The Next Generation Risk, Resilience and Security Provider

I believe we are at an inflection point in our industry. The transactions of value within our ecosystem of consultants, integrators, product vendors and security executives must evolve to meet the new business and risk reality. According to many studies, security executives have very little time for aggregating knowledge around the local and global risk picture. As well, they have the same challenge with staying current with best practices and standards in their profession. Finally, like their business counterparts, they must leverage subject matter experts to help research and assess new technology that may impact their strategy and their practices. And they must do all of this with pressures on their budget, their value and their resources.
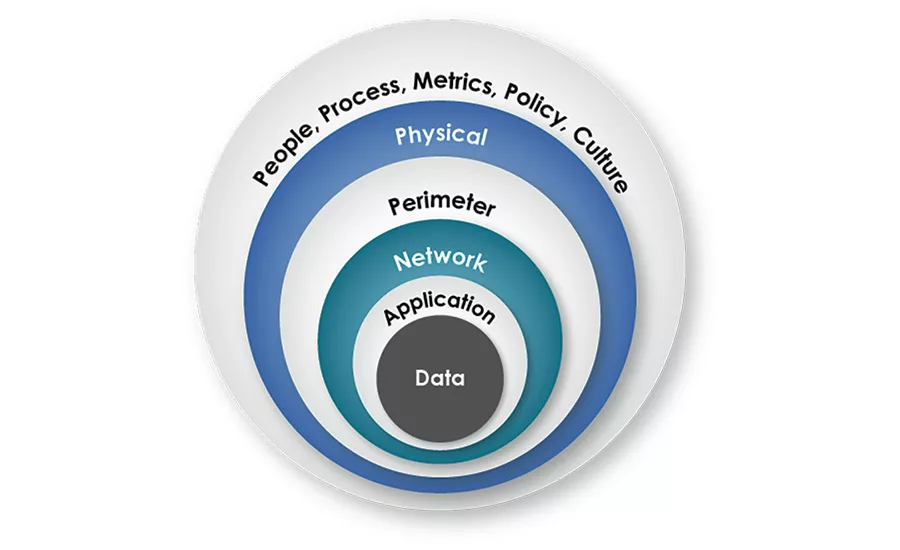
Standards are evolving as well. For example, one standard, Organizational Resilience Management (ORM) has been dependent on the experience, ability and collaboration of risk, resilience, and security professionals across multiple domains. At their best, they need to feed and understand the evolving risk picture, form a strategy to meet it, manage it, and mitigate it. To do this, they also provide their unique perspectives such as business continuity, emergency management, physical and logical security. However, they are challenged in evolving to a 360-degree picture and standard operating environment across all the domains because of the difficulty in how to introduce change across key management disciplines. Peter Drucker, the respected corporate strategist and author noted that culture can derail the best strategy.
There is a reason for this. Change is difficult for most organizations, especially when confronted with new strategies that disrupt or evolve old behaviors. We are learning, as an industry ecosystem, that we must get the strategy and measures right before the implementation of technology. Now we are also saying, we must get the cultural change process right as well.
How do you create a high performance culture, adaptable to change and innovation, while creating and leveraging a comprehensive all-hazards risk mitigation program that redefines how the risk ecosystem behaves?
We are finding that security executives are longing for a fresh perspective on how to organize and optimize their people who are performing roles in core processes using technology or tools. First, a baseline understanding of their current measures of performance are needed, before a strategy and plan can be developed. As well, consideration of the organizations culture is paramount.
Unifying Business and Security Drivers
Security executives can take a page from business executives and move to understand how their organizations investment into security is inextricably tied to their business drivers and their core processes. They must know their current program performance baseline which will include measures of risk defined by them and their internal stakeholders as well as the efficiencies of their people delivering core processes through technology.
If done with a proper methodology, organizational resilience truly becomes the capacity to be adaptive in a complex and changing environment.
To do this well will require a collaborative effort between many management disciplines which are usually silos within an organization. Silos can be accepted but the measures and feedback from security executives are clear: the more you can integrate the silos the more time, money and resources you will save and the more secure you will be.
There is a category of services that are emerging that will help navigate this journey. We call this new segment “Security Risk Management Services” or SRMS An SRMS provider can operate in one of the consulting, services, or technology areas. What differentiates them is their knowledge of their role and competency in helping unify the language, processes and information management architecture of Enterprise Security Risk Management (ESRM).
Ultimately, organizations will need to find, assess, contract and manage the external domains of knowledge and resources within the SRMS category if they truly want to create ESRM. Few organizations have the resources and skills needed to do this. New organizational competencies are required. The DNA must evolve to muster the will, strategy and operational discipline to engage the ecosystem.
My organization is experiencing this. And it is not easy. However, the need and demand to orchestrate the emerging SRMS vendor community and the internal stakeholders against the emerging needs of our clients demanded we take action.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!








