Product Spotlight
Product spotlight on access management

Access management security technology can help enterprise security leaders manage identities and physical access across different departments — which is essential to safeguarding workplaces, assets and facilities.
Security magazine highlights a few access management technologies that can help enhance security measures enterprise-wide.
AIPHONE
Access Control Integrates With Video Intercom Systems
 Aiphone Corporation’s IX Series intercoms are integrated with Genetec Security Center to enable Aiphone IX Series users to incorporate their video intercom systems as part of a larger unified security platform. Security Center, an open platform that integrates with a number of systems and sensors, provides enhanced systems management and integration between security systems, including access control, video surveillance and alarms. With integration, video from Aiphone’s video intercoms can be recorded within the Genetec Security Center, while also streaming live or being viewed during an intercom call within the Sipelia Communication Module. Commercial property, business, school and healthcare facility security teams can keep a record of interactions between personnel and visitors when the IX Series intercom system is used to request entry. Image courtesy of Aiphone
Aiphone Corporation’s IX Series intercoms are integrated with Genetec Security Center to enable Aiphone IX Series users to incorporate their video intercom systems as part of a larger unified security platform. Security Center, an open platform that integrates with a number of systems and sensors, provides enhanced systems management and integration between security systems, including access control, video surveillance and alarms. With integration, video from Aiphone’s video intercoms can be recorded within the Genetec Security Center, while also streaming live or being viewed during an intercom call within the Sipelia Communication Module. Commercial property, business, school and healthcare facility security teams can keep a record of interactions between personnel and visitors when the IX Series intercom system is used to request entry. Image courtesy of Aiphone
Find out more at www.aiphone.com
ALLEGION
Helps With Facility Management
