Career Intelligence
Supply chain security: A key career skill
Today's security executive must be conversant in key aspects of their organization's supply chain resiliency.
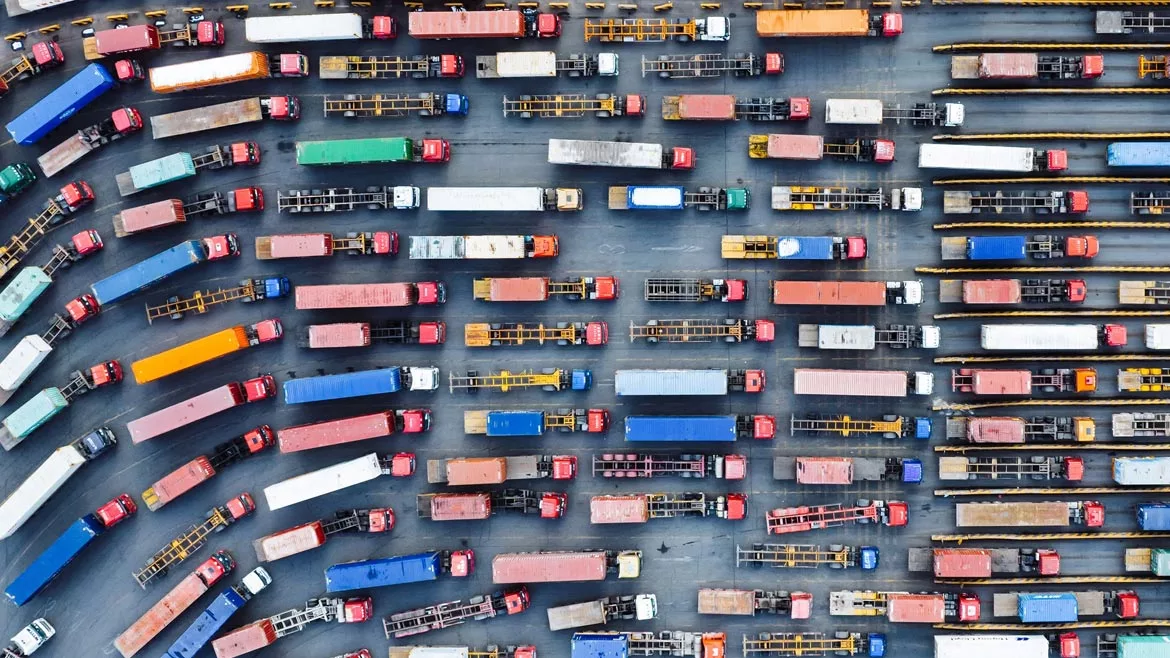
NAerialPerspective Works / E+ via Getty Images
In previous articles we have discussed the fact that supply chain security was sometimes part of the corporate security function but at times was a separate activity setting under operations or production. Whatever the organization structure, having a deep understanding of supply chain security risks is highly beneficial for your career today more than ever. Organizational supply chain risks are influenced by a mix of geopolitical tensions, evolving technology and broader economic shifts. It is directly tied to their risk resiliency programs that we are seeing more and more corporate security departments either lead or at least be an active participant in.
Recent news events have highlighted the consequences of not having examined, validated, executed and assured supply chain security. Today’s failures by your suppliers and theirs will impact your ability to support your customers. The perpetrators may be criminal organizations, employees or contractors and state sponsored operations.
Below is a list that security functions should be conversant in and able to evaluate as a part of a risk probability, impact and program implementation discussions with leadership.
Cybersecurity & technology threats
- Attackers are increasingly targeting third party vendors to gain entry to larger corporations. These breaches can result in the theft of intellectual property, customer data or critical business information.
- Ransomware may compromise systems essential for supply chain operations, bringing manufacturing, logistics, or distribution to a halt.
- Data Integrity, such as modifying shipment information or product specifications, can disrupt supply chain operations.
- The increased reliance on the Internet of Things (IoT) devices and artificial intelligence (AI) in supply chains introduces new cyber and operational risks.
- The growing inclusion of blockchain solutions can introduce new vulnerabilities around data integrity.
Geopolitical risks
- Trade wars and sanctions can lead to sudden tariffs or restrictions, forcing businesses to pivot their supply chains, sometimes at a higher cost.
- Regional Instabilities, political unrest, civil conflicts or regime changes in key manufacturing hubs can disrupt production and transportation.
- Nationalization or regulatory pressures where governments may impose stricter regulations on foreign corporations, may interfere with access to local suppliers or disrupt existing supply chain networks.
Medical / health related disruptions
- SARS, MERS and COVID19 pandemics provided a window into how health crisis could disrupt global supply chains. Recurrences or new pandemics (even on a regional scale) can lead to shutdowns, slowdowns or restrictions on movement that disrupt production and delivery timelines.
- Health related labor shortages,risks and restrictions can cause labor shortages in critical sectors such as manufacturing, shipping and logistics.
Natural disasters and significant climate events
- Extreme weather events and other natural disasters can destroy infrastructure, delay shipments, halt production and may provide opportunities for malicious actors.
- As the frequency of extreme weather events increases, long term supply chain planning becomes more difficult, especially for sectors reliant on agriculture or natural resources.
Supplier risk management
- Reliance on Single or Limited Suppliers: Many companies still rely on a few key suppliers, which increases their vulnerability. If one supplier fails, it could lead to disruptions across the entire production cycle.
- Lack of Visibility and Transparency: Many corporations struggle with visibility into their supply chain, especially at lower tier suppliers. This makes early detection of problems critical.
Counterfeit and fraudulent products
- As global supply chains grow more complex, so does the risk of counterfeit components or products entering the supply chain.
- Products, critical materials, components and parts being diverted or stolen in the supply chain or being replaced with substandard or fraudulent items are great risks.
Compliance and regulatory risks
- Regulations surrounding customs, tariffs and compliance laws increasingly have security related components that, if not effectively implemented, can cause delays or increased costs for goods in transit.
- Emerging environmental, social, and governance (ESG) regulations are also an area that security departments have become an integral part of in addition to compliance programs to avoid reputational damage, fines or loss of customer trust.
It is also critical that a security executive understand the various business impact factors so that you can more effectively communicate with your stakeholder on alignment and value of your programs. Some of the business impacts that you need to understand and be knowledgeable of are:
Logistics and transportation vulnerabilities
- Port Congestion
- Shortage of Shipping Containers
- Transportation Strikes
Economic risks
- Global Inflation
- Supplier Financial Instability
Sustainability and resource scarcity
- Resource Depletion
- Sustainability Pressures
Today’s security executive must be conversant in these key aspects of your organization’s supply chain resiliency, you must proactively assess and monitor these risks to aid in ensuring supply chains capable of withstanding the evolving landscape of security threats.
Looking for a reprint of this article?
From high-res PDFs to custom plaques, order your copy today!










