Enterprise Services
Centralized supply chain security programs yield efficiency
Finding efficiencies in supply chain security is as simple as enveloping more of your supply chain. Kirsten Provence has led Boeing’s supply chain security program for nearly a decade; here she explains what has propelled efficiency gains by scaling the program using subsidiaries.

janiecbros / E+ via Getty Images
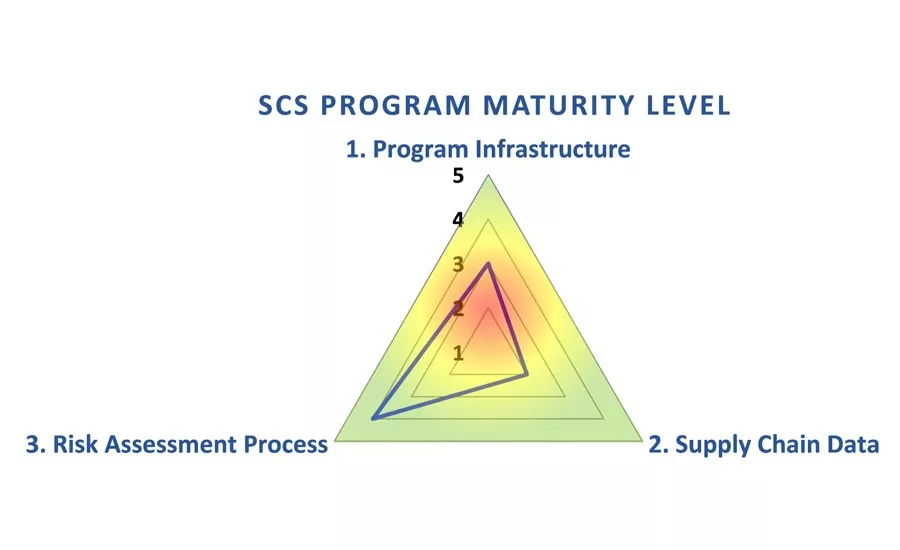
A multi-faceted program health assessment enables all parties to identify where the strengths and weaknesses are in the supply chain security program. Chart courtesy of Provence
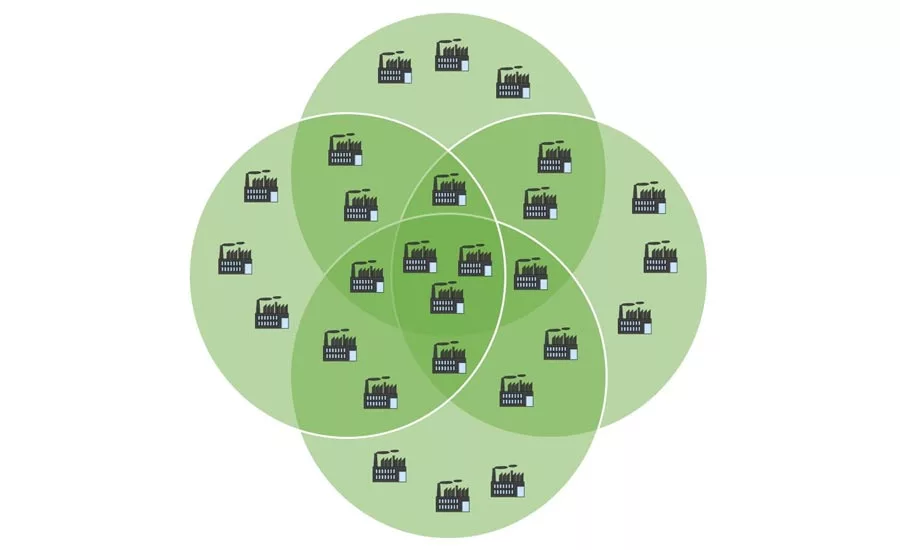
As illustrated in this diagram, conducting an assessment of the suppliers in the center enables each corporate entity to not only meet its vulnerability assessment commitments, but the efforts also provide valuable multi-tier security intelligence. Chart courtesy of Provence
Finding efficiencies in supply chain security is as simple as enveloping more of your supply chain. Leading Boeing’s supply chain security program for nearly a decade, I will explain what has propelled efficiency gains by scaling the program using subsidiaries.
When corporations first start to embark on the effort of tying subsidiary partners into a single supply chain security business model, many recognize that there are two entity types; those that were certified in a program and those that weren’t, but should be. It is critical that a strong and simple set of governance controls be instituted to enable a single program framework and, more importantly, clearly define roles, responsibilities and requirements between organizations.