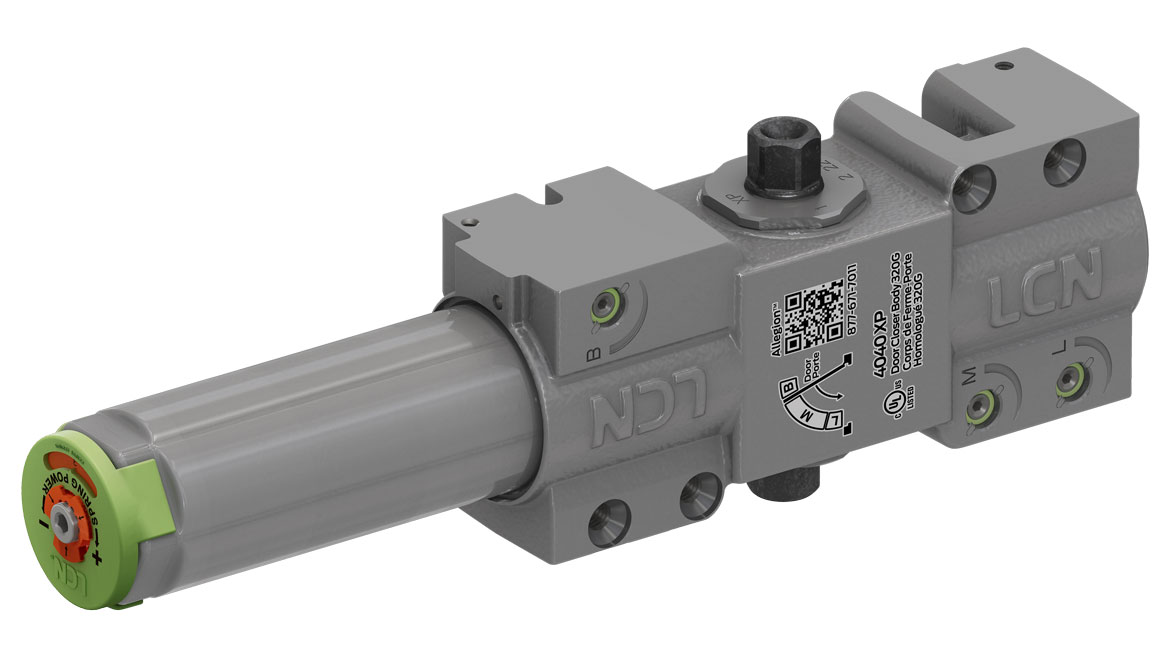 Allegion USLCN 4040XP door closer is a non-handed, surface-mounted heavy-duty closer, designed for high-use-and-abuse applications. The enhancements to the LCN 4040XP door closer include a patent-pending positive stop staking feature that prevents screws from being backed out; labeled regulation valves and corresponding diagram to make adjustments easy; enhanced green dial that simplifies spring power adjustment; and more. Image courtesy of Allegion
Allegion USLCN 4040XP door closer is a non-handed, surface-mounted heavy-duty closer, designed for high-use-and-abuse applications. The enhancements to the LCN 4040XP door closer include a patent-pending positive stop staking feature that prevents screws from being backed out; labeled regulation valves and corresponding diagram to make adjustments easy; enhanced green dial that simplifies spring power adjustment; and more. Image courtesy of Allegion
Find out more at www.lcnclosers.com
ALTRONIX
Combines With Access Control Providers
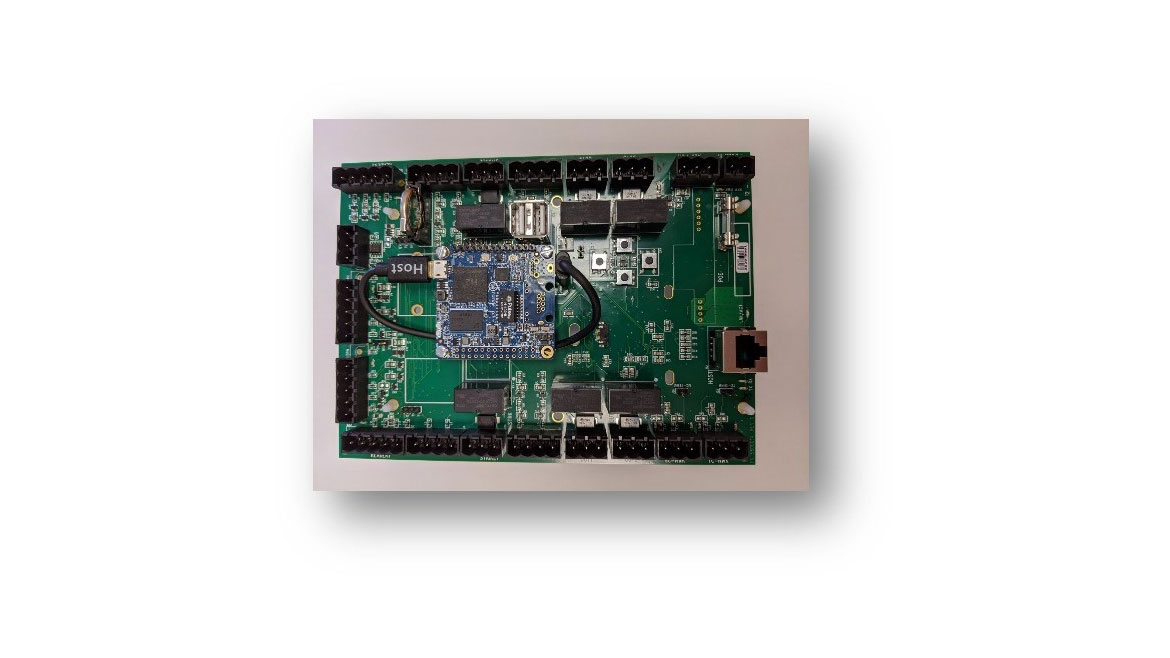
 Altronix Trove Access and Power Integration Solutions have been expanded to support more access control brands, including Inner Range, Kisi and Suprema, as well as DIN rail mount solutions ICT and TDSi. Altronix Trove Access and Power and Integration series combines Altronix accessories with access controllers available from several manufacturers. A variety of backplanes offer a range of access and power configurations. These solutions can help enterprise security leaders simplify board layout and wire management. The solutions are NDAA and TAA compliant. Image courtesy of Altronix
Altronix Trove Access and Power Integration Solutions have been expanded to support more access control brands, including Inner Range, Kisi and Suprema, as well as DIN rail mount solutions ICT and TDSi. Altronix Trove Access and Power and Integration series combines Altronix accessories with access controllers available from several manufacturers. A variety of backplanes offer a range of access and power configurations. These solutions can help enterprise security leaders simplify board layout and wire management. The solutions are NDAA and TAA compliant. Image courtesy of Altronix
Find out more at www.altronix.com
BOSCH SECURITY
Integrates Access Control With Video Management System
