Security without borders: Protecting cloud apps
Cybersecurity survey highlights global challenges and opportunities

Even before the worldwide COVID-19 pandemic and subsequent reshaping of the global workforce, public cloud has been strongly driving digital and business innovation. In addition to unleashing a host of business benefits, rapid cloud adoption was already creating new challenges and risks, including security concerns about collaboration and workflows, prior to the massive shift to remote work and online computing brought about by the “new normal.”
To take a closer look at public cloud, adoption trends, security concerns, app vulnerabilities, and a variety of related issues, Barracuda commissioned independent market researcher Vanson Bourne to conduct a global survey of 750 IT decision makers responsible for their organization’s cloud infrastructure. The survey, fielded in February 2020, included participants from the U.S., EMEA and APAC, representing organizations of all sizes from a broad range of industries.
While applications are a key part of many cloud deployments, rapid adoption of the cloud and the ongoing evolution of apps both create new risks. Careful attention must be given to secure the growing application threat vector. New strategies and solutions, including Web Application Firewalls specifically designed to protect apps from advanced threats, are required to help mitigate these risks.
Cyberattacks and their associated costs are on the rise
Around the world, cyberattacks are increasing. Since 2017, cyberattacks in all global regions have gone up about 20%. In fact, three-quarters of respondents said they have already been the target of a cyberattack, highlighting a serious global security challenge. The United States and APAC reported slightly higher rates of attacks than EMEA.
It’s costing organizations a significant amount of time to prevent and manage cyberattacks. More than one-quarter spend one day or more of the work week on cybersecurity issues—time and money that limits the impact and benefit IT teams can provide when it comes to business enablement and other proactive initiatives. More time is spent dealing with cyberattacks in APAC and less is spent in EMEA than in the United States. Much of this work could be offloaded to advanced security solutions that use artificial intelligence and machine learning to automate security tasks, allowing IT to add more value and spend time elsewhere.
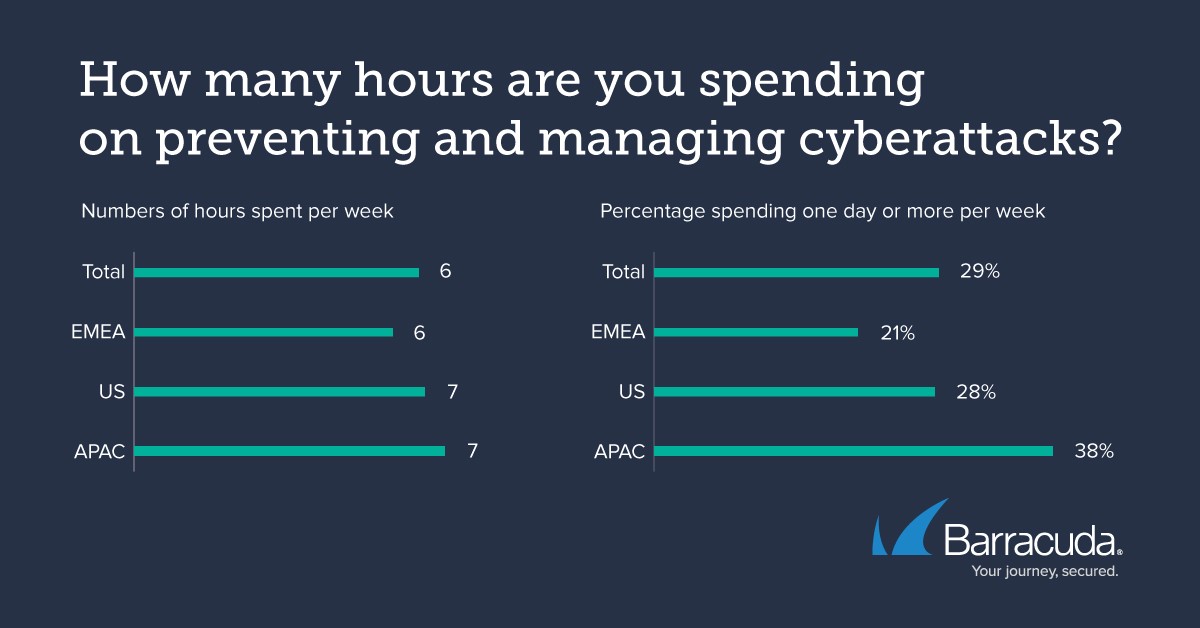
Image courtesy of Barracuda Networks
There’s confidence in the cloud, but not all organizations feel fully protected
A majority of businesses have added additional security measures to their public cloud deployments, but the adoption of third-party solutions has slowed over the past few years. This year, just slightly more than half of respondents said they have added more security to protect their cloud workloads. In 2017, that number was 62%. This decrease may indicate increased confidence for built-in security. Those in APAC and the U.S. are more likely to have added security solutions than those in EMEA.
