Security Education & Training
Education & Training
Key learning objectives all de-escalation programs should emphasize.
Read More
Critical Thinking Erosion: A Hidden Threat to Security Career Resilience
While cybersecurity is vital, it is only one piece of the larger security puzzle.
February 16, 2026
What Background Checks Miss: The Human Layer Behind Modern Screening
How to ensure your background checks aren’t missing clear red flags.
January 22, 2026
Career Intelligence
Private Sector Intelligence Careers
As corporate intelligence roles grow, gaps in analytic tradecraft education highlight the need for structured thinking and decision-support training.
January 19, 2026
Leadership & Management
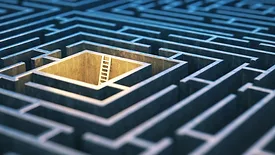
Escape Rooms, Mud Runs, and Game Nights: Cradles of Leadership?
What team-building games can teach us about real leadership.
January 16, 2026
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing