Home » Publications » Security Magazine
Security Magazine
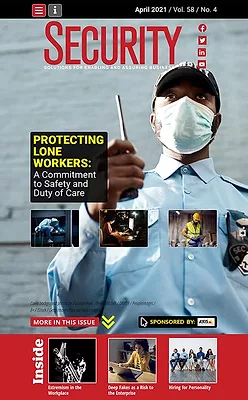
2021 April
Cover Story
Back to TopOrganizations in charge of protecting lone workers must fulfill their duty of care, taking all steps reasonably possible to ensure their safety.
Read More
Featured Articles
Back to TopHiring for personality
When it comes to completing your security team, hiring the right employees will lead you, your team and your organization to greater success, but finding, recruiting and retaining top security talent may be easier said than done.
April 9, 2021
Risk Management
Don’t discount the risk of deepfakes to the enterprise
Many security researchers are now predicting that deepfakes could become a major security threat in the 2021-2022 period. Where is the threat and what can you do about it?
April 14, 2021
Case Study: Integrated Solutions
The Gaylord Opryland Resort boosts security
April 12, 2021
Columns
Back to TopCyber Tactics
Mission-critical supply chain software: A growing operational priority
April 1, 2021
Career Intelligence
Positive brand reputation will advance your security career
Have you considered what you can do to help build a positive brand reputation for yourself and your organization?
April 1, 2021
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media.
Design, CMS, Hosting & Web Development :: ePublishing

















