Twitch suffers massive data breach

Image courtesy of Twitch
American livestreaming service Twitch has been hit by a massive leak after an anonymous hacker posted a torrent file containing a vast amount of data for the public to access.
In September 2021, the service, operated by Twitch Interactive, a subsidiary of Amazon.com, Inc., had approximately 8.07 million active streamers.
According to a report by VGC, the hacker posted a 125GB torrent link to 4chan on Wednesday, reportedly leaking “the entirety” of Twitch’s source code along with creator payout reports from 2019, mobile, desktop and console Twitch clients, proprietary services, and even “an unreleased Steam competitor, codenamed Vapor, from Amazon Game Studios.”
VGC verified that the files mentioned on 4chan are publicly available to download. An anonymous company also confirmed that the data is legitimate, including source codes.
Twitch later confirmed the authenticity of the breach, stating, “Our teams are working with urgency to understand the extent of this. We will update the community as soon as additional information is available. Thank you for bearing with us.”
The leaked data reportedly includes:
- The entirety of Twitch’s source code with comment history “going back to its early beginnings.”
- Creator payout reports from 2019
- Mobile, desktop and console Twitch clients
- Proprietary SDKs and internal AWS services used by Twitch
- “Every other property that Twitch owns,” including IGDB and CurseForge
- An unreleased Steam competitor, codenamed Vapor, from Amazon Game Studios
- Twitch internal ‘red teaming’ tools (designed to improve security by having staff pretend to be hackers)
James Chappell, Co-Founder & Chief Innovation Officer at Digital Shadows, a San Francisco-based provider of digital risk protection solutions, explains, “A post made on 4Chan pointed to a 128Gb torrent containing data that appears to have been acquired from one of Twitch’s internal GitHub repositories. The leaked data was made available through torrents shared as magnet links. The data set appears to be comprehensive. It has also been labeled as a “part 1,” which suggests that there is more to come. While user data does not currently appear to be in the archive, users on the forum are speculating as to what may follow.”
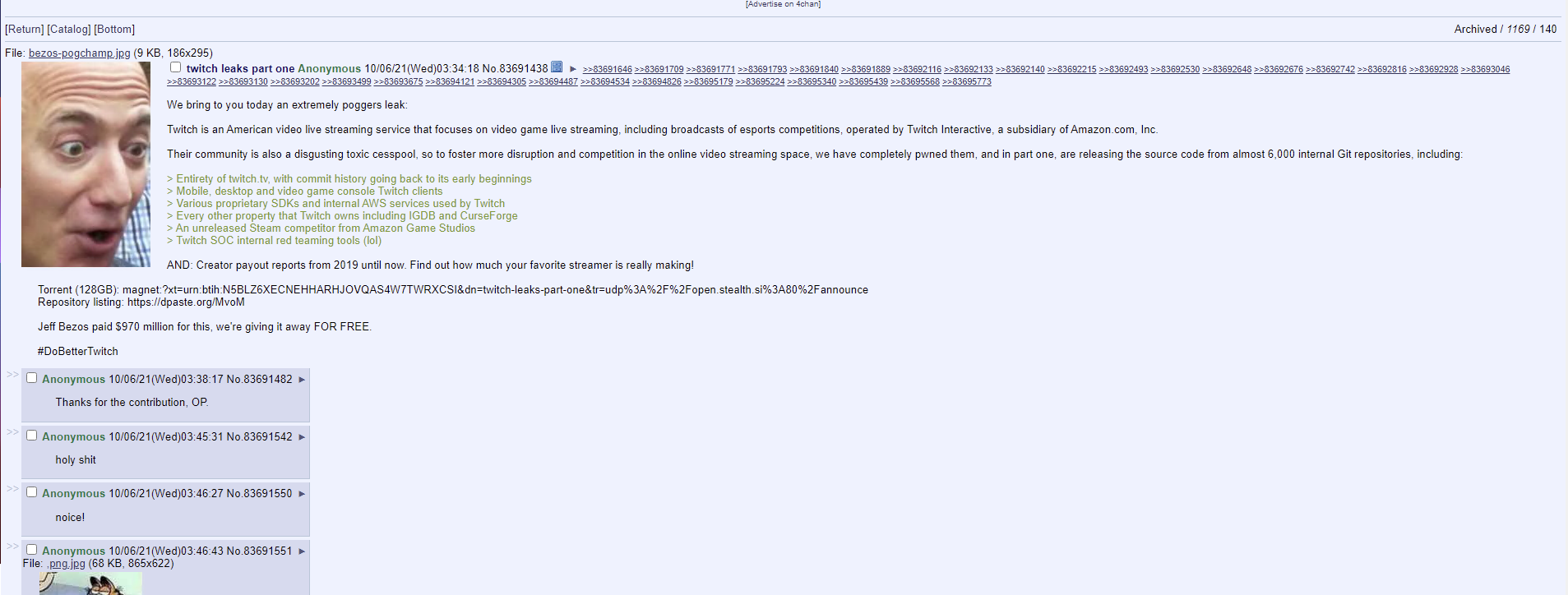
Image courtesy of Digital Shadows
Chappell adds, “There appears to be evidence that the original files came from an internal GitHub server, git-aws.internal.justin.tv, was at least part of the breach. Justin.tv was the name of a company that eventually transformed into Twitch. It rebranded as Twitch in 2011 - so this looks like a long-standing piece of infrastructure.”
