Security Top Stories
Enterprise Services
How automated security entrances and proactive maintenance deliver ROI, reduce costs and enhance protection for modern facilities.
Read More
Special Report
The 2025 Annual Guarding Report: Unrest Inspires Upgrades in Training, Technology
Security executives and guarding companies identify trends in security guarding throughout 2025, from political, executive protection challenges, violence, and theft.
December 1, 2025
Cyber Tactics
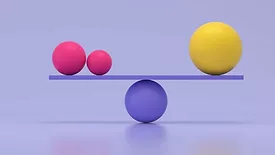
Navigating Cybersecurity’s Tightrope: Balancing Skills, AI, and Human Resilience
Addressing the skills gap, supporting employee well-being, responsibly leveraging AI, and securing adequate funding requires a holistic approach.
November 26, 2025
Product Spotlight on Healthcare
Security magazine highlights a few products that can help better secure healthcare facilities.
November 24, 2025
Integrated Solutions
5 Steps for Law Enforcement: Prepare for Hurricane Season with New Technology
Public safety professionals can prepare for hurricane season and protect their communities.
November 21, 2025
5 Minutes With
What AI Vulnerabilities Do Security Leaders Tend To Overlook?
November 20, 2025
Security Talk
Inside The 2025 Security Benchmark Report
Security leaders can gain insights into industry trends by comparing The Security Benchmark Report data year-over-year.
November 19, 2025
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing