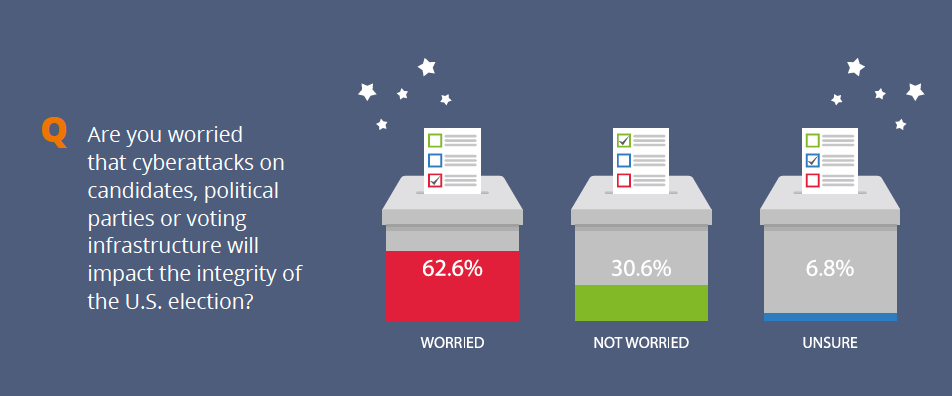
63% of government workers are worried that cyberattacks will impact the integrity of the upcoming US election

Sixty-three percent of government workers say they are worried that cyberattacks on candidates, political parties, and voting infrastructure will impact the integrity of the upcoming U.S. election, according to the Government & Election Cybersecurity Threat Index released by Morphisec, provider of Advanced Threat Prevention. In addition, more than 3-in-4 government workers (77%) believe that states and local governments need more federal funding to protect voting infrastructure better.
As Morphisec works with DHS to protect critical infrastructure and supports local governments with improving their cyber defenses against advanced threats, it surveyed 500 federal and local government employees across the U.S. in September 2020 to explore how government employees perceive current cyber threats. These government employees included law enforcement, administrative workers, librarians, and even postal workers. Of those surveyed, 31% worked within the federal government, and 69% worked within local governments.
With the U.S. presidential election just weeks away, the entire country is on high alert for cyberattacks, particularly those carried out by sophisticated nation-states or state-sponsored attackers determined to spread disinformation, disrupt national voting systems, or disable critical infrastructures. While it’s rare for voting equipment to be connected to the internet, government employees are concerned that both cyberattacks and the spread of information could undermine the election's integrity.
Furthermore, with COVID-19 creating the need for mail-in voting, there is the worry that attackers could utilize advanced malware attacks, such as the recently discovered Trickbot/Emotet variant, to undermine or disable mail-in ballot processing. That recent global campaign was successful in breaching France’s court system. The pandemic is also forcing 42% of government employees to continue working remotely, further complicating cybersecurity defenses and increasing attack surfaces during this critical period.
Additional highlights from Morphisec’s Government & Election Cybersecurity Threat Index:
- Nearly 1-in-4 (23%) government employees believe federal and local governments are “not at all prepared” to secure voting infrastructure.
- Despite the worry of voting infrastructure being breached, 62% of government workers say the more significant threat to the upcoming U.S. election is nation-states spreading disinformation online.
- When it comes to which nation-states government workers are worried about orchestrating cyber threats from during the election, Russia leads the list (50%).
- Of government employees currently working from home during the pandemic, 66% say they are using antivirus protection, 60% say they are using a VPN, and 55% utilize encryption methods.
- Almost a quarter (24%) of government workers say their department has previously experienced a cyber attack.
“Federal and especially local government employees are right to be worried about cyberattacks as we head towards election day,” said Andrew Homer, VP of Security Strategy at Morphisec. “Local municipalities are often underfunded, short-staffed and lack even the most basic cybersecurity protocols, meaning they’re readily vulnerable and will be in attackers crosshairs as we approach November 3. Furthermore, while it's encouraging to see many government workers — forced remote by COVID — using antivirus and VPNs, they remain targets for attacks that bypass traditional detection solutions. Proactive solutions, such as moving target defense, which is designed to automatically block and lock down evasive threats, is needed to guard against these sophisticated global threats.”
Download the full Morphisec Government & Election Cybersecurity Threat Index here.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





