Home » Publications » Security Magazine
Security Magazine
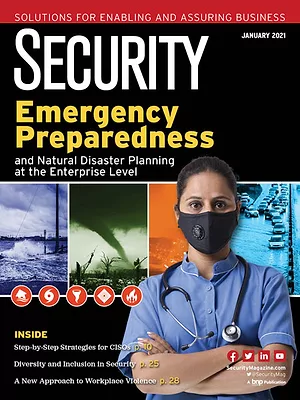
2021 January
Cover Story
Back to TopEnsure your organization is prepared for the next disaster, not the same disaster, with these six tips.
Read More
Featured Articles
Back to TopRecognize. Respond. Survive. A new approach to workplace violence prevention
Take a proactive approach to preventing violence.
January 11, 2021
Creating a diverse and inclusive workplace within security
Foster an environment of diversity and inclusion for better performance and agility within your department and enterprise-wide.
January 7, 2021
The changing role of security
Hear from Security's Editorial Advisory Board members about their thoughts on the changing role of security in the enterprise.
January 6, 2021
Columns
Back to TopSign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing














