Stop ransomware with a deterministic approach to cybersecurity

There was an unprecedented increase in ransomware attacks in 2021. With each passing day, threat actors are getting more empowered as they gain even more financial success, giving them the funds to conduct larger-scale data breaches. Alarmingly, a large computer manufacturer, Acer, paid the highest ransom demand in history, shelling out $50M. Some other prominent victims of ransomware include Colonial Pipeline, Acer, JBS Foods, Axa, Kaseya and Deloitte.
What exactly do ransomware threat actors target?
In digging deeper into these attacks, it became evident that threat actors target critical workloads of enterprises of all sizes and then either cause business disruption or threaten to make confidential data public. In fact, ransomware threat actors leverage the services of another class of cybercriminals, known as initial access brokers, who specialize in breaching companies and then selling the access to ransomware attackers. These actors infiltrate organizations that have not patched their workloads, providing initial access brokers a way to infiltrate enterprise infrastructure.
Ransomware kill chain for server workloads
A ransomware attack on a critical workload follows the kill chain below.
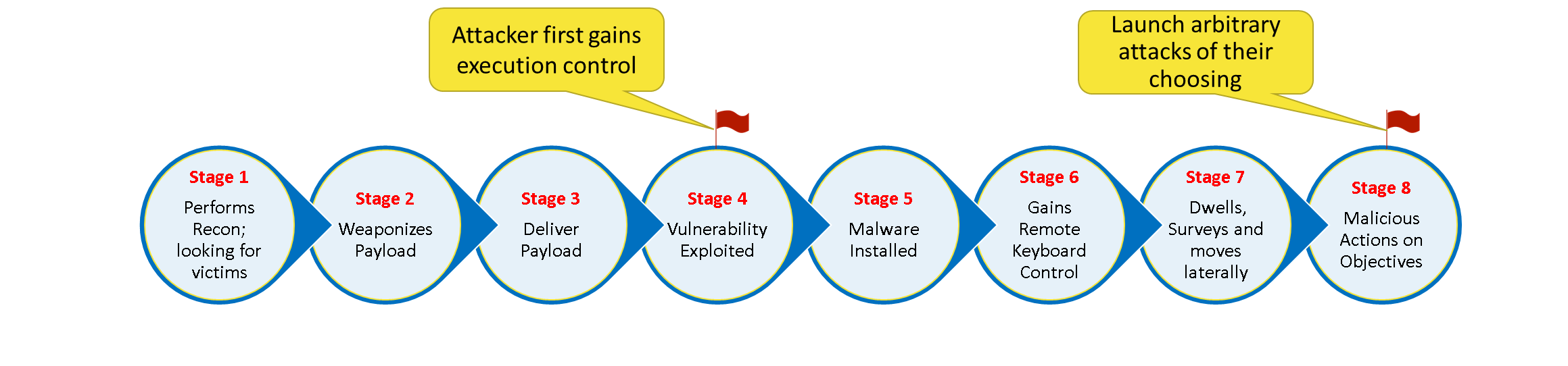 Image created by Satya Gupta, Virsec
Image created by Satya Gupta, Virsec In Stage 1, the attacker seeks out an unpatched vulnerable server using search engines that facilitate such activity.
In Stage 2, having identified a target, the attacker crafts a malicious payload that will achieve at least the following two objectives for the threat actor. The first objective packs data that will overrun the vulnerable application and allow the actor to gain execution privileges on the victim’s computer. The second goal packs the starter malware, which, upon subsequent execution, will establish a reverse channel and keyboard control back to the attacker's command control server access point.
In Stage 3, the attacker delivers the malicious payload described in Stage 2 to the victim’s workload.
In Stage 4, the targeted workload consumes the first part of the malicious payload, which helps the attacker gain execution control on the victim’s machine. Now the attacker can execute arbitrary code on the compromised device.
In Stage 5, upon gaining execution control, the attacker installs the starter malware from Stage 2.
In Stage 6, the starter malware establishes a reverse communication channel to the attacker's command control center. This path allows the attacker to communicate interactively with the target and perform several critical operations.
These operations, performed in Stage 7, include escalating or deescalating an attack, developing a unique en/decryption key for the victim, creating an inventory of high-value files, removing shadow and backup files, laterally moving to other reachable machines, dropping more malware, erasing logs and other maneuvers.
Finally, in Stage 8, the attacker launches one or more parts of their attack. Steps 7 and 8 can then repeat until the attacker meets all their objectives.
What is the root cause of ransomware attacks?
Studying the tactics used by the threat actors in 2020 and 2021, it became evident that the attacks are moving deeper into memory and targeting unpatched vulnerabilities that result in remote code execution (RCE) of arbitrary code on the victim workload.
