National Security Agency Releases Cybersecurity Guidance for Remote Workers

The U.S. National Security Agency (NSA) has released Selecting and Safely Using Collaboration Services for Telework, cybersecurity guidance which contains a snapshot of current, commercially-available collaboration tools available for use, along with a list of security criteria to consider when selecting which capability to leverage. In addition, the guidance contains a high-level security assessment of how each capability measures up against the defined security criteria, which can be used to more quickly identify the risks and features associated with each tool.
The primary audience for this guidance are U.S. Government employees and military service members engaging in telework, especially telework employing personally owned devices such as smartphones and home computers.
Collaboration services vary widely in the cybersecurity functionality and assurance that they offer. By using the objective criteria detailed below, government employees and organizations can make more informed decisions about which collaboration services meet their particular needs. By following the practical guidelines, users can draw down their risk exposure and become harder targets for malicious threat actors.
Note that individual departments and agencies may provide specific services or issue specific direction for their teleworkers.
Criteria to Consider When Selecting a Collaboration Service
- Does the service implement end-to-end encryption?
- Are strong, well-known, testable encryption standards used?
- Is multi-factor authentication (MFA) used to validate users’ identities?
- Can users see and control who connects to collaboration sessions?
- Does the service privacy policy allow the vendor to share data with third parties or affiliates?
- Do users have the ability to securely delete data from the service and its repositories as needed?
- Has the collaboration service’s source code been shared publicly (e.g. open source)?
- Has the service and/or app been reviewed or certified for use by a security-focused nationally recognized or government body?
- Is the service developed and/or hosted under the jurisdiction of a government with laws that could jeopardize USG official use?
Using Collaboration Services Securely
- If possible, use government furnished equipment (GFE) that is managed and intended for government use only and secure services designed for government use.
- If you download a collaboration service app, be sure you know where it came from.
- Ensure that encryption is enabled when initiating a collaboration session.
- Use the most secure means possible for meeting invitations.
- Verify that only intended invitees are participating before beginning, and throughout, each session.
- Ensure that any information shared is appropriate for the participants.
- Ensure that your physical environment does not provide unintentional access to voice, video, or data during collaboration sessions.
Assessment of Common Collaboration Services Against the Criteria
The table below presents an initial assessment of how available commercial collaboration services satisfy NSA security criteria.
According to the NSA, the selection of services for this initial assessment was driven by inquiries and usage from across NSA's national security customer base; this is not a comprehensive list of services or possible criteria. NSA analysts gathered factual material from published company literature and product specifications, supplemented by other openly published analyses and basic hands-on technical observation. No formal testing was performed on products or services for this analysis. These assessment findings are meant to serve as an input for government employees and organizations. Users of these services must exercise judgment when choosing a service for their particular mission telework needs, says the NSA.
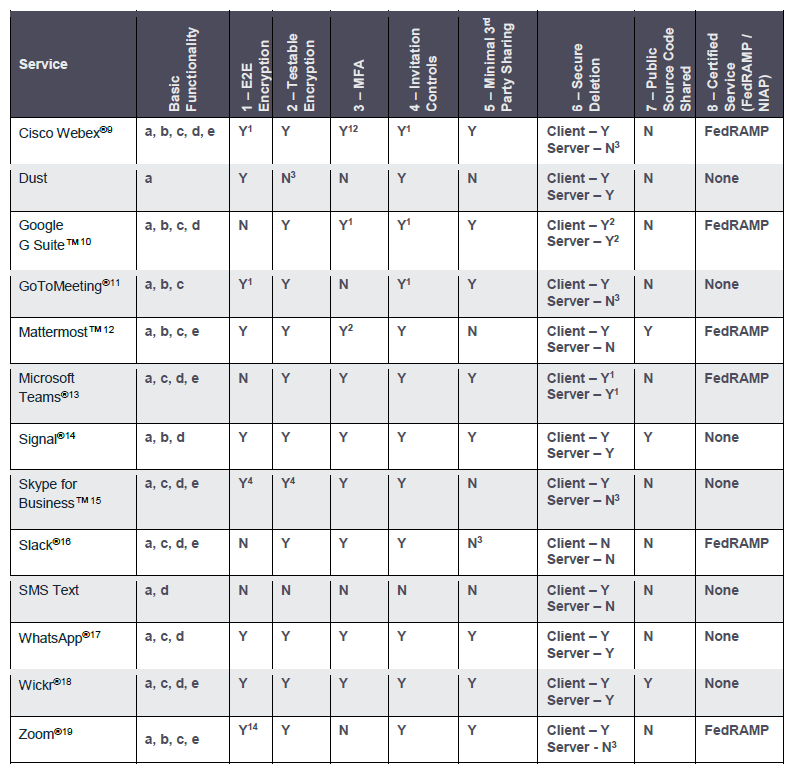
Legend: Y = Yes, N = No; (a) text chat, (b) voice conferencing, (c) video conferencing, (d) file sharing, (e) screen sharing.
1 Configurable
2 Free Version - N
3 No Published Details
4 Partial
An extended version of Selecting and Safely Using Collaboration Services for Telework is also available.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!