 Bosch’s access control software is an access management system for medium- to large-sized applications. It offers data security features and integration with third-party systems. Three software options offer each a range of cardholders and doors, enabling an upgrade when an organization grows. Up to 400,000 cardholders and up to 10,000 doors can be administered in the largest bundle. Existing floor maps are imported into the system, and icons are dragged and dropped to represent controllers, doors and building objects on the map view. Image courtesy of Bosch
Bosch’s access control software is an access management system for medium- to large-sized applications. It offers data security features and integration with third-party systems. Three software options offer each a range of cardholders and doors, enabling an upgrade when an organization grows. Up to 400,000 cardholders and up to 10,000 doors can be administered in the largest bundle. Existing floor maps are imported into the system, and icons are dragged and dropped to represent controllers, doors and building objects on the map view. Image courtesy of Bosch
Find out more at www.boschsecurity.com
HID
Helps Secure Access Through Several Facilities
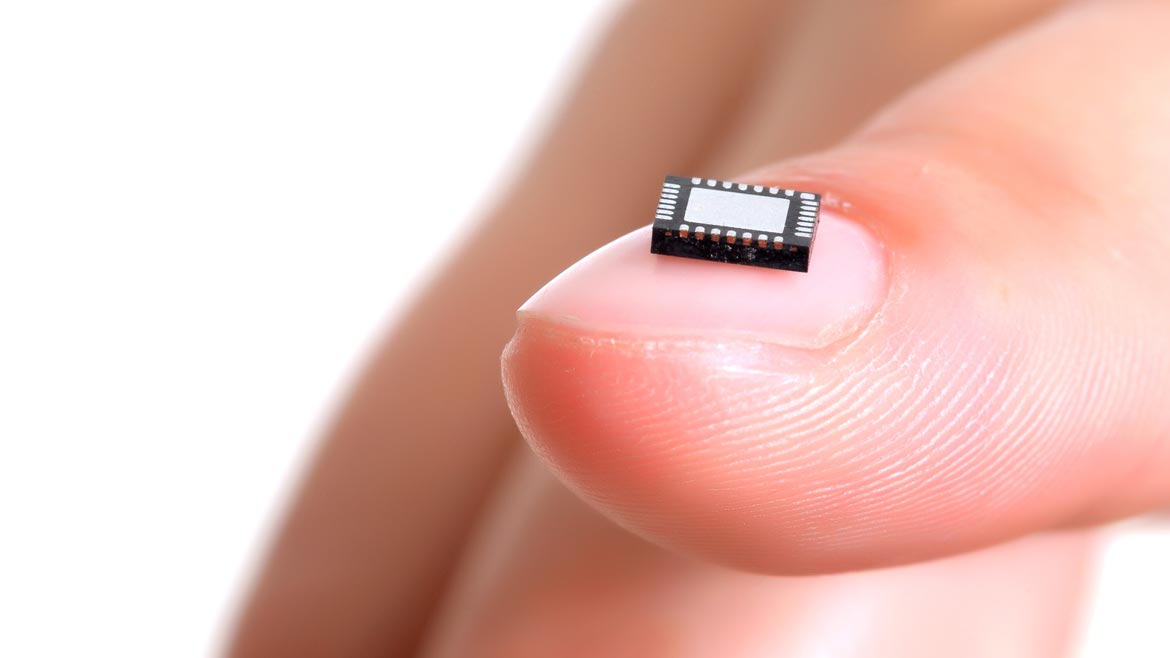 HID OMNIKEY Secure Element can help to support applications in connected workplaces, healthcare environments, education campuses, office buildings, and more. It supports credential technologies, including mobile IDs and employee badges in Apple Wallet, while enabling secure access identification and authentication applications. The single-chip OMNIKEY Secure Element represents a safe key for leveraging Seo credential technology, such as multi-application converged access on mobile phones. It also supports other technologies and can be used for other card protocols. It is designed to deliver security extensions for reader devices across many connected business applications, such as secure print, time and attendance that span multiple “smart” offices, universities or healthcare or government facilities. Image courtesy of HID
HID OMNIKEY Secure Element can help to support applications in connected workplaces, healthcare environments, education campuses, office buildings, and more. It supports credential technologies, including mobile IDs and employee badges in Apple Wallet, while enabling secure access identification and authentication applications. The single-chip OMNIKEY Secure Element represents a safe key for leveraging Seo credential technology, such as multi-application converged access on mobile phones. It also supports other technologies and can be used for other card protocols. It is designed to deliver security extensions for reader devices across many connected business applications, such as secure print, time and attendance that span multiple “smart” offices, universities or healthcare or government facilities. Image courtesy of HID
