How Cloud Computing Changes Risk Management
It wasn’t long ago that “cloud computing” was a marketing term being thrown around. And now? There’s been a marked shift towards cloud-based services. Research firm Gartner recently predicted that the market will grow 19.6 percent to $109 billion by the end of this year.
The advantages that it can offer an enterprise are numerous, including the creation of business efficiencies, value, business flexibility and scalability and more.
Yet, we’re still learning about this great new tool, about how it’s perceived, used and understood. For example, there are some people who think that cloud computing is related to the weather, says a survey by Wakefield Research. The survey found that there is a significant disconnect between what people know, what they pretend to know and what they actually understand when it comes to cloud computing.
The survey, which was commissioned by Citrix, showed that while the cloud is widely used, it is still misunderstood. For example, 51 percent of respondents believe stormy weather can interfere with cloud computing. Nearly one-third see the cloud as a thing of the future, yet 97 percent are actually using cloud services today through online shopping, banking, social networking and file sharing. Despite the confusion, 59 percent said they believe the “workplace of the future” will exist entirely in the cloud.
The savings by moving access control to the cloud have been substantial for Barefoot Resort complex in Myrtle Beach, S.C. |
Meanwhile, 54 percent of respondents claim to never use cloud computing. However, 65 percent bank online, 63 percent shop online, 58 percent use social networking sites such as Facebook or Twitter, 45 percent have played online games, 29 percent store photos online, 22 percent store music or videos online and 19 percent use online file sharing. All of these services are cloud-based. Even when people don’t think they’re using the cloud, they really are, the survey revealed.
The survey also showed that 68 percent of respondents said they recognize the economic benefits of cloud computing after learning more about the cloud. The most recognized benefits are that the cloud helps people by lowering costs (35 percent), spurs small-business growth (32 percent) and boosts customer engagement for businesses (35 percent).
The fact is that many of us use cloud computing every day, with sites like Facebook, Netflix or Gmail. Photos and videos are stored on Facebook servers, which are retrieved from any computer with an Internet connection.
You can store documents, photos or videos online with services like Google Drive, Microsoft SkyDrive or Amazon Cloud Drive.
Apple’s iCloud, Dropbox and Google Drive can sync files between your devices and the cloud. If iCloud is enabled and you take a photo with your iPhone, it will automatically show up on your iPad. For some, that’s a beautiful thing.
“Virtually every enterprise, even it only has 10 employees, is using cloud computing, but some don’t realize it,” adds John Howie, COO, of the Cloud Security Alliance (CSA). “For example, non-core applications like payroll may be in the cloud. And employees are using the cloud with Facebook or Twitter. The key for a security executive is to write the policies and procedures necessary to keep their organization’s cloud secure. You can never be as secure as Google – they have far more money, and they will run better shops than you can do yourself. But I predict that with the correct security procedures in place, that ‘security’ won’t rank in the top five concerns with the cloud in the next few years.”
For now, security is a concern. Like any business concept, it comes with risks. It is not a perfect solution; huge things can go wrong. Case in point, although on a small scale: last month Wired senior writer Mat Honan reported that because of what were initially fraudulent phone calls, several of his online accounts were breached, including his iCloud account. Honan’s iPhone, iPad and MacBook were remotely wiped because the hacker had access to his iCloud account.
So what is a security executive to do? According to Larry Ponemon, chairman and founder of the Ponemon Institute: focus on a private cloud computing effort that makes the most business sense.
“The cloud potentially can create a new IT infrastructure…and the cloud is changing,” Poneman says. “Early on it was software as a service and that was great, but now we see new services emerging. And there are things in the cloud that are attractive to small organizations. For example, a cloud based application in a smaller organization can help to level things out a bit. A small organization can get some services it needs without incurring huge investments.”
The cloud solution that makes business sense, Poneman says, definitely needs to involve the security executive in every enterprise. “Unfortunately, many cloud decisions in an organization are made by those who are not involved in security, such as sales and marketing. And by making those choices they can put their organization in jeopardy,” he notes. “For example, with Dropbox, it’s a great tool, but what happens if that data is not secure? It’s a train moving down the tracks fast, and we see organizations who don’t consult with their security team. So using the cloud can be a tradeoff between ease and convenience and good security. And we need both.”
The first step to take in the “cloud”process, says Poneman, is the awareness step. Even though you might not control the use of it in your organization, you need to find out what applications employees are using and determine whether any data from your company in those environments is not secure. Second, determine which applications pose the greatest risk. Do a search, talk to colleagues and find out which products are secure. And look to the cloud as a positive business tool, instead of negative, he suggests. Embrace it. “The bottom line is that you can’t stop it, you can’t tell employees to stop using it. It’s all about mitigating the risk.”
“Make sure that it makes business sense,” Howie of CSA adds. “Some companies may not see the cost savings right away. And that be due to the fact that they are not using cloud computing properly. Some companies are just using it to virtualize their existing data center. Some are creating a virtual server and are finding the cost savings are not what they thought it would be. However, when it comes to Software as a Service applications, the savings are there for most organizations. But look for the solution that’s best for you.”
Business Efficiencies
The savings by moving access control to the cloud have been substantial for Barefoot Resort complex in Myrtle Beach, S.C. The organization is using a cloud-based solution to improve safety and security. The 2,300-acre resort has more than 700 single-family homes and five condominium developments totaling 1,000 units.
Years ago, video surveillance was installed at one of the Barefoot property’s clubhouses. At that time, all of the Barefoot communities under Omni Management relied on standard lock and key and telephone access systems for common amenities such as clubhouses and pools, as well as residential homes and condos. Pam Basilicato, Community Association Manager at Omni, has begun using a cloud-based access control system to manage 24 access points across five properties.
