Home » enterprise security
Articles Tagged with ''enterprise security''
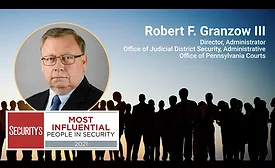
Director, Administrator, Office of Judicial District Security, Administrative Office of Pennsylvania Courts
Read More
Steven Antoine – Most Influential People in Security 2021
Vice President, Global Security, PepsiCo North America
September 1, 2021
Three elements of a successful GSOC
For a Global Security Operations Center (GSOC) to be successful in today’s threat landscape, it must include these three key elements in its design.
August 9, 2021
Leadership & Management
Nominate a deserving colleague: That’s what a leader does
August 2, 2021
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing