Easing Migration and Saving Money with Ethernet Adapters
The migration from analog infrastructure to networked systems continues to gain traction at a rapid pace given all the inherent benefits networked technology provides for video surveillance and security applications. However, there are costs involved, and they can be significant, especially if the move to networked infrastructure requires the removal of existing wiring and the installation of new Ethernet cabling. One of the greatest challenges involves the distribution of power to various edge devices. Here’s where PoE technology has helped to increase the trend towards networked systems.
It’s no surprise that more and more system designers and installers are realizing the advantages of Power over Ethernet (PoE). First used for voice-over-IP telephones, PoE technology has gained popularity as a means of introducing power safely to other network devices via the same CAT5 or higher cable that transmits Ethernet data. In security and surveillance systems, power up to 15.4 watts can be supplied to network cameras and other devices using the original IEEE 802.3af PoE standard. The newer IEEE 802.3at standard, also known as PoE+, supplies up to 25.5 watts to accessories like power heaters and blowers and infrared illuminators, among other devices.
In just a few years, PoE has already redefined how security professionals design and deploy systems. Rather than using standard-type power supplies, integrators are increasingly employing PoE network switches or incorporating PoE midspan devices, which inject power into an Ethernet cable after it leaves the switch and before it reaches the network device. This is an ideal solution given that Ethernet cabling is already in place, or planned for a new installation, but the edge devices sitting on the network also need to have the ability to accommodate PoE, and many IP cameras, access control and related devices installed and on the market today have PoE functionality built into them. Then there is the issue of legacy coax infrastructure which was not initially intended to accommodate IP devices, let alone PoE.
Ethernet Adapters Open the Network Gateway
Here’s where the development of new PoE Ethernet Adapters solve the issue of deploying IP devices using coax cabling, and now make virtually any edge device PoE capable. The fact is there are literally millions of existing analog systems installed today that use RG59 and 18/2 cabling infrastructure for video and power. By employing IP-over-coax Ethernet adapters, it is possible to upgrade legacy systems from analog to IP without having to rewire a facility. In addition to realizing substantial cost savings, new solutions like Altronix new eBridgePlus Ethernet over Coax/PoE Adapters also enable PoE to be sent over coax cabling resulting in even higher cost savings.
Let's take a closer look at how using Ethernet over Coax/PoE Adapters can save installation costs. The accompanying chart shows an approximated cost comparison based on list pricing and average installation charges typical of a large integrator. This example also excludes costs for recording equipment, switches, cameras, camera mounts, etc.
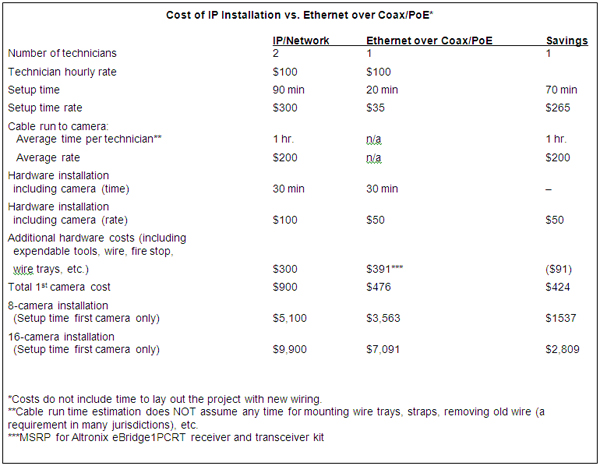
It is clear to see the savings using IP-over-coax Ethernet Adapters and existing coax infrastructure. They enable transmission of IP video, data and power over existing coax with high cost efficiency and signal integrity, and they minimize installation costs. This latest product innovation will undoubtedly continue to fuel the installation of networked systems by providing users with the perfect combination of cost-efficiency and performance they need to improve their video surveillance and security operations.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!





