
The major credit card companies – Visa, Mastercard, and American Express – established Payment Card Industry Data Security Standards (PCI DSS) guidelines in 2006 in an effort to protect credit card data from theft. PCI v3 has 12 Requirements; Requirement 8 covers identifying and authenticating access to system components and includes the following password recommendations:
- Minimum 7 characters
- At least 1 number and one alpha character
The Specops team analyzed the compromised password dataset for passwords that met the above criteria and found that 59.14% of the dataset matched those requirements.
Some samples of the 59% otherwise compliant passwords:
- 22pink22
- 21dog657
- o1livia
- beatrice.99
- klippen5
5. Almost NIST Compliant Compromised Passwords
NIST, the National Institute of Standards and Technology, sets the information security standards for federal agencies (or organizations looking to do business with those agencies) in the United States. Through the NIST Special Publication 800-63B Digital Identity Guidelines, NIST provides best practices related to authentication and password lifecycle management. In this publication,
NIST outlines several best practices to bolster password security, including:
- Minimum password length of 8 characters
- Prevent the use of repetitive or incremental passwords
- Disallow context-specific words as passwords
- Check passwords against breached password lists
The Specops team analyzed the 800 million compromised password dataset for passwords that met a minimum length of 8 characters and did not use repetitive or incremental characters, and found 78.27% of the known compromised password dataset to fulfill those two recommendations. The repetitive/incremental check included looking for character repetition of at least 3 (aaa, bbb, ccc) and sequences of 123, 234 etc. In a real-world setting, context-specific checks such as preventing usernames and business-related words would drive this down further.
Some examples of the 78% otherwise compliant passwords:
- password1
- qwertyuiop
- 1q2w3e4r5t
- iloveyou
- myspace1
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