In 2021 alone, there were over 28,000 unique vulnerabilities disclosed in various databases. Of these, 8,000 vulnerabilities had public exploits, 5,800 of which could be exploited remotely. An unprotected workload that is exposed to the internet can be exploited in under seven minutes. A workload that has not been patched and hosts server code that has one or more remote code execution vulnerability is the classic “unprotected” workload that threat actors are looking for.
If an enterprise does not patch software vulnerabilities in the first seven minutes after the vulnerability disclosure, they leave themselves vulnerable to a cyberattack. Many top ransomware victims in 2021 failed to patch their workloads for several years, let alone in seven minutes.
Why do conventional security solutions fail to detect ransomware promptly?
Conventional cybersecurity tools leverage either the pre- or post-execution technologies for protecting enterprise workloads. Pre-execution technologies include intrusion protection systems (IPS), next generation firewalls (NGFW) and web application firewalls (NGFW), among others. Post-execution technologies use variants of exploit detection and response (EDR) solutions.
Once the threat actor has infiltrated the workload using a remote code execution vulnerability, they can run sophisticated malware that can receive minimalistic or encrypted commands from the attacker’s remote command control center. This effectively bypasses all protection offered by pre-execution security solutions.
Post-execution security controls leverage user, network, file system and process creation activity logs as their triggers. Processing these triggers allows EDR technologies to detect attacks. However, a threat actor who can run arbitrary code on a victim’s workload can easily suppress any log. This effectively blindsides all EDR solutions and any protection the enterprise expects from their cybersecurity solution.
How does deterministic protection technology protect against ransomware attacks?
As explained above, attackers are looking to leverage unpatched or undisclosed vulnerabilities in internet-facing production applications. Upon gaining the ability to execute their malicious code (as shown in the righthand side of the diagram below), the attacker has effectively achieved Stage 4 of the kill chain. If the attacker crosses Stage 7, they will be unstoppable if conventional security solutions are used for protection.
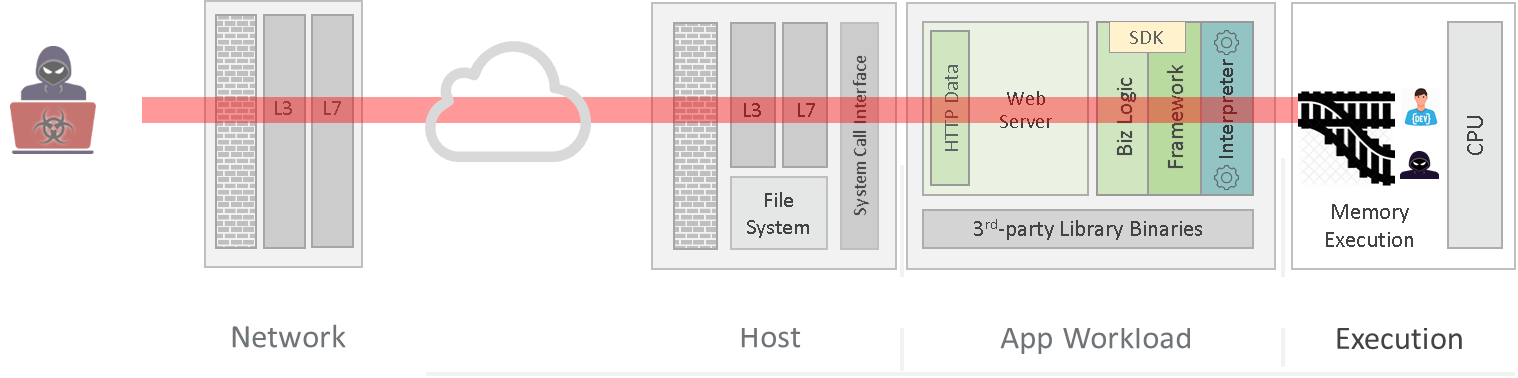 Image created by Satya Gupta, Virsec
Image created by Satya Gupta, VirsecDeterministic protection (DP) technology works silently in memory, similar to how GPS guides a driver through their travels.
The driver starts by putting an address into their GPS. The GPS responds by creating an intended navigation map for their journey. As the driver starts to travel to their destination, the GPS ensures that the driver stays on course. However, when the driver deviates, the GPS instantly alerts them that they are off course.
DP technology leverages the same principle. As a known application code loads in memory, it creates an application provider intent map (APIM) just like GPS loads an intended navigation map. During the lifetime of the application, DP technology tracks the application’s execution against the APIM. If under the influence of the attacker, the application deviates from its APIM (as shown in the figure above) and DP technology promptly engages a pre-configured protection action.
As a result, a ransomware attack never progresses past Stage 4 and an enterprise no longer needs to keep looking over their shoulder, even if their applications are riddled with vulnerabilities.
This article originally ran in Today’s Cybersecurity Leader, a monthly cybersecurity-focused eNewsletter for security end users, brought to you by Security magazine. Subscribe here.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!