Basilicato has created groups for residents of each of the separate properties, for vendors who need 24/7 access, for management, a host of other vendors, and for those working on temporary projects within the resort. Each group is programmed for specific day, time and location access, based on its needs. “For temporary projects, I can activate a card or a fob corresponding just to the length of the project,” she says. Omni controls access for more 3,000 residents, vendors, staff and temporary visitors to clubhouses, pools and residential buildings.
In addition to standard access control, Basilicato and her team run activity log reports to see who is going where after hours and identifying instances when residents are attempting access where and when they should not be doing so. “If I’m told someone is in the pool at 1:00 a.m., I can see whose cards were used or were attempted to be used. The system is very user-friendly, and it’s accurate; I love it. It gives me all the info I need to take proper, informed action. I’ve used the reports function quite a bit,” Basilicato said.
Regis University in Denver, Colo., is using a cloud-based system to manage security at its new CyberSecurity Education Center at the University’s Denver Technology Center campus.
When the University began building its new CyberSecurity Education Center a few years ago, its staff knew the facilities would be much more than just a classroom and that there would be a lot of expensive equipment onsite. Also as time went on, more visitors would be utilizing the facilities, in addition to the adult students. “Clearly, we had to have enhanced control over the doors at the center and who was coming into and out of the classrooms and meeting rooms,” explains Dan Likarish, Director of the Center on Information Assurance Studies at Regis University.
Regis’ campus at the Denver Technology Center is a public access facility, located adjacent to a major highway and accessible by light rail. Easy access also means that anyone can be walking around the campus. In addition, the Center has made a substantial investment in the equipment they provide in their classrooms and labs. The Center caters to an adult student body so classes are held at night, which compounds security challenges.
“With Brivo, we have what I call constant vigilance monitoring, and that reduces our worry factor,” says Likarish. “Add to this that our students get the practical experience of working with this system in a higher security environment, and that’s a positive experience all around.” All students earning their master’s degree in information assurance do a walk-through of the University’s security systems, and that’s when they are introduced to a Brivo ACS WebService. “Utilizing the system, we demonstrate the one, two and three factor combinations of identification – card, biometrics or fingerprint reader and PIN. Physical security is part of our curriculum, so we used this system to turn it into a lab exercise. We explore not only the physical devices, but also what happens in the event of a power failure, what is the door device to webserver connection, why use PoE, what is the support and maintenance model, and many other aspects.”
Another purpose for the Center is to provide education for first responders at the tribal, local, state and federal levels (the FBI, FEMA and Interior are future, prospective customers). So, the University has many different groups coming through and recently was preparing to receive 70 new visitors in just a few days. “The system gives us the flexibility to control our rooms for our many different needs, and those needs are only going to expand as we receive more and more visitors, hold trainings and cyber competitions, and so on,” says Likarish.
This article was previously published in the print magazine as "Cloud Computing’s Potential."
Managing The Risk |
|
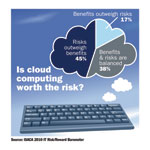
What do the majority of IT experts think about cloud computing? According to a survey by ISACA, 45 percent of IT professionals believe the risk outweighs the benefits. According to ISACA Vice President Robert Stroud, “The cloud represents a major change in how computing resources are utilized, so it’s not surprising that IT professionals have concerns about risk vs. reward.” Past studies by Forrester Research and ISACA have revealed that the main driver of IT-related risk management is the need to comply with industry and governmental regulations, with avoiding negative incidents. Therefore, cloud computing proponents, such as the Cloud Security Alliance, who want to facilitate the widespread adoption of cloud services, can use industry regulation as a way to do so. |
Cloud Security Beyond IT |
||
If employees walked into your HR department and removed and shared files with others within and outside your company, corporate security would probably be asked to investigate and identify ways to prevent this from happening. You would incorporate an identity management, access control and audit trail to gain transparency about who accesses files and how they are used. In the era of the cloud, your organization is probably storing files in Google Docs or a similar service, including sensitive information and intellectual property files, without any identification or audit trail regarding who accesses them or where they go. But because it is considered an “IT” issue, security is often excluded from the process until it is too late. It shouldn’t be. The HR file cabinet has the same physical security risks in the cloud as it did in an office building. At AMAG Pharmaceuticals, Nathan McBride, Vice President, had to audit the access and use of 780,000 documents stored in Google Docs by his company. “We had to do it for two primary reasons, both focused around compliance,” he explains. “First and foremost is the need to remain compliant under Sarbanes Oxley 404 requirements. The second is to be able to withstand the scrutiny of a MA201 audit. Either of these audits, if failed, can have financial detrimental impacts on a company. We needed a major document management tool to apply best practices, ensure compliance and audit activity,” says McBride. McBride found a CloudLock solution as a way to view the usage and sharing of documents by AMAG employees, as well as to terminate permissions after an agreement or relationship ended. It is not a prevention tool, but an audit tool that had several benefits for AMAG, McBride says. “The ROI is measurable. The cost is low, and it pays for itself. The ability to transfer documents when an employee leaves the company saves significant time and money for our department. It also eliminates policy violations by enabling us to observe the use of the document system,” he says. McBride says he views Google Docs as business enabler, but there would be uncertain risks without transparency were it not for the tool. As organizations work to identify risks to assets and IP, SaaS or Cloud-based document storage risk needs to be mitigated and managed as a business problem, not an IT or security issue, he says. |
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!