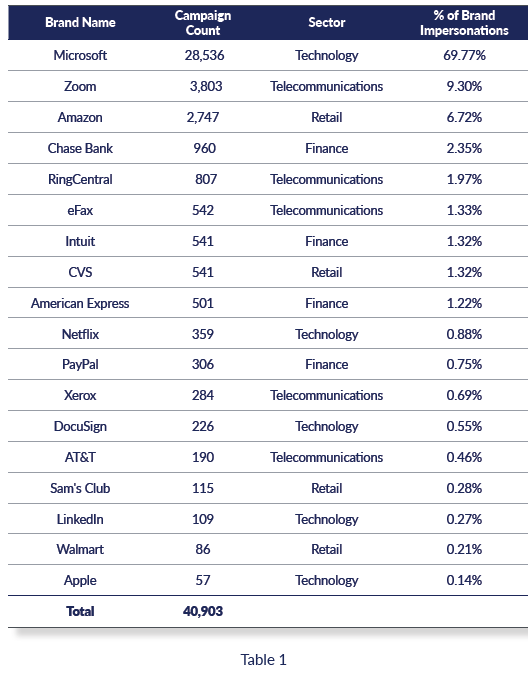
The top 25 most phished brands

INKY processed 656,954,951 emails in 2020. From this data, they ranked the top 25 most-phished brands during 2020. In round numbers, that’s two-thirds of a billion.
Within this pool, Inky found 4,874,096 phishing campaigns. Of those phishing campaigns, 591,293 of them were brand impersonations. Out of the brand-impersonation group, INKY found 40,903 unique campaigns, the total shown in Table 1. A single campaign is defined as being from the same sender domain and authentication source and having roughly the same text, links, and attachments. One campaign can represent hundreds or even thousands of emails, which may be vanilla (only the recipient is varied) or dynamic (customized per target via clever software).
Roger Kay, VP Security Strategy, INKY, says, "Phishers focused their efforts to target brands that enable WFH. When Video conferencing platforms (Apple FaceTime, Microsoft Teams, Cisco WebEx, RingCentral Meetings, Zoom, and Skype) replaced in-person collaboration, impersonations of these brands significantly increased. Common phishing lures are fake meeting invites, voicemails, and account verification emails.
He also explains that phishers are relying on zero day attacks to easily evade existing solutions. "Legitimate platforms and services are abused to launder malicious links and malware. An example is the use of SLK attachments in phishing emails. It’s a real Microsoft file format that’s modified to download and install remote access tools and ransomware. Malicious links and malware are hosted on cloud sharing sites (Microsoft SharePoint, Microsoft Forms, Microsoft OneNote, Google Drive, Google Docs, and Canva) because some solutions view these sites as safe even if it’s abused and used by phishers."
Kay adds, "Phishers will target the vaccine supply chain since there is an effort to vaccinate millions of people. Federal, state, and local governments are great targets since they are the authority of vaccine distribution. Insurance companies and pharmacies are also targeted because they are necessary components to get vaccinated."
For the full report, please visit https://www.inky.com/the-top-25-most-phished-brands
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!