For organizations that haven’t already done so, there are strong intentions in all global regions to implement added cloud security. The number of companies that plan to add additional security in the future is nearly equal across all regions. However, in EMEA, more than 10% said they have no plans to implement any additional security.
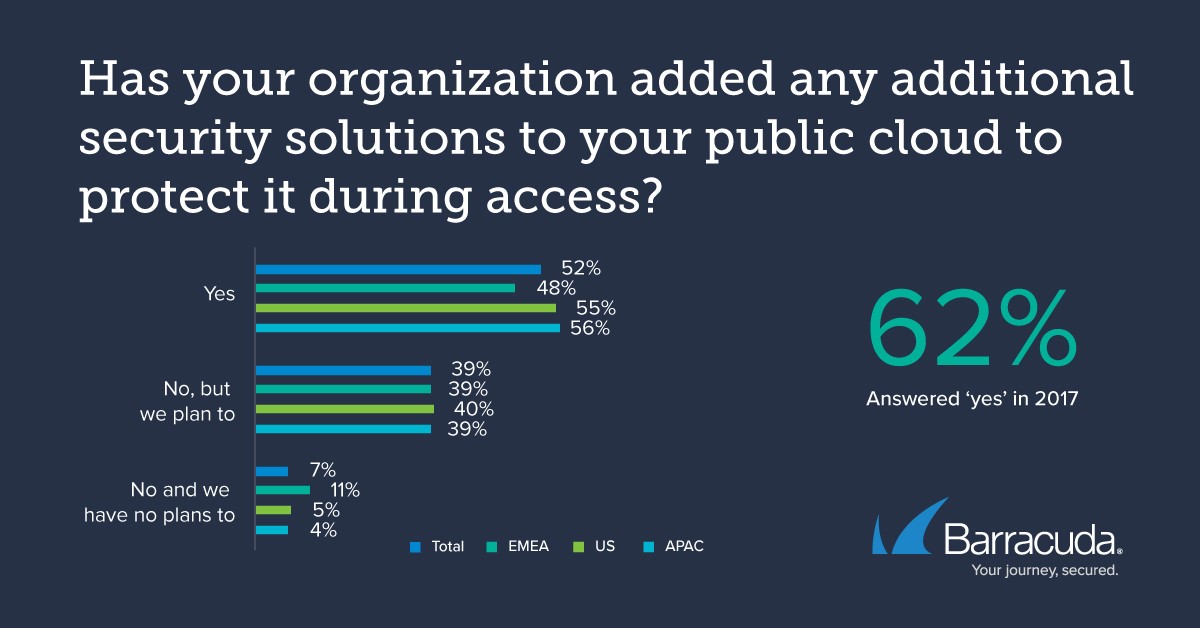 Image courtesy of Barracuda Networks
Image courtesy of Barracuda Networks
Nearly 67% of organizations believe they are fully protected in the cloud, with U.S. being the most confident. A third, however, don’t feel completely protected and that will ultimately prompt organizations to seek additional security strategies and solutions to close the gaps.

Image courtesy of Barracuda Networks
Concerns about poor app security and related consequences are prevalent
More than half of the IT decision makers said they are worried about losing sensitive, mission-critical data. In addition to concerns about data loss, crippled day-to-day operations, and lost customers, secondary consequences of a successful cyberattack can include lawsuits, regulatory fines, and damage to brand reputation.
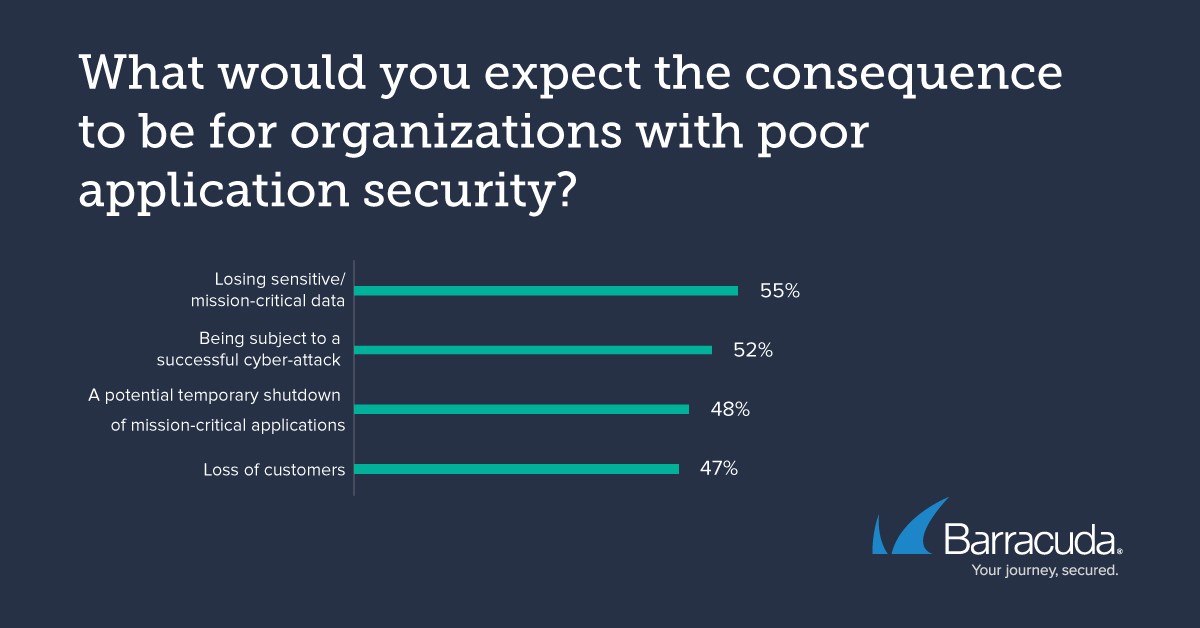
Image courtesy of Barracuda Networks
Most IT decision makers are concerned about app protection. They understand the need to protect apps that can be accessed by external users, involve e-commerce or PII, or can be accessed via mobile devices. A small majority even feel that applications without external access are still vulnerable, which shows the extent of the concern.
