Product spotlight: GSX 2024 product preview

GSX — held this year from September 23 through September 25 in Orlando, Florida — provides security leaders an opportunity to network and discuss current security trends. Security magazine highlights some of the products featured at this year’s conference.
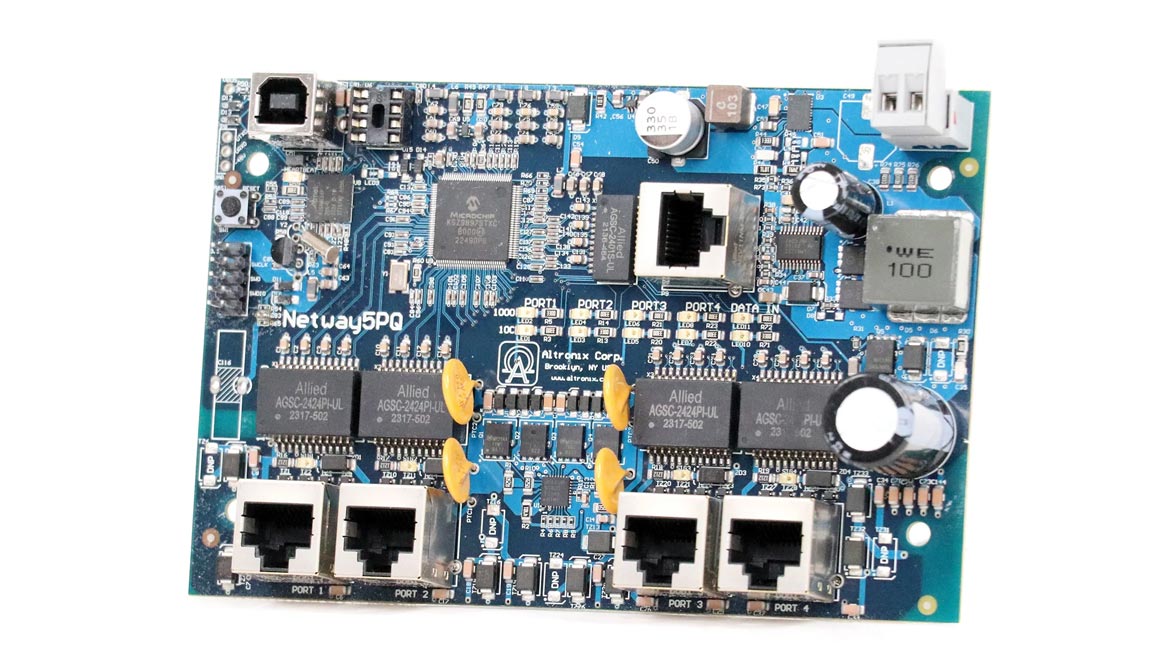
Altronix
Improve Access Control Deployments
The NetWay5PQ from Altronix is a 5-port Managed hardened PoE+ switch designed to enhance the efficiency of access control deployments. This compact switch board powers up to four IP devices such as access controllers and cameras via a single Ethernet cable. In addition to providing four PoE/PoE+ output ports and an Ethernet/data port, the NetWay5PQ also features embedded LINQ Technology for remote monitoring, control, and reporting of power diagnostics. This includes capabilities to reset devices, receive alerts/notifications and log event history, making it suitable for installations where space is limited and remote management is required. Image courtesy of Altronix
Find out more at altronix.com

Babel Street
Monitor Risks Using Analytics
Babel Street Insights delivers advanced AI and data analytics solutions that enable users to search, aggregate, and integrate open-source intelligence (OSINT) data — including publicly and commercially available information (PAI/CAI) — to close the Risk-Confidence Gap. With the 2024 release of Elite Regional Access, Babel Street now empowers users to zoom in on communities, events, and trends that are often obscured or completely inaccessible within broader global data sets for deeper insights to help mitigate risks, optimize operations, and gain a competitive edge in rapidly evolving landscapes. Image courtesy of Babel Street
Find out more at babelstreet.com

Boon Edam
Secure Sensitive Data and Spaces
Boon Edam’s Circlelock “Solo” is a turnkey, mantrap portal solution that provides security for sensitive locations, such as data centers. Only one user can pass through the Circlelock due to the reliable near-infrared and optical detection technology of StereoVision. The Circlelock Solo supports multi/two-factor authentication, including a variety of biometric technologies, ensuring that both the credential and identity are confirmed. Image courtesy of Boon Edam
Find out more at boonedam.com/en-us