Find out more at www.hidglobal.com
HONEYWELL
Provides Access Control, Video Surveillance & Intrusion Detection
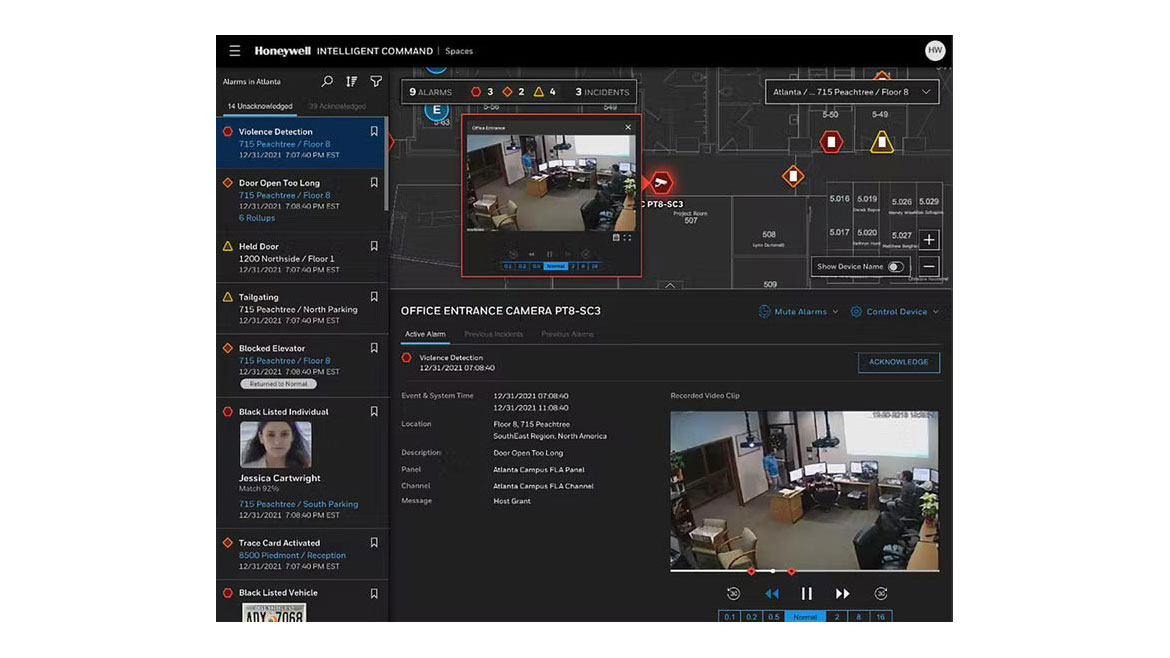 Honeywell Pro-Watch 6.0, part of the Pro-Watch Integrated Security Suite platform, provides integrated access control, video surveillance and intrusion detection to protect staff and property, and comply with industry regulations. The software features a video analytics event feed for situational awareness and mapping capabilities with a view of alarms and maps. The platform integrates with a number of access control hardware. Pro-Watch uses advances in artificial intelligence to help collect and analyze data from multiple systems. When an abnormal situation is detected, the location of the incident is represented on a building map, and an incident workflow is created. Image courtesy of Honeywell
Honeywell Pro-Watch 6.0, part of the Pro-Watch Integrated Security Suite platform, provides integrated access control, video surveillance and intrusion detection to protect staff and property, and comply with industry regulations. The software features a video analytics event feed for situational awareness and mapping capabilities with a view of alarms and maps. The platform integrates with a number of access control hardware. Pro-Watch uses advances in artificial intelligence to help collect and analyze data from multiple systems. When an abnormal situation is detected, the location of the incident is represented on a building map, and an incident workflow is created. Image courtesy of Honeywell
Find out more at www.honeywell.com
MORSE WATCHMANS
Secures and Manages Keys, Cards and More
 Morse Watchmans KeyWatcher Touch system is a key control solution for organizations looking to secure, manage and track keys, card modules and other assets. With a 7” touchscreen SmartKey system with KeyAnywhere technology, security operators can withdraw and return a key securely to key cabinets located within an enterprise. The system includes KeyWatcher TrueTouch key inventory software for enhanced administration and control of the KeyWatcher Touch system. Security operators can create profiles to assign users key and group permissions, access level and other settings. Image courtesy of Morse Watchmans
