The connection between cybersecurity and worker safety
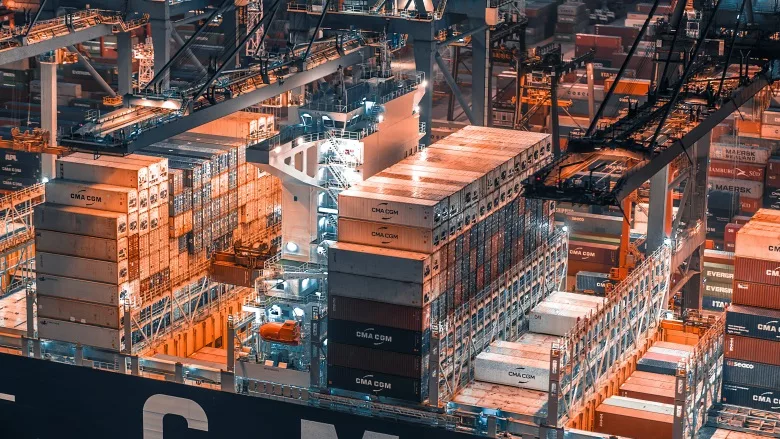
Image via Unsplash
Governments from the United States to Australia are shoring up their cybersecurity controls with a renewed focus on their technology assets, including operational technologies (OT). Preserving the integrity of these systems is a pillar of the U.S.’s national cybersecurity strategy and Australia’s national risk management program. These announcements capped a year of record-breaking threats, with 91% of organizations worldwide reporting at least one cyber incident in 2022, up from 88% in 2021. Cyberattacks on Ukraine’s critical systems throughout the Russia-Ukraine war demonstrate how exploitable vulnerabilities in OT and other systems can threaten both the digital and physical world. Cybersecurity should be a top priority for businesses across industries because, aside from providing improved resiliency in business operations, cybersecurity measures can improve an organization’s ability to protect the safety of employees and the end consumers of their products.
OT cybersecurity breaches are increasingly compromising the potential physical safety of workers. OT systems coupled with industrial internet of things (IIoT) devices being used within industrial networks to collect and exchange data are not always well protected. When increased network connectivity is introduced to enable business operation strategies, the lack of protection can lead to both loss of productivity and safety events as bad actors can more easily attack vulnerable systems that are used to control the physical processes.
Cyberattacks affecting these industrial environments can manifest through denial-of-service, phishing, watering-hole, or data injection attacks, to name a few. These attacks can often originate within an organization’s enterprise network before the attacker pivots into the industrial networks, exploiting the lack of segmentation that exists between the two.
Six years ago, private cybersecurity researchers identified “Energetic Bear” as a cyber operation targeting U.S. and European energy sector companies with malware, which was used to extract energy consumption information. This malware was similar to the Stuxnet virus that destroyed a fifth of Iran’s nuclear centrifuges by targeting their programmable logic controllers (PLCs) and speeding up the internal processes in such a way that the centrifuges tore themselves apart. Considering the physical effects of Stuxnet and similar attacks, hackers can potentially cripple energy systems, from wind turbines to gas pipelines to power plants. They do this by taking control of those systems that the processes depend on, such as PLCs.
During a 2018 attack on a global petrochemical company, the company’s safety instrumented systems (SIS), which are designed to take processes to a safe state when predetermined conditions are violated were compromised and attackers attempted to trigger a remote explosion. The attack failed because of a mistake in the attackers’ computer code that brought the production processes down before the attack could be fully carried out. Consider today’s disruption and safety implications: safety controllers are used at many critical infrastructure organizations, and it was a mistake by the attackers themselves that stopped the attack in 2017.
Given these risks, the mining and metals industry has made improvements in safety over the last two decades. With the increased use of artificial intelligence (AI) and other digitization initiatives, the need to continuously protect OT systems and their underlying networks becomes more important as the cost for adversaries to develop the attacks decreases and the cost to protect goes up.
Psychological safety is important for sustainable mining activities as people have the right to feel safe at work, and they perform at their highest level when they do. Companies can secure their systems and garner employee confidence in their ability to prevent cyberattacks by implementing a centralized security operations center (SOC) that has the ability to monitor the corporate and OT networks.
The benefits of a consistent cybersecurity posture stretch beyond worker safety and trust, to business results: cybersecurity measures can support business initiatives by increasing efficiency and improving resilience and agility.
The bottom line is that cyber-resilient organizations reap greater benefits, including safer work environments; better employee performance; improved job satisfaction; greater trust, efficiency, resilience and agility; improved brand reputation; and long-term sustainability. With the threat landscape ever evolving, cybersecurity investment is imperative.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!