Many corporations have established and dedicated teams to focus on programs like supply chain security, whereas smaller companies that get acquired often have multiple people whom each had a small part of their work statement consumed with supply chain security; however, their larger job responsibilities were focused elsewhere. In the realm of acquisitions and work consolidations, a best practice is coring up the governance and operational processes and leveraging the subsidiary team members for their product and process knowledge as well as a means to access their network of business partners (e.g. procurement, trade controls, logistics, suppliers, etc.).
As with any integration effort, there are best practices to be found from all parties and truly successful organizations make every effort to capture and replicate those best practices throughout their programs. The creation of a multi-faceted program health assessment enables all parties to identify where the strengths and weaknesses are on all aspects of the entity’s oversight of the supply chain security program.
The program health assessment should cover three critical areas:
- Program Infrastructure: A review of critical business operations such as organizational hierarchy, operating models and rhythm, business partner management and engagement as well as looking at what operational tools are in place to facilitate the supply chain security program.
- Supply Chain Data: A review to identify how supply chains are analyzed using available trade data and what Key Performance Indicators (KPIs) are measured. This is often the first deep look at a subsidiary’s supply chain infrastructure where discovery of common suppliers and logistics partners are identified.
- Risk Assessment Process: A review of the subsidiary’s risk assessment process identifies how the entity executes supply chain mapping, threat and vulnerability assessments and what control measures are in place to enforce security throughout the supply chain.
The outcome of a program health assessment will yield a maturity score which identifies where best practices, tools and systems are in place and where more robust processes and governance is needed.
Large scale efficiencies can be gained by utilizing standard processes, tools and systems, but determining which should be used can be a difficult task to navigate when considering multiple programs, businesses and differing requirements. When trying to encapsulate multiple programs, creating a baseline of the most stringent requirements from all programs enables each subsidiary to not only meet its minimum requirements, but also exceed them. Establishing this minimum acceptable performance level often brings a lot of clarity to the systems and tools that most effectively cross over the majority of the programs and subsidiaries.
The ongoing success of subsidiary integration is rooted in the ability for supply chain security leaders to stay engaged with all parties. Many certificated supply chain security programs require annual self-assessments and attestations. These duties create a great opportunity for teams to engage with one another to learn about changes and improvements made to the security posture of the supply chain. However, an annual tag-up is not enough to truly ensure that all business partners are committed to securing the supply chain. Recurring tag-ups are necessary to review trends in supply chain movements, threat assessments and to collaboratively execute a comprehensive risk assessment process and some of the leading principles of engagement is executive buy in.
Roadblocks do exist when trying to manage international programs from afar where regulations require local corporate officers to be the face of the program. In these cases, the recurring engagement with the subsidiary focal is even more important to ensure there is alignment on the program architecture and processes at the governance level so that the local officer can accurately describe those to the regulator.
It takes a lot of effort to stand up the initial integration of a subsidiary, but the benefits from leveraging one integrated network extend beyond standardization and resource consolidation. When a single organization is responsible for executing the processes and consolidating the data, the visibility a company gets to its extended supply chain and the security thereof creates an opportunity to drive a deeper level of business resiliency. Through the execution of a risk assessment process, supply chain partners are targeted for security assessments. When coupling all of the supply chain data between subsidiaries and the main corporation, a Supply Chain Security (SCS) program can identify common supply chain partners where the execution of a single security assessment yields value for multiple entities.
In this Venn diagram, you can see how conducting an assessment of the suppliers in the center enables each corporate entity to not only meet its vulnerability assessment commitments, but the efforts also provide valuable multi-tier security intelligence. It’s obvious that when corporations acquire companies who were formerly a Tier 1 supplier, they immediately get visibility into their Tier 2 supply chains. What many corporations then discover is their newly acquired visibility into the integrated network of Tier 3 and Tier 4 supply chain partners like packagers, logistics providers, security operations and security system providers.
Shoring up processes, tools and systems is a part of any acquisition, but an effective strategy for driving efficiencies into a supply chain security program isn’t to take a top-down governance approach, but instead to collaborate with the stakeholders in order to have frequent, candid and honest dialogue between the parties. Efficiencies are gained by operating under a single program infrastructure, executing risk assessment processes on common supply chain partners and gaining visibility into lower level supply chain tiers.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






