Home » international security
Articles Tagged with ''international security''
BeyondZero: How Jacobs is Fostering a Culture of Caring
Jacobs is taking duty of care further by integrating their BeyondZero philosophy into every facet of the business.
December 7, 2018
GDPR Implementation Costs Enterprises More than Expected
Only 29% of healthcare organizations report having a comprehensive security program in place.
December 1, 2018
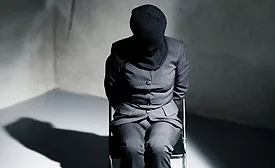
Our Executive is Missing: Kidnap and Ransom Basics for Security Professionals, Part 3
This is the third of a three-part series to help enterprise protective professionals understand how K&R can be successfully resolved.
November 14, 2018
Our Executive is Missing: Kidnap and Ransom Basics for Security Professionals, Part 2
The second of a three-part series to help protective professionals understand how K&R can be successfully resolved.
October 3, 2018
Sign-up to receive top management & result-driven techniques in the industry.
Join over 20,000+ industry leaders who receive our premium content.
SIGN UP TODAY!Copyright ©2026. All Rights Reserved BNP Media, Inc. and BNP Media II, LLC.
Design, CMS, Hosting & Web Development :: ePublishing