Thermal imaging provides security officers with investigation tools

The use of thermal imaging cameras (TICs) in assault cases is a relatively new concept for first responding officers and investigators. Thermal imaging is the simplified name for Infrared Thermography, which shows variations in heat sources. The technology has been used by doctors, engineers, and fire departments for decades. It is still relatively new and under-utilized by security personnel and investigators responding to assaults.
The Thermal Imaging Camera (TIC) is a valuable tool for investigators and first responding security officers when investigating assault cases. As all experienced investigators and security officers know, bruising from assaults may not show up at all or may only show up , preserve, days after the offense has been committed. As a responding security officer, your job, after securing the assailant, is to document evidence of the assault for use later by the prosecutor. This evidence is critical to obtain and deliver to the county or district attorney who will be prosecuting the assailant. Oral testimony and written reports are great, but, as a former Assistant District Attorney, I can tell you that photographic evidence and video evidence make cases and establish that proof “beyond a reasonable doubt.” Many times, though, we are faced with assaults where the perpetrator has not broken the victim’s skin, there is no bleeding or visible evidence of an assault. In cases like this, we can rely on proof of subcutaneous bruising (hemorrhage) to show the force that was used in the assault. Most bruising will not show up for days on the victim’s chest, arms, neck, or face.
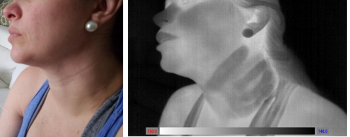
The photograph of the victim on the left shows an assault victim who appears to have no bruising around her neck. The image on the right is a thermal (heat) image of the same victim’s neck. In the thermal image we can clearly see the heat profile of fingers wrapped around the victim’s throat (photos provided courtesy of Officer Brian Bennett with his express permission).
Though some of TICs are sold for use in construction, engineering, HVAC, and firefighting, they still can be utilized for criminal investigations. Even inexpensive TICs produce very nice thermal images.
Having served as a police chief and a supervisor of security, I am keenly aware of the budget issues that private and governmental agencies face. Some security departments and police agencies simply cannot afford to spend a thousand dollars on a Thermal Imaging Camera (TIC). In my service as a volunteer firefighter, I have observed that almost every fire department carries a Thermal Imaging Camera (TIC) on their Engine. Even small rural fire departments usually have a TIC in their engine to help locate “hot spots” between walls or in attic spaces.
Security personnel, whose agency does not own a TIC, may want to reach out to their Maintenance Department or Safety Team and ascertain if they have a TIC. If so, officers should borrow the TIC to see if there are thermal images proving injury to the victim, by way of heat signatures, such as finger marks or grab marks on your victim’s body. You can document that image by simply taking a picture of that image with your smart phone. These images have been accepted in courtrooms across the country as proof of bodily injury – a required element in Assault Bodily Injury cases.
I urge you to begin utilizing a Thermal Imaging Camera (TIC) in all assault investigations. There is an extremely high likelihood that a perpetrator who strikes, grabs, kicks, or strangles his victim will leave signature thermal image evidence of the assault on his victim. Your photographs of these thermal images of victims’ soft-tissue injuries could be the deciding factor in obtaining a conviction against an assailant. When you have a case with no visible signs of trauma, think about utilizing a TIC to ascertain if there subcutaneous injury to the cells and tissues of your victim by using a thermal imagining camera.
Additionally, a TIC is a useful security tool for helping locate suspects or lost children (or adults) in outdoor natural areas such as fields or forests. TICs can be used by security, fire protection, and maintenance personnel to help locate fires between walls, on roofs or electrical “hot spots” in industrial machinery. TICs are a multi-function tool that can be utilized by all departments in the private sector.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