Morse Watchmans KeyWatcher Touch system is a key control solution for organizations looking to secure, manage and track keys, card modules and other assets. With a 7” touchscreen SmartKey system with KeyAnywhere technology, security operators can withdraw and return a key securely to key cabinets located within an enterprise. The system includes KeyWatcher TrueTouch key inventory software for enhanced administration and control of the KeyWatcher Touch system. Security operators can create profiles to assign users key and group permissions, access level and other settings. Image courtesy of Morse Watchmans
Find out more at www.morsewatchmans.com
SIELOX
Access Control Solution for SMBs and Large Enterprises
 Sielox Pinnacle 11.0 Access Control Platform is an event-management software solution that can accommodate a number of access control applications, ranging from retail and small businesses (SMBs) to stand-alone buildings, multi-tenant complexes and enterprise-level campuses. Features available with Pinnacle include: time zones and holidays with expanded configuration (e.g., scheduled and repeatable intervals daily, weekly, monthly, yearly; different holidays by controller) and email notification. Additional legacy features include the ability to execute local, regional or global lockdowns, event link with camera and/or cardholder image displays, programmable privileged access levels, smart and traditional elevator controls, and more. Image courtesy of Sielox
Sielox Pinnacle 11.0 Access Control Platform is an event-management software solution that can accommodate a number of access control applications, ranging from retail and small businesses (SMBs) to stand-alone buildings, multi-tenant complexes and enterprise-level campuses. Features available with Pinnacle include: time zones and holidays with expanded configuration (e.g., scheduled and repeatable intervals daily, weekly, monthly, yearly; different holidays by controller) and email notification. Additional legacy features include the ability to execute local, regional or global lockdowns, event link with camera and/or cardholder image displays, programmable privileged access levels, smart and traditional elevator controls, and more. Image courtesy of Sielox
Find out more at www.sielox.com
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





