15% of Small Businesses Experienced a Cybersecurity Threat in 2019
More than 1 in 10 small businesses faced a virus, hack, or data breach in 2019, revealing small businesses' cybersecurity vulnerability. Luckily, the majority of small businesses (67%) say they will devote more resources to cybersecurity in 2020.
Nearly one-fifth of small businesses (15 percent) say they experienced either a hack (seven percent), virus (five percent), or data breach (three percent) in 2019, according to new data from The Manifest, a B2B news and how-to site.
The Manifest surveyed 383 small business owners and managers to better understand the challenges they had with cybersecurity in 2019 and how they plan to approach cybersecurity in the future. "It begins with small businesses believing — erroneously — that it cannot happen to them. Although a hacker might not single out a small business, businesses can certainly become victims of hacks and other cyber-criminality," said Charles Lee Mudd Jr., founder and principal of Mudd Law Firm, a firm specializing in internet, startup, intellectual property, privacy, defamation, space, and entertainment law.
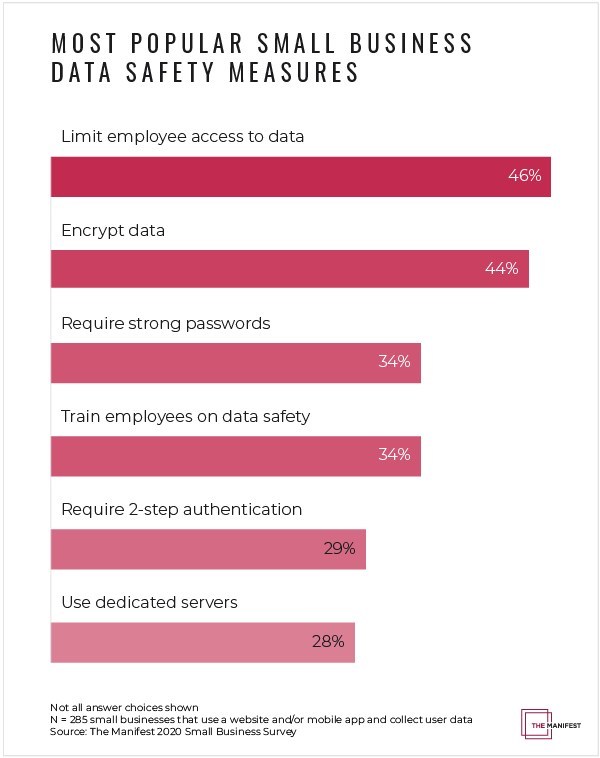
Limiting Access, Encryption Are Most Popular Small Business Cybersecurity Strategies
The most popular strategies small businesses pursue for cybersecurity are limiting employee access to data (46 percent) and encrypting data (44 percent), followed by requiring strong passwords (34 percent) and training employees on data safety (34 percent).
"The top cybersecurity threat to small businesses is an insider threat because employees let cybercriminals in," said Cyrus Walker, principal at Data Defenders, a cybersecurity services provider.
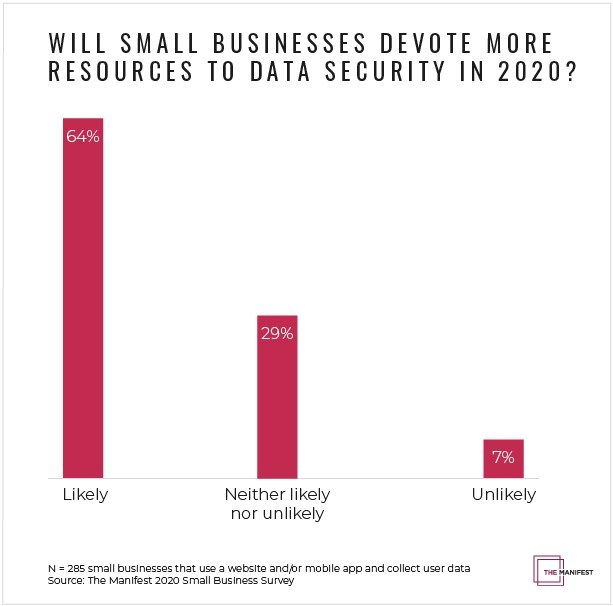
Majority of Small Businesses Want to Increase Cybersecurity Resources
The Manifest found that, at the time of data collection in December 2019, most small businesses (64 percent) said they were planning to devote more resources to cybersecurity in 2020. However, the sudden economic downturn caused by the COVID-19 pandemic may mean small businesses can't follow through with cybersecurity improvement plans, though, just as cybersecurity becomes more important than ever due to many businesses moving online and employees working remotely, says the report.
Read the full report: https://themanifest.com/mobile-apps/data-safety-small-businesses-2020-cybersecurity-statistics
*All images courtesy of The Manifest.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





