Payment Data Breach Risks Increase as New Payment Methods Emerge
Fifty-four percent of respondents in The Global Study on the State of Payment Data Security, conducted by the Ponemon Institute on behalf of Gemalto, have had a security or data breach involving payment data an average of four times in the past two years. Enterprises’ steps to improve data security in new payment methods continues to grow more and more critical, as the acceptance of methods such as mobile payments, contactless payments and e-wallets is expected to double from nine percent of all payments to 18 percent in the next two years.
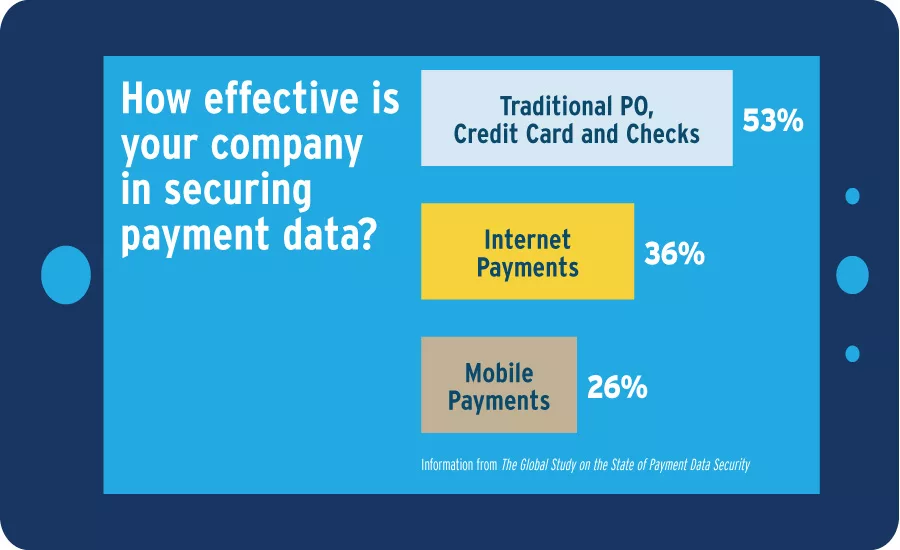
The majority of the global companies represented in this study plan to accept next-generation payment platforms such as Apple Pay, but do not believe existing security protocols are capable of supporting these platforms. In addition, the majority of respondents do not believe security personnel and technologies are sufficient to effectively protect payment data.
Part of the problem is that 55 percent of enterprises do not know where their payment data is stored or located, the study shows, and this is considered either a very high risk (by 42 percent of respondents) or high risk (38 percent of respondents).
Only 46 percent of respondents said the protection of payment data is among the top five security priorities for their companies, and only 31 percent say their organization allocates enough resources to the task.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





