GAO: Federal Agencies Need to Coordinate on Requirements and Assessments of States

Although the Centers for Medicare and Medicaid Services (CMS), Federal Bureau of Investigation (FBI), Internal Revenue Service (IRS), and Social Security Administration (SSA) each established requirements to secure data that states receive, these requirements often had conflicting parameters, says the U.S. Government Accountability Office (GAO) in a new report.
According to GAO, such parameters involve agencies defining specific values like the number of consecutive unsuccessful logon attempts prior to locking out the user. Among the four federal agencies, the percentage of total requirements with conflicting parameters ranged from 49 percent to 79 percent, GAO found.
Regarding variance with National Institute of Standards and Technology guidance, GAO found that the extent to which the four agencies did not fully address guidance varied from 9 percent to 53 percent of total requirements. The variances were due in part to the federal agencies' insufficient coordination in establishing requirements, says GAO.
Although the Office of Management and Budget's (OMB) Circular A-130 requires agencies to coordinate, OMB has not ensured that agencies have done so. Further, while federal agencies' variance among requirements may be justified in some cases because of particular agency mission needs, the resulting impact on states is significant, according to state chief information security officers (see figure).
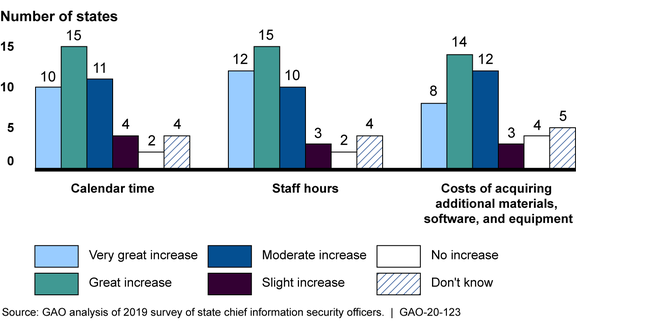
The four federal agencies that GAO reviewed either fully or partially had policies for coordinating assessments with states, but none of them had policies for coordinating assessments with each other. State chief information security officers that GAO surveyed reinforced the need to coordinate assessments by identifying impacts on state agencies' costs, including multiple federal agencies that requested the same documentation.
Coordinating with state and federal agencies when assessing state agencies' cybersecurity may help to minimize states' cost and time impacts and reduce associated federal costs, notes the report. Federal agencies reported spending about $45 million for fiscal years 2016 through 2018 on assessments of state agencies' cybersecurity, says GAO.
Recommendations for Executive Action
-
Recommendation: The Director of OMB should ensure that CMS, FBI, IRS, and SSA are collaborating on their cybersecurity requirements pertaining to state agencies to the greatest extent possible and direct further coordination where needed.
Agency Affected: Executive Office of the President: Office of Management and Budget
-
Recommendation: The Director of OMB should take steps to ensure that CMS, FBI, IRS, and SSA coordinate, where feasible, on assessments of state agencies' cybersecurity, which may include steps such as leveraging other agencies' security assessments or conducting assessments jointly.
Agency Affected: Executive Office of the President: Office of Management and Budget
-
Recommendation: The Administrator of CMS should, in collaboration with OMB, solicit input from FBI, IRS, SSA, and state agency stakeholders on revisions to its security policy to ensure that cybersecurity requirements for state agencies are consistent with other federal agencies and NIST guidance to the greatest extent possible and document CMS's rationale for maintaining any requirements variances.
Agency Affected: Department of Health and Human Services: Centers for Medicare and Medicaid Services
-
Recommendation: The Administrator of CMS should revise its assessment policies to maximize coordination with other federal agencies to the greatest extent practicable.
Agency Affected: Department of Health and Human Services: Centers for Medicare and Medicaid Services
-
Recommendation: The FBI Director should, in collaboration with OMB, solicit input from CMS, IRS, SSA, and state agency stakeholders on revisions to its security policy to ensure that cybersecurity requirements for state agencies are consistent with other federal agencies and NIST guidance to the greatest extent possible.
Agency Affected: Department of Justice: Federal Bureau of Investigation
-
Recommendation: The FBI Director should fully develop policies for coordinating with state agencies on the use of prior findings from relevant cybersecurity assessments conducted by other organizations.
Agency Affected: Department of Justice: Federal Bureau of Investigation
-
Recommendation: The FBI Director should revise its assessment policies to maximize coordination with other federal agencies to the greatest extent practicable.
Agency Affected: Department of Justice: Federal Bureau of Investigation
-
Recommendation: The IRS Commissioner should, in collaboration with OMB, solicit input from CMS, FBI, SSA, and state agency stakeholders on revisions to its security policy to ensure that cybersecurity requirements for state agencies are consistent with other federal agencies and NIST guidance to the greatest extent possible.
Agency Affected: Department of the Treasury: Internal Revenue Service
-
Recommendation: The IRS Commissioner should revise its assessment policies to maximize coordination with other federal agencies to the greatest extent practicable.
Agency Affected: Department of the Treasury: Internal Revenue Service
-
Recommendation: The Commissioner of SSA should, in collaboration with OMB, solicit input from CMS, FBI, IRS, and state agency stakeholders on revisions to its security policy to ensure that cybersecurity requirements for state agencies are consistent with other federal agencies and NIST guidance to the greatest extent possible and document the SSA's rationale for maintaining any requirements variances.
Agency Affected: Social Security Administration
-
Recommendation: The Commissioner of SSA should fully develop policies for coordinating with state agencies on the use of prior findings from relevant cybersecurity assessments conducted by other organizations.
Agency Affected: Social Security Administration
-
Recommendation: The Commissioner of SSA should revise its assessment policies to maximize coordination with other federal agencies to the greatest extent practicable.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






