Home » Publications » Security Magazine
Security Magazine
2022 July
Cover Story
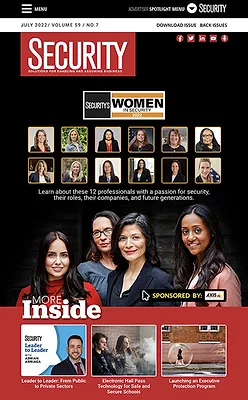
Back to TopSpecial Report / Women in Security 2022
These professionals represent the depth, breadth and diversity that make up women across all functions, roles and responsibilities within the security industry.
Read More
Featured Articles
Back to TopProduct Spotlight
Product spotlight on threat monitoring and risk assessment solutions
July 15, 2022
Integrated Solutions
Electronic hall passes: A powerful school safety technology
Electronic hall passes can play an integral role in combatting the K-12 student vaping epidemic, and the technology offers other safety and security benefits as well.
July 13, 2022
Enterprise Services
The ins and outs of launching an executive protection program
Security executives share practical considerations and tips for launching an executive protection function or reevaluating an existing program.
July 11, 2022
Columns
Back to TopLeadership and Management
Holding up a black mirror to society
It’s imperative security leaders constantly prepare their organizations for future threats. Conveniently, many of these potential threats are explored in one TV show.
July 8, 2022
Education & Training
Risk assessment strategies: Be careful what you eat
Conducting risk assessments are a valuable piece of any security program. But, in order to achieve maximum return, there’s a right and a wrong way to follow through.
July 8, 2022
Cyber Tactics
Costa Rica in crisis: Russian ransomware raises its head
Let’s take a look at the evolution and path of Conti ransomware.
July 8, 2022
Career Intelligence
International experience can advance your security career
Effectively leading and navigating security programs in diverse cultural settings is critical to many security leaders’ successes. Here’s how to get that experience.
July 8, 2022
Leader to Leader
Transitioning from public to private sector security
Burke Brownfeld sits down with corporate security leader Adrian Arriaga to talk about the corporate security function inside a healthcare environment.
July 6, 2022
Security Talk
Future-proofing your organization against the unknown
Businesses need to evaluate how they manage their physical risks to avoid the next improbable event that could have devastating consequences to an organization’s continuity and bottom line.
July 6, 2022
Departments
Back to TopGlobal News
Bolstering crisis response practices during geopolitical cyber threats
July 18, 2022
Global News
Executive support highly correlates with security operations success
July 18, 2022
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing





