Corbin Russwin
Stregthen Locks for Enhanced Security
The Corbin Russwin ML2000 Series with Motorized Electric Latch Retraction (MELR) mortise locks are tailor-made for the demands of commercial, institutional, and industrial environments. Designed for dependable operation, code compliance and resistance to physical abuse, they offer seamless compatibility with any access control application using standard mortise locks. From in-swing to out-swing doors, they facilitate both push and pull operations and latch retraction capable of withstanding pressure up to 50lbs. Image courtesy of Corbin Russwin
Find out more at corbinrusswin.com/en

ECAMSECURE
Alert Users of Nearby Threats
ECAMSECURE's Digital Signage for Mobile Surveillance Units serves multiple purposes: a visual deterrent, a display broadcasting essential instructional messaging and even promoting businesses’ offerings. Whether it's alerting trespassers to vacate a restricted area or welcoming visitors to a parking lot, the unit reacts swiftly and effectively to the surrounding environment, ensuring both enhanced security and effective communication. Image courtesy of ECAMSECURE
Find out more at ecamsecure.garda.com

IDIS
Reduce False Camera Alarms
The new IDIS Edge AI camera range reduces false alarms and improves the responsiveness and operational efficiency of security teams with faster forensic search and investigation. Plug-and-play and NDAA compliant, the cameras are equipped with the IDIS Deep Learning Engine on the edge. Image courtesy of IDIS
Find out more at idisglobal.com

ONTIC
Manage Security Operation Centers
Ontic’s Converged Security Operations Console is a centralized technology solution for teams across corporate security functions to establish a common view of situational awareness for unified management. Global Security Operations Centers (GSOCs) get a complete view of signals from OSINT activity, weather analysis, public events, geo-risk devices, systems, and stored data for always-on threat visualization and monitoring with coordinated workflows for actionable risk intelligence and incident response. The solution allows teams to analyze data in relation to public records, people and assets, incidents, and more to activate playbooks, enable their guard force, and use mass notification when necessary. Image courtesy of Ontic
Find out more at ontic.co
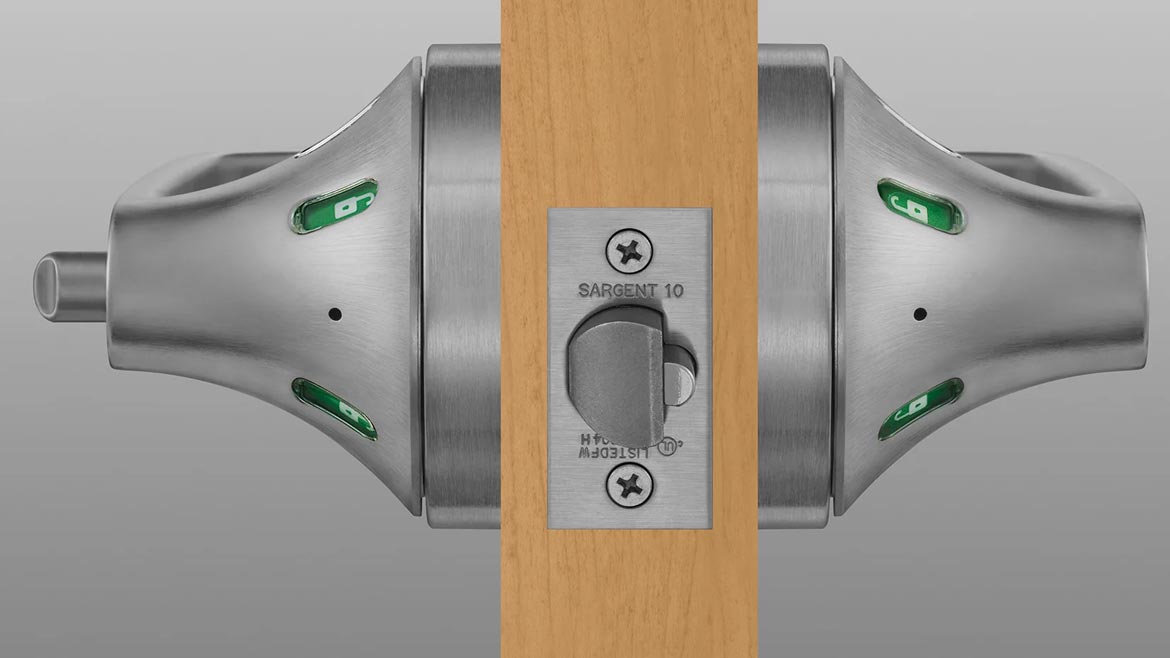
SARGENT
Ensure Doors are Locked
SARGENT announces the 10X Line bored locks now with visual status indicators. These indicators offer confirmation of a door's locked/unlocked status. Available in multiple functions, including keyed and privacy, these locks are built for new and retrofit projects, exceed industry standards for ANSI/BHMA Grade 1 durability, and fit standard bored lock prep. Image courtesy of SARGENT
Find out more at sargentlock.com/en
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






