Smartphones Can Open Doors, Dorm Doors That Is
|
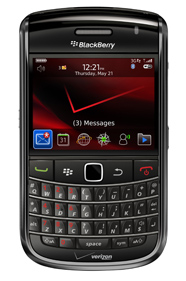
| College students see value in using their smartphones to gain access to facilities and services. There is a pilot program at Arizona State University. Near field communication chips in the BlackBerry Bold, for example, can integrate to door locks. Photo courtesy PRNewsFoto/Verizon Wireless |
Thanks, in part, to near field communication (NFC) chips embedded in smartphones, the door has opened for college students and staff to unlock and lock their campus doors using personal smartphones.
For example, HID Global launched a pilot project last fall that showcases the benefits of using NFC smartphones for opening doors at universities and other campus environments. The trial is underway at Arizona State University (ASU), where a group of students and staff are accessing a campus residence hall and selected resident’s rooms using iCLASS SE credentials embedded into a variety of popular smartphones connected to all major mobile networks.
ASU manages on-campus housing for approximately 13,000 students living in 34 residence halls. To implement the pilot, readers were deployed on secured doors to ASU’s Palo Verde Main hall. Participants were given NFC smartphones carrying next-generation iCLASS SE technology. To open door locks, participants present the phones to a door reader just as they do with their existing Sun Cards, which are the university’s campus credentials. All participants are using their phones for residence hall access, and some are using them with a unique additional digital key and PIN to open individual room doors. The technology also supports over-the-air provisioning and management of digital keys, which simplifies administration of the access control system.
In initial feedback, approximately 80 percent of ASU participants reported that using a smartphone to unlock a door is just as convenient as using their campus ID card. Nearly 90 percent said they would like to use their smartphone to open all doors on campus. While the pilot was focused on physical access, nearly all participants also expressed an interest in using their smartphone for other campus applications including access to the student recreation center, as well as transit fare payment and meal, ticket and merchandise purchases.
“When I first saw this technology used in other applications, I recognized the benefits it could bring to a university campus,” said Laura Ploughe, director of business applications and fiscal control, University Business Services, at Arizona State University. “Mobile phones are at the heart of campus life and [they] play a major role in facilitating the students’ social connections. This project has proven that a ubiquitous device can converge secure identity credentials and physical access control, and endorsed the promise that NFC technology holds within the campus environment. We were very impressed with the convenience of putting Sun Card credentials on NFC smartphones, as well as the enhanced security that is delivered by this next-generation of advanced access control system.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!