These concerns underscore the importance of providing customers with a strong and secure IT solution that provides reassurance about public cloud security to increase adoption and help them take advantage of all the business benefits inherent in leveraging the cloud.
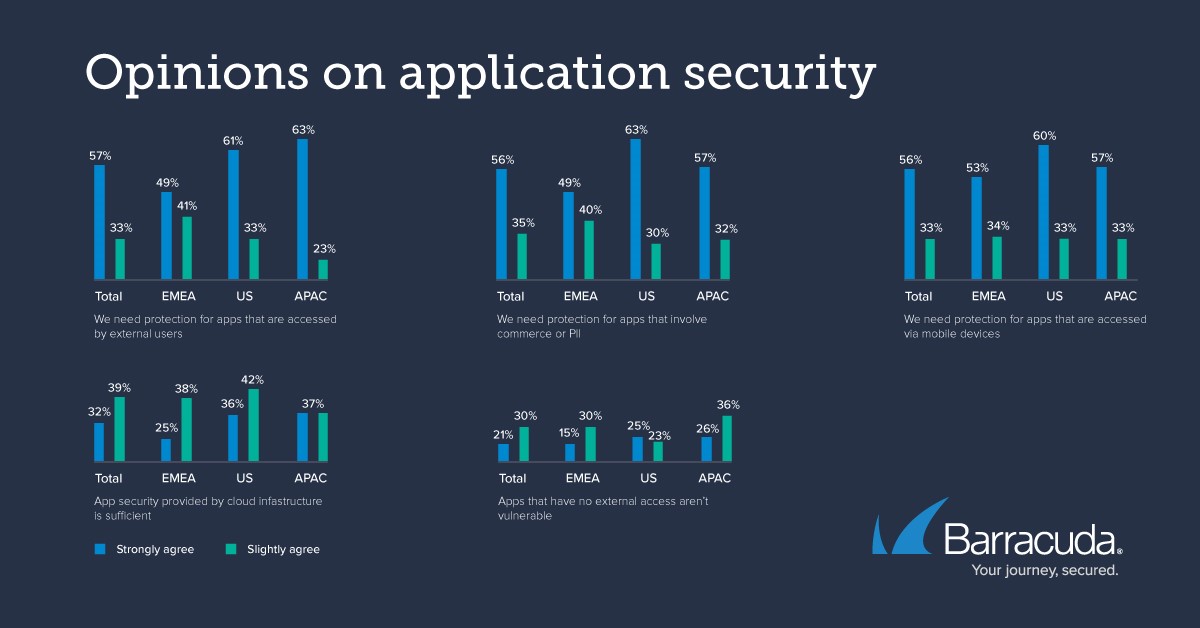
Image courtesy of Barracuda Networks
Use a third-party WAF solution to fully protect cloud applications
When it comes to application security, there’s no substitute for the benefits and protections of a web application firewall (WAF). WAFs are specifically designed to protect websites and applications from advanced threats.
When properly deployed in front of web-facing apps, a WAF ensures protection from web and distributed denial-of-service (DDoS) attacks, protects APIs and mobile apps, blocks malicious bots and automated attacks, secures application delivery, and controls access and authentication. Many Software-as-a-Service (SaaS) solutions also include built-in, WAF-related tools to help discover and remediate vulnerabilities before they lead to attacks.
As apps remain one of the most exploited threat vectors and security remains a top concern, WAFs provide the ability to safeguard data with confidence by eliminating application vulnerabilities and stopping data breaches.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