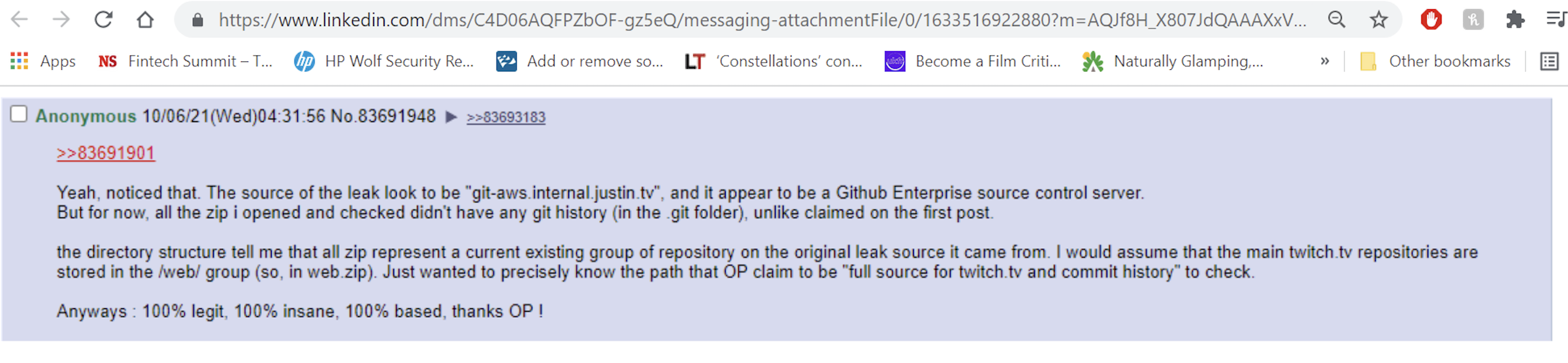
Image courtesy of Digital Shadows
“We know that streamers will be concerned about the impact of their streaming revenues being made public given that they rely on donations from fans,” Chappell says. “The Twitch security team’s details have been leaked alongside this first dump. Currently, users on 4chan seem to be crowdsourcing the analysis of what appears in this dump, so expect more details to drop throughout the day.”
Commenting on the news, Archie Agarwal, Founder and CEO at ThreatModeler, a Jersey City, N.J.-based automated threat modeling provider, says, “Reading of a data breach that includes the entire source-code including unreleased software, SDKs, financial reports and internal red-teaming tools will send a shudder down any hardened infosec professional. This is as bad as it could possibly be.”
The first question on everyone’s mind has to be: How on earth did someone exfiltrate 125GB of the most sensitive data imaginable without tripping a single alarm, Agarwal says. “There’s going to be some very hard questions asked internally. Although it appears a direct attack against Twitch only rather than users at first glance, it is almost guaranteed that user information will have been swept up in this breach. Users will have to take the usual precautions of changing their account credentials and make sure they don’t use the same combination of credentials to access other services online.”
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




